Connecting Multiple VPCs with EC2 Instances (SSL)
Amazon Virtual Private Cloud (Amazon VPC) provides customers with tremendous network routing flexibility. This document describes how a customer can create a secure SSL tunnel (using OpenVPN) to connect multiple VPCs into a larger virtual private network that allows instances in each VPC to seamlessly connect to each other using private IP addresses.
Submitted By: Steve Morad, John Reif
AWS Products Used: Amazon EC2, Amazon VPC
Created On: October 11, 2012
Topics
- Overview
- Configuration Walkthrough
- Connecting Additional VPCs
- Appendix: High-Level HA Architecture for VPN Instances
Amazon Virtual Private Cloud (Amazon VPC) provides customers with tremendous network routing flexibility. This document describes how a customer can create a secure SSL tunnel (using OpenVPN) to connect multiple VPCs into a larger virtual private network that allows instances in each VPC to seamlessly connect to each other using private IP addresses.
Please reference the Amazon Virtual Private Cloud Network Administrator Guide for complete VPC networking documentation; however, the following definitions, example configuration, and diagram may be helpful for understanding the content of this paper.
Internet Gateway (IGW)
The IGW is an egress point from a customer's VPC that allows public Elastic IP (EIP) addresses to be mapped to VPC instances. IGW provides public address mapping that allows VPN instances in each VPC to communicate with each other. When communicating between VPCs in different AWS Regions, the Internet gateway routes the VPN connections over the Internet. However, when communicating between VPCs in the same AWS Region, the IGW routes traffic directly between the VPCs using the AWS network.
SSL Connection
An OpenVPN SSL connection between two EC2 VPN instances that will be used to virtually connect the two VPC networks.
This guide uses the following VPC configuration for illustrative purposes:
- The SSL connections will require each VPN instance to live in a public subnet and have an Elastic IP address.
- VPN instances are a potential single point of failure. Please see the Appendix for a high-level HA design for this component
- This lab provides examples using Amazon Linux and standard Amazon Linux packages.
- This guide assumes you already have two or more VPCs created. For instructions on creating VPCs, please see the Amazon Virtual Private Cloud Getting Starting Guide.
- In this scenario, AWS manages the IGW and the customer is responsible for managing their EC2 instances and the VPN connections.
In this walkthrough, we will perform the following steps:
- Launch EC2 VPN instances
- Configure VPN server software on the EC2 instances
- Connect additional VPCs (if needed)
- Launch two Amazon Linux instances, one in each VPC public subnet, with the following characteristics:
- Assign the VPN instance a static private IP address (not required, but makes setting up the configure files much easier). In this example, we use 10.0.0.5 and 172.16.0.5.
- Allocate two VPC EIPs (or one VPC EIP in each region) and associate an EIP to each VPN instance. In this example, we use EIP1 and EIP2 to represent the EIPs for VPC 1 and VPC 2, respectively.
- Configure the instance Security Groups to allow UDP 1194 between the two EIPs.
- Disable Source/Dest checking on both instances by right-clicking the instances and selecting Change Source/Dest. Check.

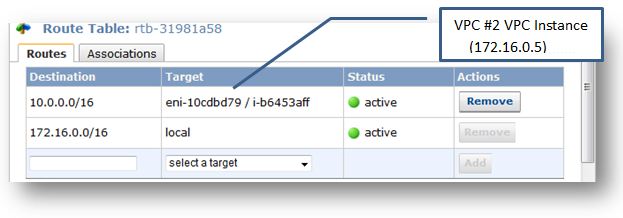
- Configure Routing Tables in both VPCs to send traffic to the "other" VPC through the VPC EC2 instances (note: you may need to configure multiple route tables for your public and private subnets depending on which subnets you want to route between.
The following examples demonstrate the appropriate modifications to the "Main" route tables in each respective VPC).
- Connect to each EC2 VPN Instance, and install the openvpn package with the following command:
Prompt> sudo yum install openvpn
- On the VPC1/EIP1 Instance:
- Create a new OpenVPN key:
Prompt> cd /etc/openvpn Prompt> sudo openvpn --genkey --secret ovpn.key
- Create a new /etc/openvpn/vpc1-to-vpc2.conf file similar to the following:
Prompt> sudo vi /etc/openvpn/vpc1-to-vpc2.conf
# Sample OpenVPN configuration file using a pre-shared static key # Port to use: 1194 is the official IANA port number port 1194 # Use a dynamic tun device. dev tun # Remote peer and network remote
route - On the VPC2/EIP2 Instance:
- Securely copy the resulting file (/etc/openvpn/ovpn.key) created on the VPC1/EIP1 instance to this second VPN instance in VPC #2.
- Create a new /etc/openvpn/vpc2-to-vpc1.conf file similar to the following:
Prompt> sudo vi /etc/openvpn/vpc2-to-vpc1.conf
# Sample OpenVPN configuration file using a pre-shared static key # Port to use: 1194 is the official IANA port number port 1194 # Use a dynamic tun device. dev tun # Remote peer and network remote
route - On both instances, perform the following steps:
- Start OpenVPN
Prompt> sudo service openvpn start
- Configure OpenVPN to always start on boot
Prompt> sudo chkconfig openvpn on
- Configure the Linux instances to route traffic by editing /etc/sysctl.conf and change the net.ipv4.ip_forward variable from 0 to 1
Prompt> sudo vi /etc/sysctl.conf
net.ipv4.ip_forward = 1
-
Restart your network settings for the network forwarding settings to take effect.
Prompt> sudo service network restart
When testing connectivity between VPCs, make sure you set the appropriate security group rules. Additionally, when performing connectivity tests originating from one of the VPN instances, be aware that the VPN instance may use its tunnel IP address as its source address when communicating across the tunnel. This makes it more difficult to test remote nodes without updating the route tables with the tunnel network as well.
You can connect additional VPCs by simply repeating the steps above while creating additional OpenVPN configuration files in /etc/openvpn and specifying a different port for each connection. For example, on VPC1/EIP1 instance, /etc/openvpn could have the following files to connect a third and fourth VPC via VPN:
vpc1-to-vpc2.conf vpc1-to-vpc3.conf vpc1-to-vpc4.conf
The EC2 VPN Instances in these additional VPCs would require a copy of the ovpn.key file as well as corresponding files like those created for VPC #2 above (with the corresponding port change for the VPN connection). Additionally, OpenVPN has a client/server model that can be used to connect multiple tunnel connections using a single OpenVPN process. This configuration involves setting up OpenVPN servers and clients and is beyond the scope of this document.
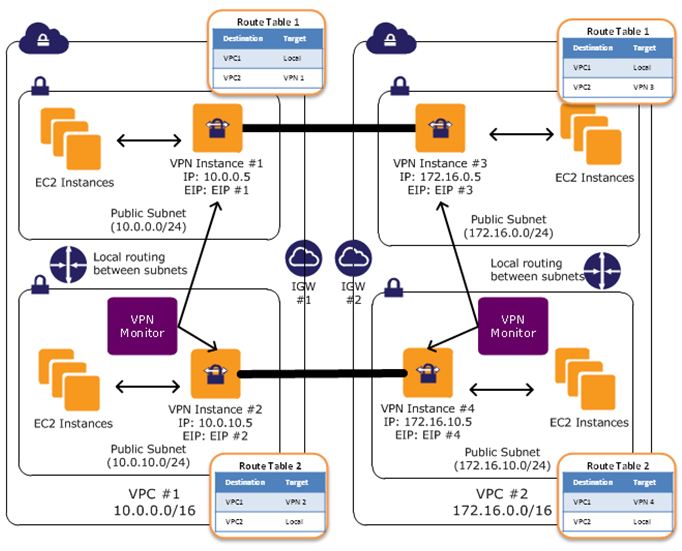
Creating a fully redundant VPC connection between VPCs in two regions requires the setup and configuration of 4 VPN instances and monitoring instances to monitor the health of the VPN connections.
We recommend configuring your VPC Route Tables to leverage all VPN instances simultaneously by directing traffic from all of the subnets in one Availability Zone through its respective VPN instances in the same Availability Zone. Each VPN instance will then provide cross-VPC connectivity for instances that share the same Availability Zone.
The VPN Monitor is a custom instance that you will need to create and develop monitoring scripts to run on. This instance is intended to run and monitor the state of VPN connection and VPN instances. If a VPN instance or connection goes down, the monitor will need to stop/terminate or restart the VPN instance while also re-routing traffic from one subnet to the working VPN instance until both connections are functional. High Availability for Amazon VPC NAT Instances: An Example provides an example of a script that could be modified to run on the VPN instances or a separate monitoring instance to preform this function.