- AWS Solutions Library›
- Guidance for Container Runtime Security Monitoring with CNCF Falco and AWS Security Hub
Guidance for Container Runtime Security Monitoring with CNCF Falco and AWS Security Hub
Overview
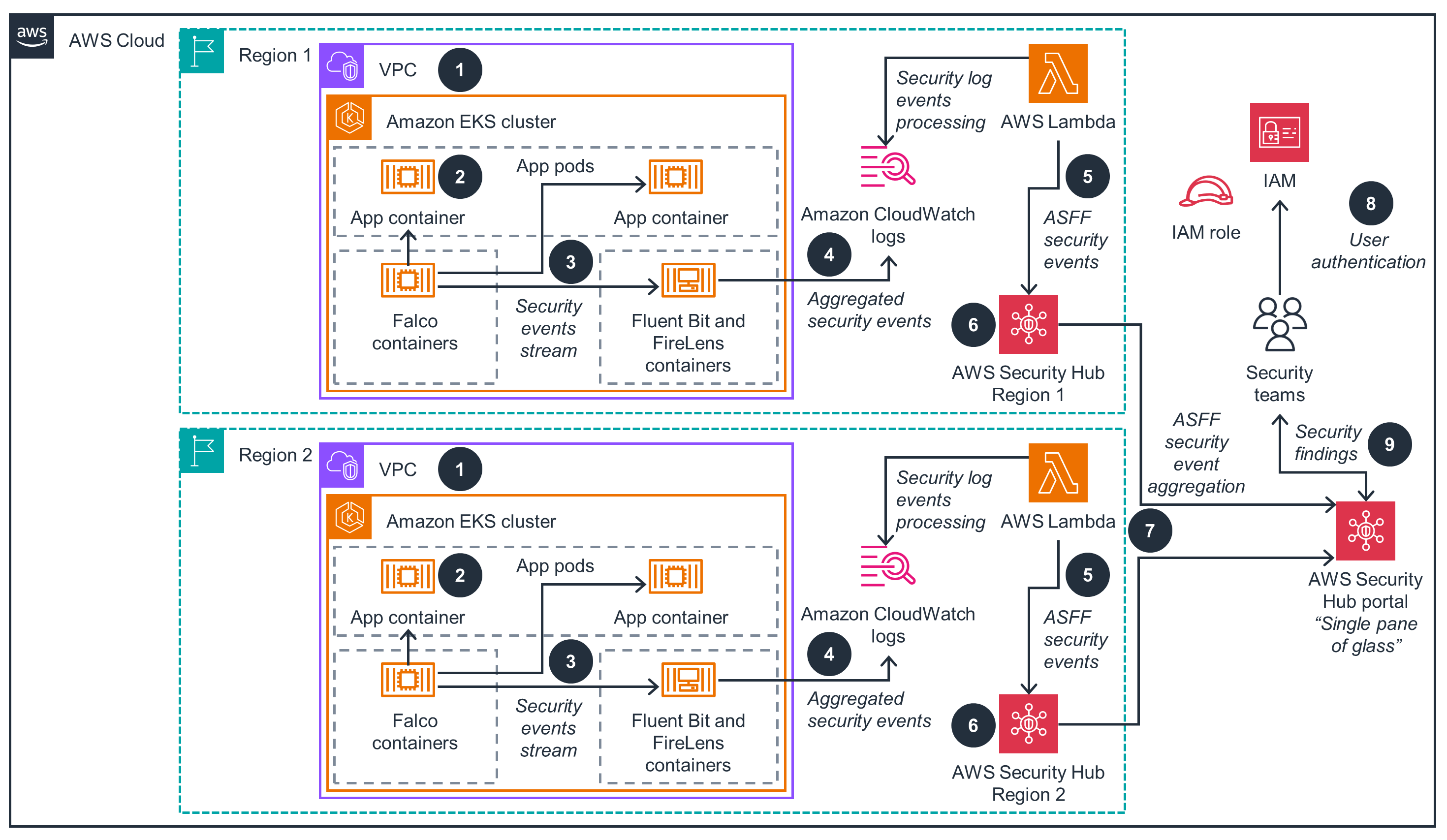
This Guidance shows you how to stream security event logs from Falco into AWS Security Hub in near real-time for enriched analysis. Provided by Cloud Native Computing Foundations (CNCF), Falco detects security events at runtime for containers. Using an integration of the FireLens and Fluent Bit tools with AWS services, this Guidance enriches security event logs generated by Falco and imports them into AWS Security Hub. Your security and DevOps teams can then use the Security Hub management portal to gain a centralized view of security events from all your container applications to facilitate triage and resolution.
How it works
Infrastructure
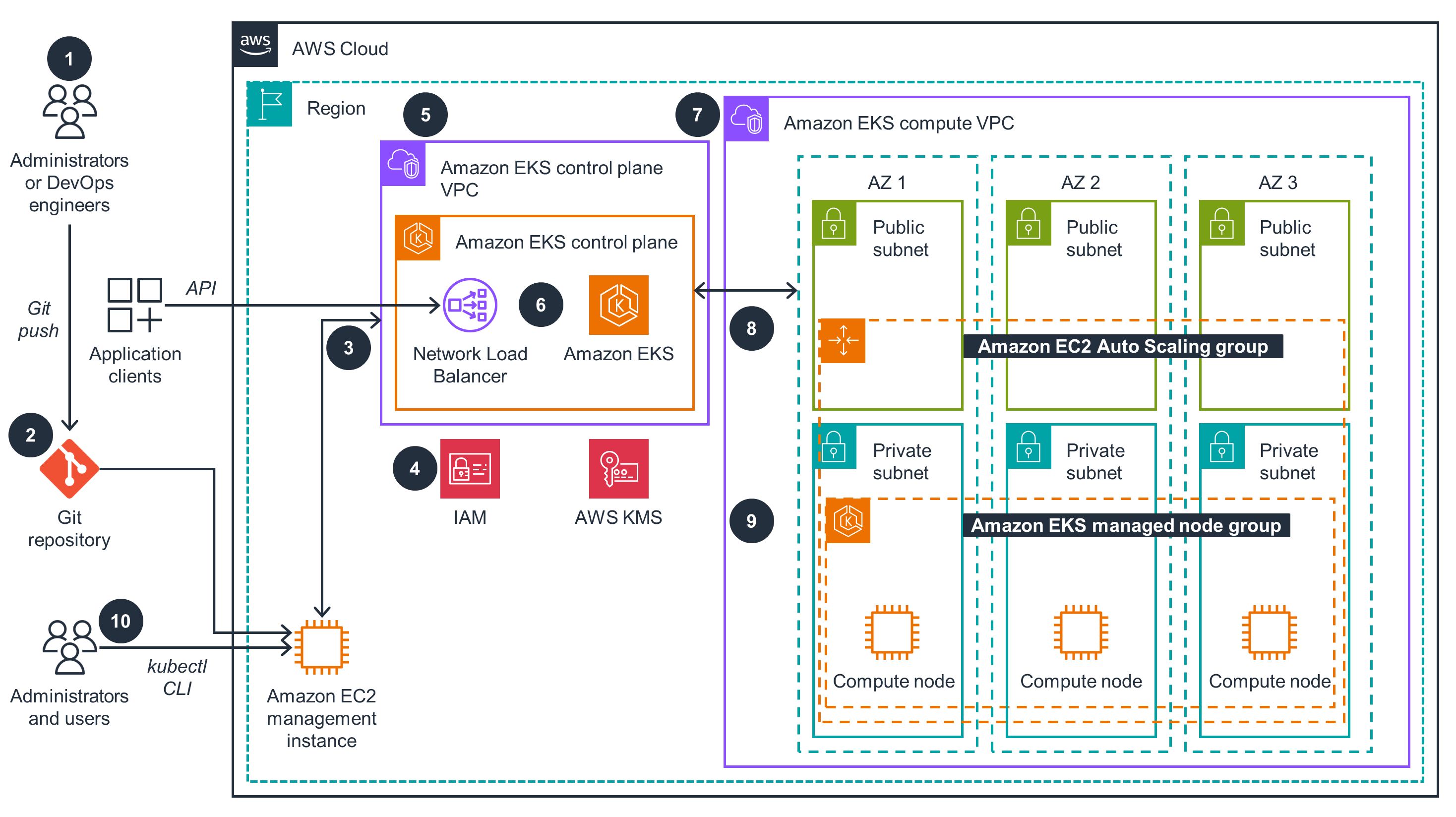
This architecture diagram shows how to set up the Amazon EKS cluster needed for this Guidance. To learn more about detecting security events using CNCF Falco and AWS Security Hub, open the Architecture tab.
Architecture
Get Started
Well-Architected Pillars
The architecture diagram above is an example of a Solution created with Well-Architected best practices in mind. To be fully Well-Architected, you should follow as many Well-Architected best practices as possible.
This Guidance provides operational excellence by invoking Security Hub workflows that respond in near real-time to security threats related to your business applications. The Fluent Bit and FireLens integration used with Falco sends information about containers’ potential runtime security violations to the CloudWatch log event manager. Lambda then converts them into ASFF and imports them into Security Hub portals, where your security team can review, triage, and remediate them.
This Guidance uses Falco to continuously scan the containers running on your Amazon EKS applications for runtime security events. Falco also monitors containers running on Amazon EKS cluster nodes for security violations and works with FireLens, CloudWatch , and Lambda to send security event information into Security Hub , which further aggregates the security event logs and displays them for review and triage by your security team. You can then use Security Hub to start remediation workflows for security threats. All IAM policies used in the Amazon EKS cluster are scoped down to the minimum permissions required for the service to function properly.
Amazon EKS is an enterprise-grade, reliable Kubernetes application service deployed with high availability across multiple Availability Zones. CloudWatch is a log-event-management service, and Lambda is an event-processing service; together, these services ingest and generate information on security threats that might impact application reliability. Security Hub aggregates and displays these findings so that your security and site reliability engineering (SRE) teams can quickly address threats, significantly reducing the chances of application failures due to security violations.
This Guidance provides efficient scalability and performance both for your containerized application platforms (using Amazon EKS ) and for event detection (using Falco, CloudWatch , Lambda ). You can also deploy this security monitoring solution across Regions, further helping you avoid negative performance impacts from security threats.
By using Falco, which is an open-source service, available at no cost, you can lower the cost of security event monitoring. CloudWatch , Lambda , and Security Hub are charged based on the amount of ingested and processed event data. These services provide a free tier of data storage and processing, so costs only accrue after you exceed this tier. Additionally, CloudWatch provides automatic archival for logs, helping you reduce message storage costs.
CloudWatch , Lambda , and Security Hub are serverless and automatically scale to match workload demands and eliminate idle resources, and Amazon EKS provides high elasticity. By using these managed AWS services, alongside cloud-native technologies that run on elastic Amazon EKS clusters, this Guidance helps you achieve a high utilization of infrastructure resources, helping you minimize energy waste. Additionally, this Guidance does not require custom hardware or physical servers, and by using it to remediate security threats, you can further optimize resource utilization.
Disclaimer
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages