Containers
Results of the 2020 AWS Container Security Survey
In 2019 we carried out the first AWS Container Security Survey and now we have the results of this year’s survey for you available. As in 2019, we conducted an anonymous survey throughout 2020 amongst container users on AWS. From the 655 people who visited the survey, 295 started it and 156 completed it (completion rate of 52%) with an average completion time of a little over ten minutes. I again would like to thank everyone who suggested questions as well as helped spread the word. Big kudos to everyone who participated and provided input!

Overall, we notice a positive trend in terms of good practices concerning container security. Almost all key areas, from scanning to policies enjoy positive adoption rate changes compared to 2019. Two things stand out:
- There seems to be a decrease of uptake around supply chain management; further investigations are necessary to reveal the underlying reason, that is, if it is related to the survey question or if there’s a deeper underlying reason for this.
- The adoption rate for signing container images has not changed and remains around 10% (same as in 2019). We would expect that with the work around Notary 2 this to change in 2021; we’re contributing to the upstream efforts and looking forward to see this topic receiving more attention.
The summary of the results as a PDF file as well as the raw results in CSV format are available along with the details on the questions we asked. Now let’s have a look at the details!
In terms of demographics, we had a single question in there, and this one was about the role:
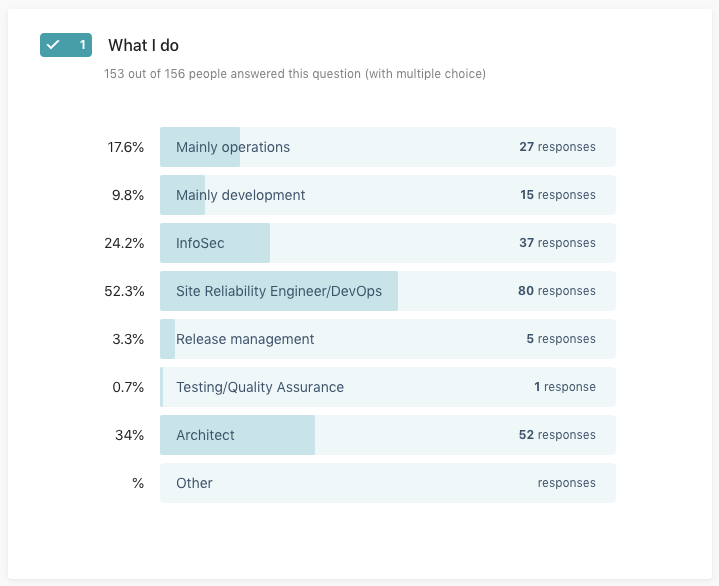
It’s great to see more than 50% of the responses from folks that are in a Site Reliability Engineering/DevOps role. Compared to 2019, the number of Architects responding to the survey increased and also InfoSec got more involved. The response rate from developers remains low.
Next, we asked about how folks are running containers, that is, about their container orchestrator and compute engine of choice:
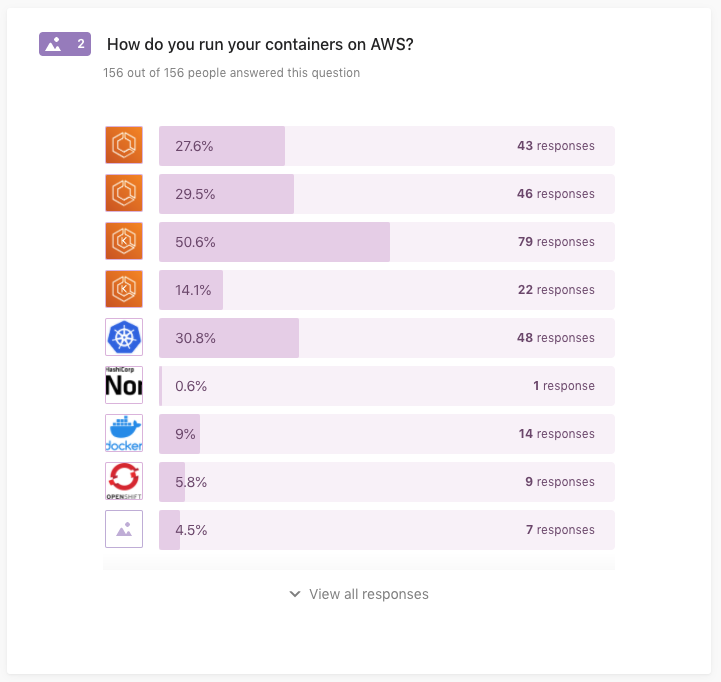
The top three combinations of container orchestrators and compute engine mentioned were Amazon EKS on EC2 with 79 responses, DIY Kubernetes on EC2 with 48 responses, and Amazon ECS on AWS Fargate with 46 responses.
Next up were artifacts, that is, where container images and the like are stored (new question, not asked in 2019):
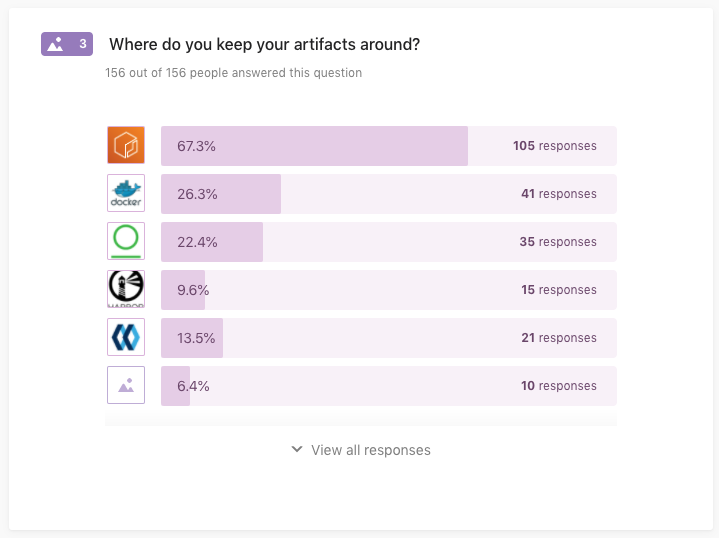
Amazon ECR leads with 105 responses, followed by Docker Hub (41) and JFrog Artifactory (35).
Related to the previous question, we asked people how they do static image scanning:
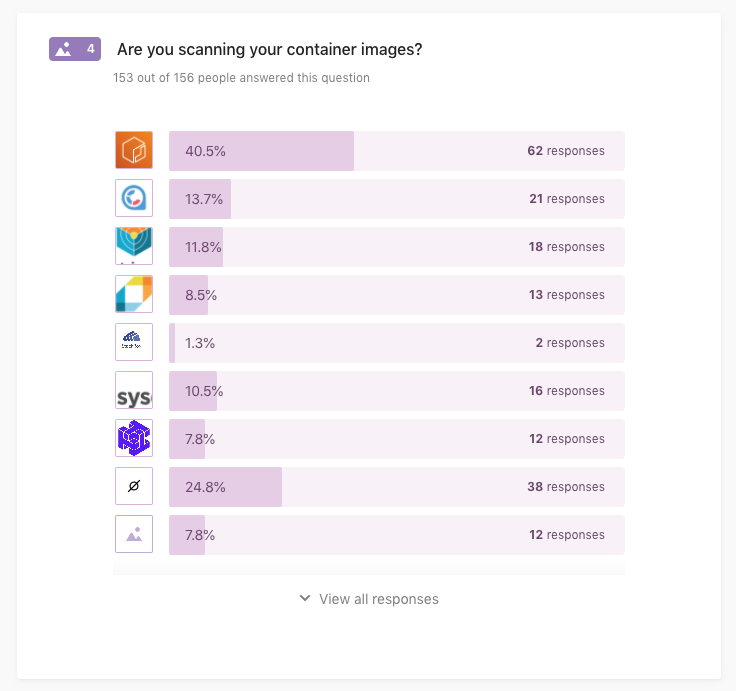
Native ECR scanning got 62 responses, followed by using open source Clair in a self-managed setup (21 responses), and open source Trivy self-managed (18). What stands out compared to 2019 is that the number of people responding that they do not (yet) scan their container images dropped from 38% to 24.8%, that’s good progress!
Moving on with scanning, but this time around dynamic or runtime scanning:

While still some 70% say they do not (yet) scan their containers at runtime, that is, in the context of their container orchestrator such as ECS or EKS, we see some positive trends compared to 2019. First, the number of people not scanning decreased from 83% to 70%, and second, we see CNCF Falco (27 responses), Twistlock (10 responses for each Prisma Cloud and Twistlock Defender), as well as Aqua Security (7 responses) gaining traction.
Shifting gears now, we asked about how sensitive data such as passwords and API keys are managed:
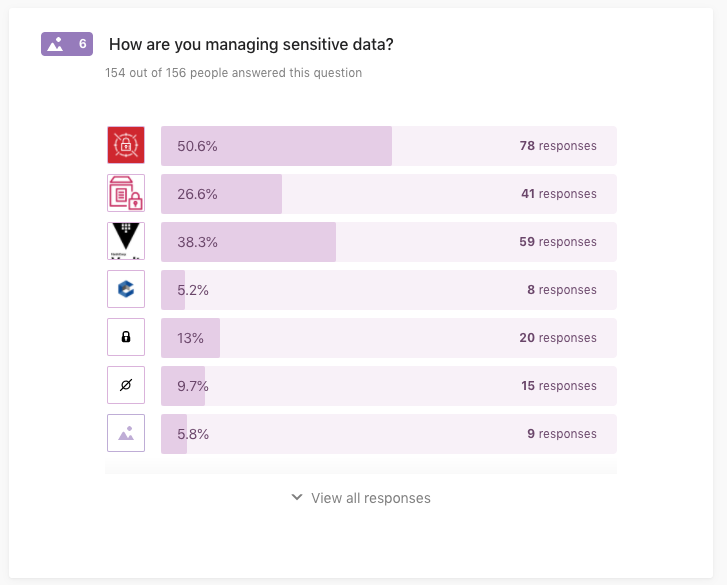
What we can see in above responses is that AWS Secrets Manager is leading (78 responses), followed by HashiCorp Vault (59 responses), and AWS Parameter Store (41 responses). The percentage of folks who say they do not encrypt sensitive data decreased slightly from 11% last year to 9.7% this year.
Moving on to container image signing:
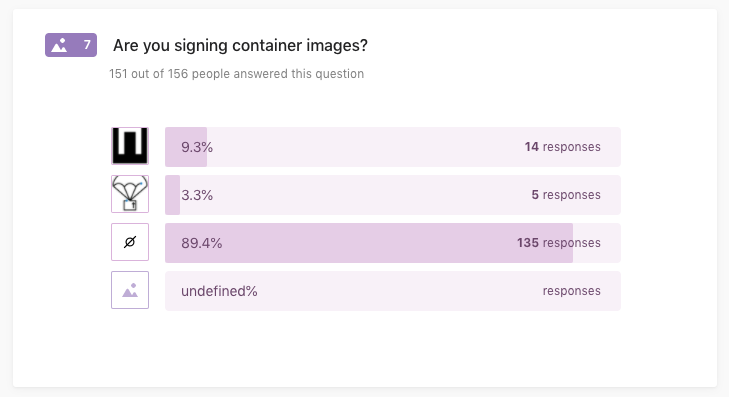
This looks pretty consistent with last year’s results. The majority of 89% are not signing their container images, yet.
Concerning supply chain management, we see—a little surprising, but this could be due to the sample size last year—that still the majority does not do it (93%, up from 81%):
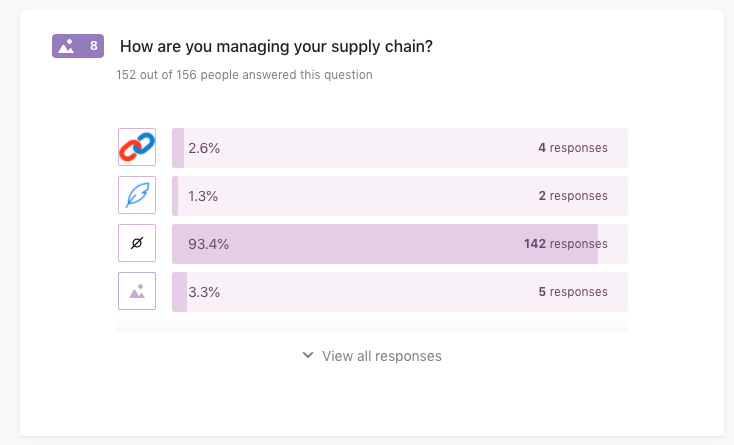
Most folks who do manage their supply chain seem to have home-grown or proprietary solutions in place (5 responses), followed by CNCF in-toto (4 responses), and Grafeas (2 responses).
Next up was a new question that ask about the policy management and enforcement strategy, in general:

From the 155 people who answered this question, we can see that the majority (76 responses) does not yet have a general policy management strategy in place, however CNCF Open Policy Agent (OPA) already enjoys almost a third (42 responses) of the coverage, followed by DIY methods (38 responses).
Another new question in 2020 was around network traffic, both in-cluster (East-West) and to the outside (North-South):

This is some interesting uptake: 121 people responded they filter network traffic at ingress, followed by 104 responses for security groups/ACL, and 40 for in-cluster. I believe we should drill deeper here next year.
Next, we focused on Kubernetes which more than 77% of the participants say they are using in one form or the other:

In the context of Kubernetes, we first asked a new question around GitOps uptake:

A promising 2/3 of the people who answered this question (78 out of 121) do already use GitOps in their setup.
Next up was a question around Kubernetes network policies that we can compare with last year, again:

Overall, we see a bit more than a third not yet using network policies, followed by Calico (35% in 2020, 60% in 2019), service meshes (21.8% in 2020, 33% in 2019), and Cilium (10%, up from 0% last year). Note that, given that we didn’t include the “not using” option last year the trends should interpreted with this in mind.
Continuing with Kubernetes policies, this next question focusing on runtime policies:
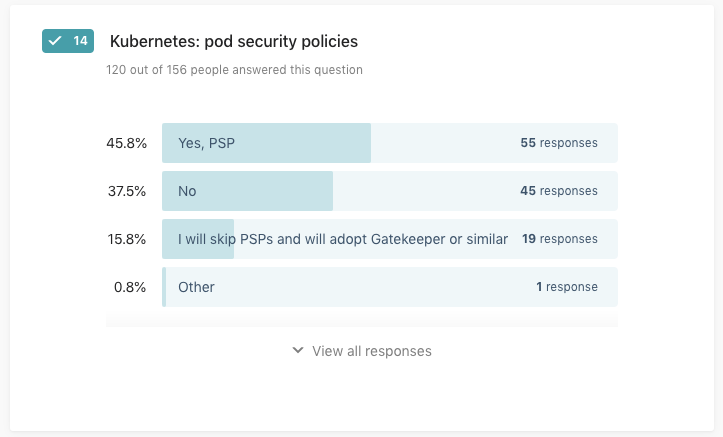
We note that last year we only asked if Pod Security Policies (PSP) are used, so, again the numbers are not 1:1 comparable with 2019 in this case. While the overall picture is stable, some 15% said they intend to skip PSPs in favor of an alternative such as the CNCF OPA subproject Gatekeeper. This seems like a sound strategy, given the pending deprecation of PSPs in Kubernetes.
Then we focused on user management in Kubernetes in the next question:

What we see here, compared to 2019, is that not much has changed: directly using IAM users/roles is still leading by far (80% in 2020, slightly down from 86% in 2019), followed by SSO (29% in 2020, 31% in 2019), and LDAP-based solutions (20% in 2020, up from 7% in 2019).
Related, we asked again about least-privileges on the pod level:
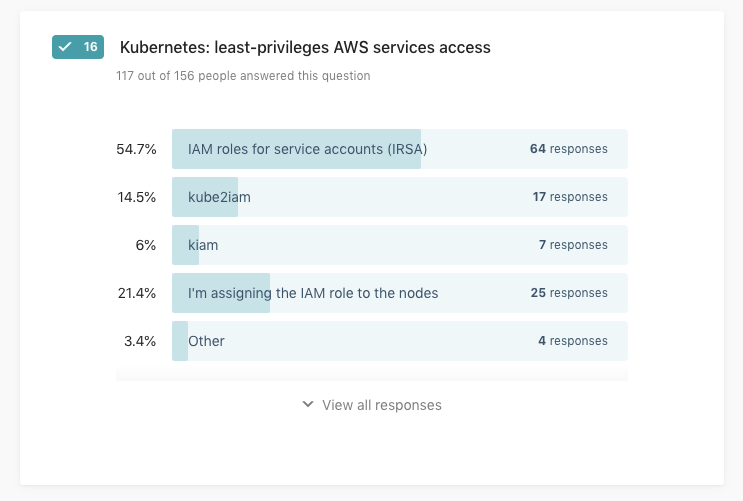
As in 2019 the case, the AWS-native solution IAM roles for service accounts is the most often used solution (54%, up from 43% in 2019), followed by node-level IAM roles (21% in 2020, down from 25% in 2019), and kube2iam (14% in 2020, down from 20% in 2019). While it’s great to see that the trend to migrate to pod-level role management is a positive one, we still need to invest more work to get the remaining 20%+ who’re assigning IAM roles to nodes rather to adopt pod-level mechanisms.
With this we wrap up the 2020 survey results and if you’re interested in the raw results—and what people said what else they use—check out the answers in the raw results on GitHub. I’d like to thank you again for your time, and looking forward to the 2021 edition.