AWS Storage Blog
Learn how to use two important Amazon S3 security-features: Block Public Access and S3 Object Lock
Update (4/27/2023): Amazon S3 now automatically enables S3 Block Public Access and disables S3 access control lists (ACLs) for all new S3 buckets in all AWS Regions.
Amazon Simple Storage Service (Amazon S3) was AWS’ first Generally Available service when it launched on Pi Day in 2006, and in doing so created cloud storage. It quickly became one of the most important building blocks of AWS infrastructure. Today, S3 is used by millions of customers to store trillions of objects and many exabytes of data. One of the reasons S3 has been so successful is our focus on data security right from the beginning. We continuously invest to raise the bar on security for storage, and work with customers to meet ever-increasing security needs while holding true to our mission to keep storage simple. For example, you can use IAM policies to require the use of TLS encryption (HTTPS) for all S3 requests or to require the use of S3 Server-Side Encryption using keys from AWS Key Management Service (KMS). You can also establish a private connection from your Virtual Private Cloud (VPC) to S3 using VPC Endpoints, and attach a VPC Endpoint policy that permits access from that VPC only to whitelisted buckets. AWS CloudTrail can be enabled to provide an audit log for most S3 operations, and AWS Config Rules has 10 built-in rules to programmatically check S3 security configurations.
Today I want to mention two important security features of S3 that you might not have seen: S3 Block Public Access and S3 Object Lock.
S3 Block Public Access
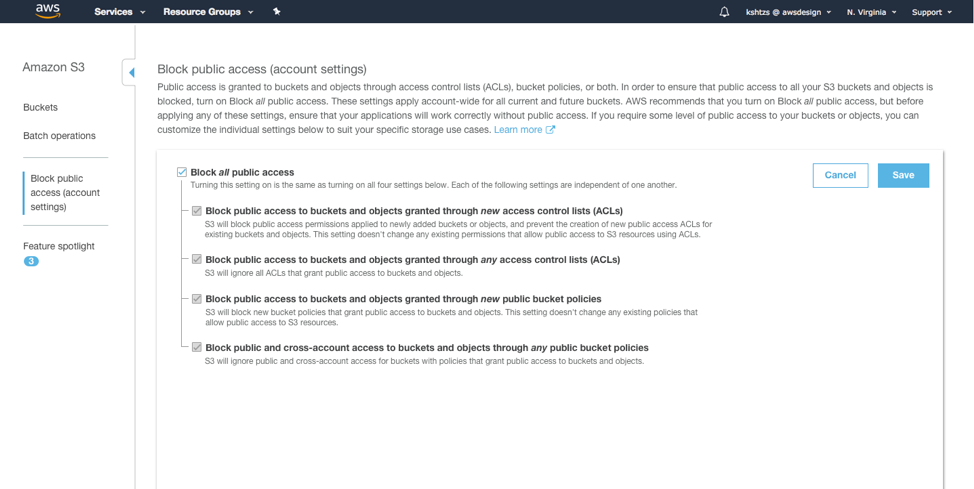
S3 Block Public Access provides controls across an entire AWS Account or at the individual S3 bucket level to ensure that objects never have public permissions. If an object is written to an AWS Account or S3 bucket with S3 Block Public Access enabled, and that object specifies any type of public permissions via ACL or policy, those public permissions are blocked. Block Public Access is a good second layer of protection to ensure that you don’t inadvertently grant broader access to objects than intended. If you’re not already using S3 Block Public Access today, I strongly encourage you to spend the 5-minutes it takes to implement it with a few clicks in the S3 console (see below). Alternatively, you can enable S3 Block Public Access via the AWS CLI, SDKs, or REST APIs. Detailed instructions for either option are available in the S3 Block Public Access documentation. Remember that you can always check for public buckets in the S3 Console (we flag buckets with objects containing public permissions prominently there), and you can also use AWS Trusted Advisor’s S3 Bucket Permissions Check to notify you of any open buckets at no cost to you.
Amazon S3 Block Public Access Settings in the S3 Management Console:
S3 Object Lock
S3 Object Lock allows you to attach a specific retention date (or specify indefinite retention we call Legal Hold) to an S3 object. S3 then prevents deletion of that object until the date passes. Customers frequently have data with defined retention periods. For example, logging data may have a 30-day retention, quarterly backups a 6-month retention, and end-of-year summaries a 5-year (or longer) retention. Activating S3 Object Lock provides an additional layer of protection to ensure data is not inadvertently deleted. Object Lock can be used in two modes: Governance mode and Compliance mode. In Governance mode, the lock can be removed by an administrator with additional privileges. In Compliance mode, S3 does not allow deletion under any circumstance. Detailed instructions for using S3 Object Lock are available in the S3 Object Lock documentation.
With the security features of Amazon S3, we’re confident that you’ll have as good if not better control over the security of your data in Amazon S3 as you would have in a typical on-premises environment. As always, our teams are here to help you every step of the way, so if you have any questions about securing data in S3, please contact AWS Developer Support.