- Products
- Management and Governance
- AWS CloudTrail
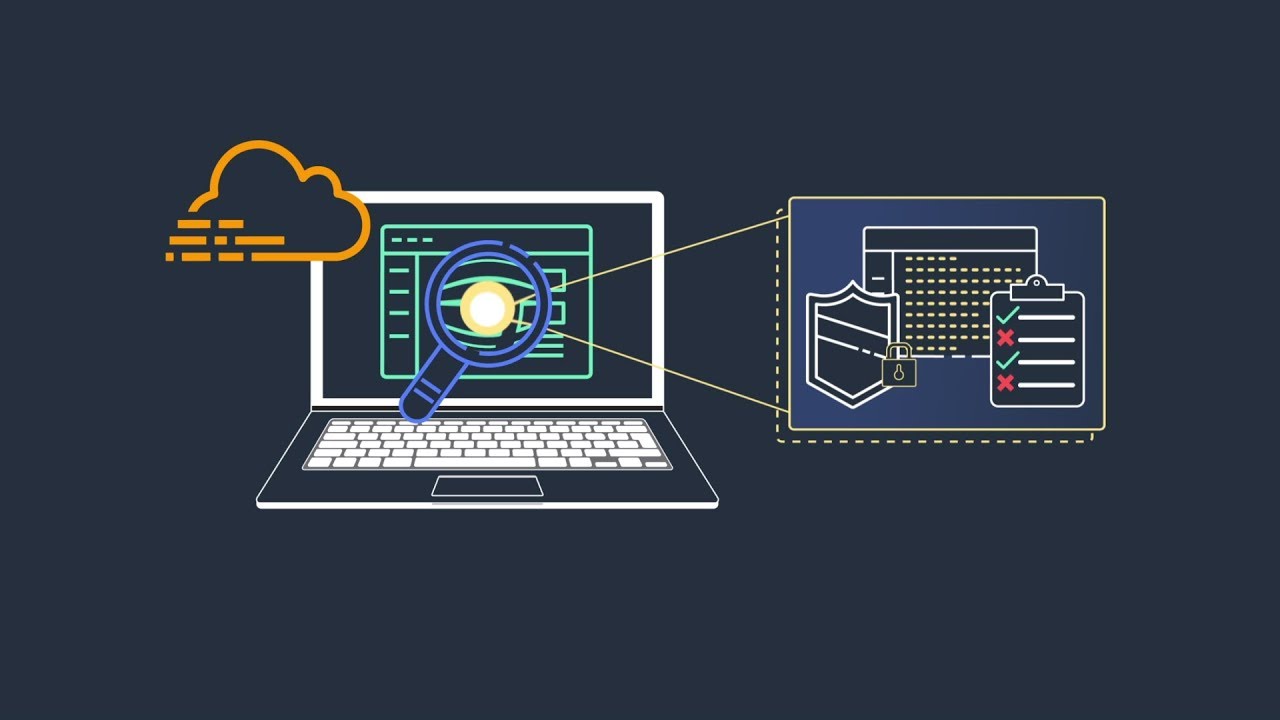
AWS CloudTrail
Track user activity and API usage on AWS and in hybrid and multicloud environments
End of Support notice
AWS CloudTrail Lake feature will no longer be open to new customers starting on May 31, 2026. For capabilities similar to AWS CloudTrail Lake feature explore Amazon CloudWatch. Learn more
Benefits
-
With CloudTrail Lake, you can ingest activity events from AWS and sources outside AWS, including other cloud providers, in-house applications, and SaaS applications running in the cloud or on premises.
-
In AWS CloudTrail Lake, you can immutably store audit-worthy events. Easily generate audit reports required by internal policies and external regulations.
CloudTrail helps you monitor AWS activity through multiple ways: detect anomalous API behavior with CloudTrail Insights for both management and data events, and track activity trends through data event aggregations which consolidates data events into 5-minute summaries, showing key trends like access frequency, error rates, and most-used actions.
Why CloudTrail?
Use cases
Protect your organization from penalties using CloudTrail logs to prove compliance with regulations such as SOC, PCI, and HIPAA.
Improve your security posture by recording user and API activity in your AWS accounts. You can also enhance your data perimeter with network activity events for VPC endpoints.
Answer operational questions, facilitate debugging, and investigate issues using SQL-based queries, natural language query generation, or Amazon Athena. Summarize query results by turning on the AI-powered query result summarization feature (in preview), further streamlining your investigations. Visualize trends with dashboards in CloudTrail Lake.
Learn how to run SQL queries against your event data using Amazon Athena
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages