AWS Security Blog
Using AWS Firewall Manager and WAF to protect your web applications with master rules and application-specific rules
Jeff Barr’s blog post introducing AWS Firewall Manager describes how you can centrally manage a set of web application firewall rules to protect all the applications in an AWS Organization. This blog post will take you through the specific steps to implement firewall rules using both AWS Web Application Firewall (AWS WAF) and AWS Firewall Manager, including how to use a predefined set of AWS WAF rules like a master rule set that you can enforce on multiple resources.
If you haven’t used these services before, here’s a quick overview:
- AWS WAF is a web application firewall that lets you monitor the HTTP and HTTPS requests that are forwarded to Amazon CloudFront or to an Application Load Balancer. AWS WAF also lets you control access to your content. Based on conditions that you specify, such as the IP addresses from which requests originate or the values of query strings, CloudFront or an Application Load Balancer will respond to requests either with the requested content or with an HTTP 403 status code (Forbidden). You also can configure CloudFront to return a custom error page when a request is blocked.
- AWS Firewall Manager simplifies your AWS WAF administration and helps you enforce WAF rules on the resources across all the accounts in an AWS Organization by using AWS Config in the background. AWS Firewall Manager also enables you to selectively apply the rules to specific resources.
By using AWS Firewall Manager together with AWS WAF, you can enable developers to code WAF rules while still ensuring that all applications are protected by master rules defined by your organization’s security team. This strategy meets the needs of organizations using a DevOps model of development, where both the security team and the application development teams will build, manage, and deploy security rules. The architecture proposed in this post lets the security team create and enforce a master set of WAF rules using AWS Firewall Manager while still allowing developers to build and manage additional rules.
Customers use AWS WAF and AWS Firewall Manager to meet different requirements. One common scenario is to create different global sets of WAF rules in AWS Firewall Manager and apply these centrally managed rule sets to individual applications using AWS Firewall Manager policies. With AWS Firewall Manager policies, you can filter resources based on tags. Another common use case is to create AWS WAF rules in individual accounts and apply web access control lists (web ACLs) to protect specific resources by associating the application’s CloudFront distribution resource or the application’s Application Load Balancer.
However, with multiple customers adopting DevOps culture for software development, I’ll use this post to dive deep into a design pattern that enables developers to deploy and manage application-specific WAF rules to augment their existing security controls. This lets your organization’s InfoSec team create a master set of WAF rules using AWS Firewall Manager and enforce these rules across all applications, while enabling developers to build and manage additional rules in conjunction.
Prerequisites
AWS Firewall Manager has the following prerequisites:
- AWS Organizations: Your organization must be using AWS Organizations to manage your accounts, and All Features must be enabled. For more information, see Creating an Organization and Enabling All Features in Your Organization.
- A firewall administrator AWS Account: You must designate one of the AWS accounts in your organization as the administrator for AWS Firewall Manager. This gives the account permission to deploy AWS WAF rules across the organization.
- AWS Config: You must enable AWS Config for all of the accounts in your organization so that AWS Firewall Manager can detect newly created resources. To enable AWS Config for all of the accounts in your organization, you can use the Enable AWS Config template on the StackSets Sample Templates page. For more information, see Getting Started with AWS Config.
Architecture diagram
The following diagram gives an overview of the process for deploying WAF rules to different applications.
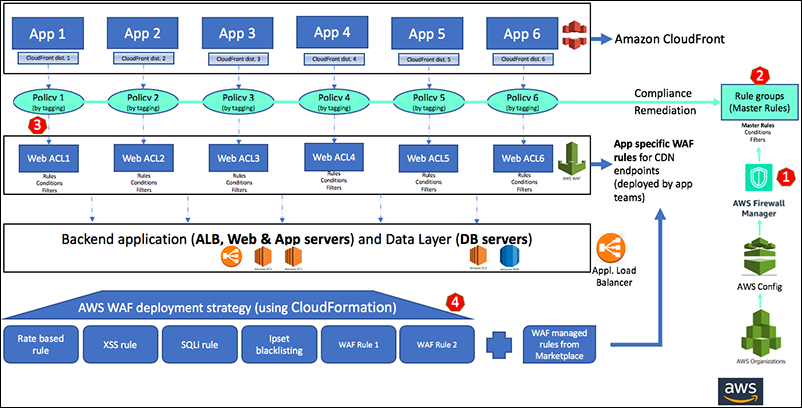
Figure 1: Architecture diagram
The diagram illustrates the following steps:
- Enable AWS Firewall Manager and designate the account owned by your security team as the AWS Firewall Manager administrator account.
- Create a rule group under AWS Firewall Manager. This is nothing but a logical grouping of WAF rules that you can add to a web ACL or an AWS Firewall Manager policy. You can either create or use an existing set of WAF rules as the master rule set.
- Under AWS Firewall Manager, create policies that can be applied to individual application resources (Application Load Balancer or CloudFront distributions) by mapping them to specific application name/value tags. The policies you create will result in the generation of individual new web ACLs in the backend for each policy.
- Application developers can further build more app-specific WAF rules on the web ACLs created in the previous step.
Deploying the solution
The following steps will walk you through the deployment details.
- From the AWS Management Console, select AWS WAF. You can either create your own set of master rules or import a master set of rules. For more information about how to import a pre-defined master set of rules, see the whitepaper Use AWS WAF to Mitigate OWASP’s Top 10 Web Application Vulnerabilities. You can also choose to use the AWS CloudFormation template mentioned in the AWS WAF Security Automations implementation guide. As another option, you can choose to import managed rules offered by partners on AWS Marketplace Rule Groups as the master set of rules.
- Under AWS Firewall Manager, select Rule groups, and then select Create rule group.
- Under Choose how you want to proceed, select Use existing rules for this rule group, and then select Next. If you choose to create your own rules, you can select Create rules and conditions for this rule group.

Figure 2: The “Use existing rules for this rule group” option
- Enter a name for your rule group. In my example, I’ve named my rule group “MasterRuleGroup.” Add each rule to your rule group by selecting Add another rule. After adding all of your rules, select the Create button to create the rule group.

Figure 3: Create a rule group
- Now, under AWS Firewall Manager, select Security Policies. You’ll create a new policy for each of the applications that you want to manage by selecting the Create policy button and following these steps:
- Select the option to Create an AWS Firewall Manager policy and add existing rule groups.
- Associate the policy to the rule group you named and created earlier, and then select Next. In my example, you can see that I’ve associated one of my policies (Policy1) with my rule group (MasterRuleGroup).

Figure 4: Associate the policy to the rule group
- On the following screen, select the box that says Select accounts to include/exclude from this policy, and then select the option to Include only these accounts in this policy. Add the corresponding accounts by selecting Add, then select the appropriate resource type to protect. Finally, select the checkbox for the option to Use tags to include/exclude resources (optional), select Include, and then add the application’s Name/Value tag.

Figure 5: Define the policy’s scope
- Repeat step five to create policies for all the applications that you want to manage, using each application’s corresponding application tags.
Each security policy creates a web ACL that is visible in the web ACLs list under AWS WAF. The policies appear with a unique ID starting with FMManagedWebACL:
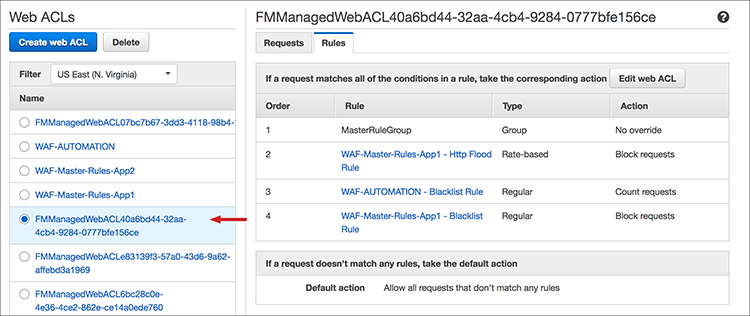
Figure 6: Look for IDs that begin with “FMManagedWebACL”
Each of these WAF web ACLs can be managed by your individual application teams. Developers can add up to nine WAF rules for various scenarios, such as cross-site scripting, SQL injections, and IP blacklisting, while still ensuring that their applications are protected by the master rules defined in the AWS Firewall Manager.
Additionally, master rules will be automatically reinstated if any of the application team members deletes the master rule group. Now, I want to take a moment here and highlight the importance of this feature. If you have a new developer who has taken up the responsibility of developing and managing the WAF rules and who mistakenly deletes the master rule group of type Group, AWS Firewall Manager in the backend will find that this rule has gone non-compliant and automatically remediate it by adding this rule back into the web ACL.
Conclusion
This blog post describes how you can create AWS Firewall Manager rules using the web console. You can also create these rules by using the command line interface (CLI), programmatically with the SDK, or by using AWS CloudFormation and other such scripting tools.
Using both AWS WAF and AWS Firewall Manager, you can create a deployment strategy that enables
developers to maintain a security mindset and begin coding WAF rules, while at the same time ensuring all applications are still protected by a set of WAF rules defined by your organization’s InfoSec team
If you have feedback about this blog post, submit comments in the Comments section below. If you have questions about this blog post, start a new thread on the AWS WAF forum or contact AWS Support.
Want more AWS Security news? Follow us on Twitter.