Containers
Results of the 2019 AWS Container Security Survey
Security is a top priority in AWS, and in our service team we naturally focus on container security. In order to better assess where we stand, we conducted an anonymous survey in late 2019 amongst container users on AWS. Overall, we got 68 responses from a variety of roles, from ops folks and SREs to InfoSec to developers and architects. Here are the results, with some interpretations and conclusions. I’d like to thank everyone who helped spreading the word and especially the many AWSome folks who took time out of their busy schedule to provide the raw data. The questions and results are available via GitHub.
Let’s start with the key stats: from the 90 people who visited the survey, 68 completed it with an average completion time of just over seven minutes. In terms of demographics, we had a single question in there, and this one was about the role:
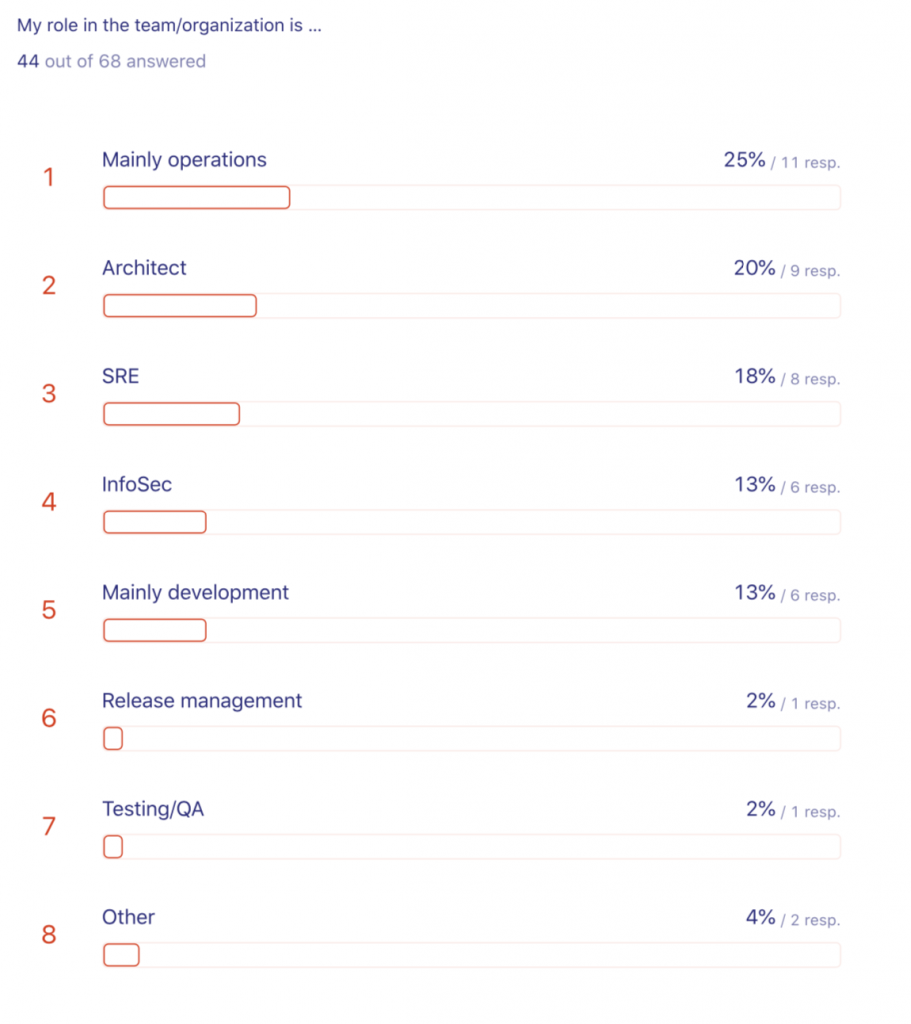
Nice distribution across the spectrum, I’m glad that also testing/QA was interested and a little surprised that release management was not stronger represented.
Container Security General
Moving on to overall setup: not very surprisingly, we found that any given user employs multiple container orchestrators and offerings. In detail, it looks as follows:
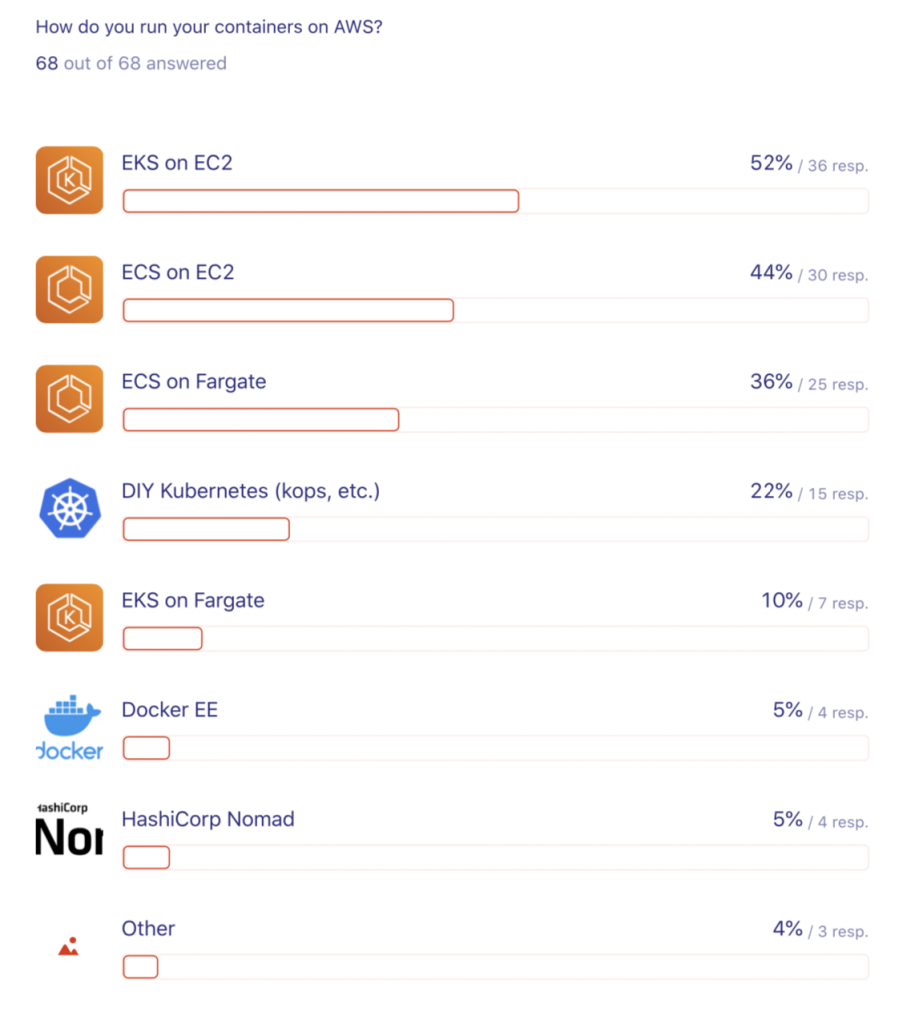
EKS on EC2 as well as ECS on EC2 lead with 52% and 44%, respectively. In the long tail we see amongst other systems Docker EE and Nomad used, great!
Next, we looked at proactive or preventive methods employed: scanning, signing, and supply chain management. The overall results look as follows:
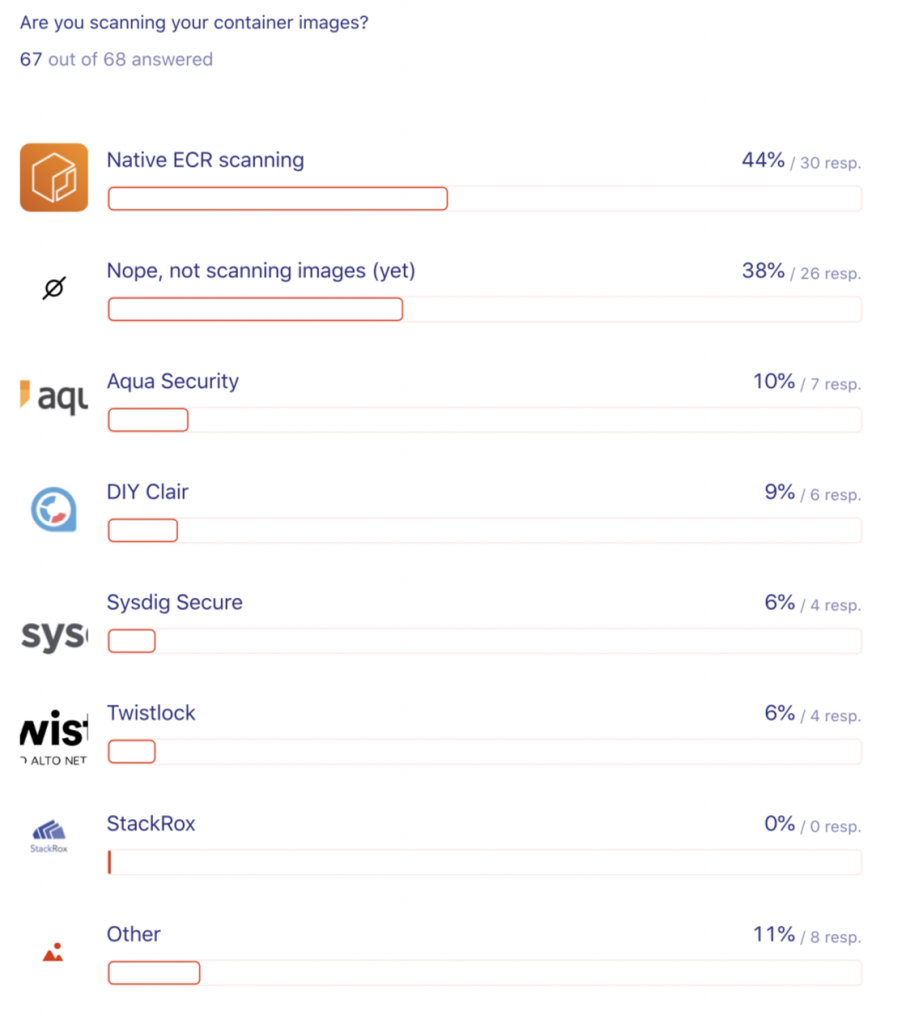
It seems like the native ECR scanning feature we introduced in 10/2019 enjoys some popularity and it’s great to learn that a majority (62%) of the folks out there have static scanning covered. But how is the state of the world concerning dynamic or runtime scanning?

Not so great, here a huge majority, 83% of the respondents, said they don’t do it (yet). Also, nice to see CNCF Falco being actively used, leading the pack with 13%.
Next, up container image signing. Oh boy. If you are currently not in the business of doing it, let me tell you, you’re in good company (hey, I’m not judging, just saying):

Yup, 89% say they don’t sign their images. Let’s change that! Read about the Notary 2 effort, and join us on the #notary-v2 channel on the CNCF Slack to contribute.
Now, how about managing the digital supply chain?
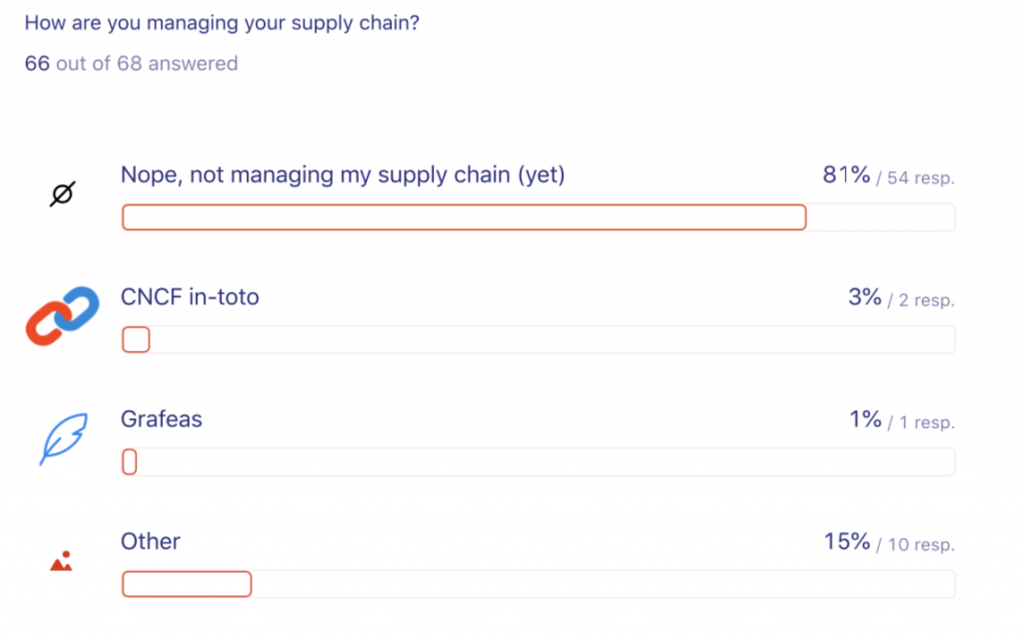
I was not too surprised. Most (81%) of the survey folks said that they’re currently not managing the supply chain. Well, at least some are looking at CNCF in-toto, that’s a start.
Next, we looked at how sensitive data is being managed. Think of database passwords or API keys. Who’s brave enough to admit they’re storing it in plain text? Let’s see …
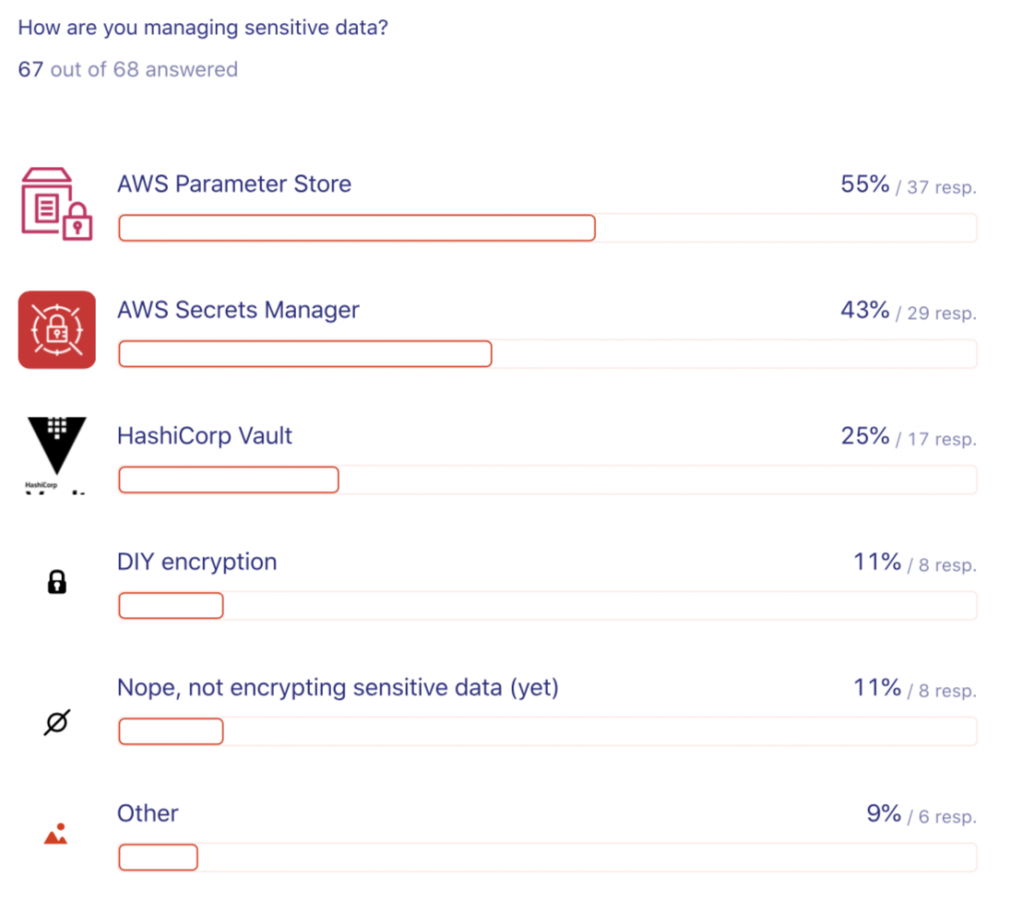
The two managed services, AWS Systems Manager Parameter Store and AWS Secrets Manager seem to be widely used (50 out of 67 said they use an AWS managed offering), followed by the popular solution by HashiCorp, Vault. Interestingly, 11% did say they are not (yet) encrypting sensitive data. As our CTO likes to say: “Dance like nobody’s watching, encrypt like everybody is”.
Kubernetes
If participants answered Yes to the question “Are you using Kubernetes on AWS” they were presented with a few further questions. Here are the results.
First off we were interested in the uptake of Network Policies:
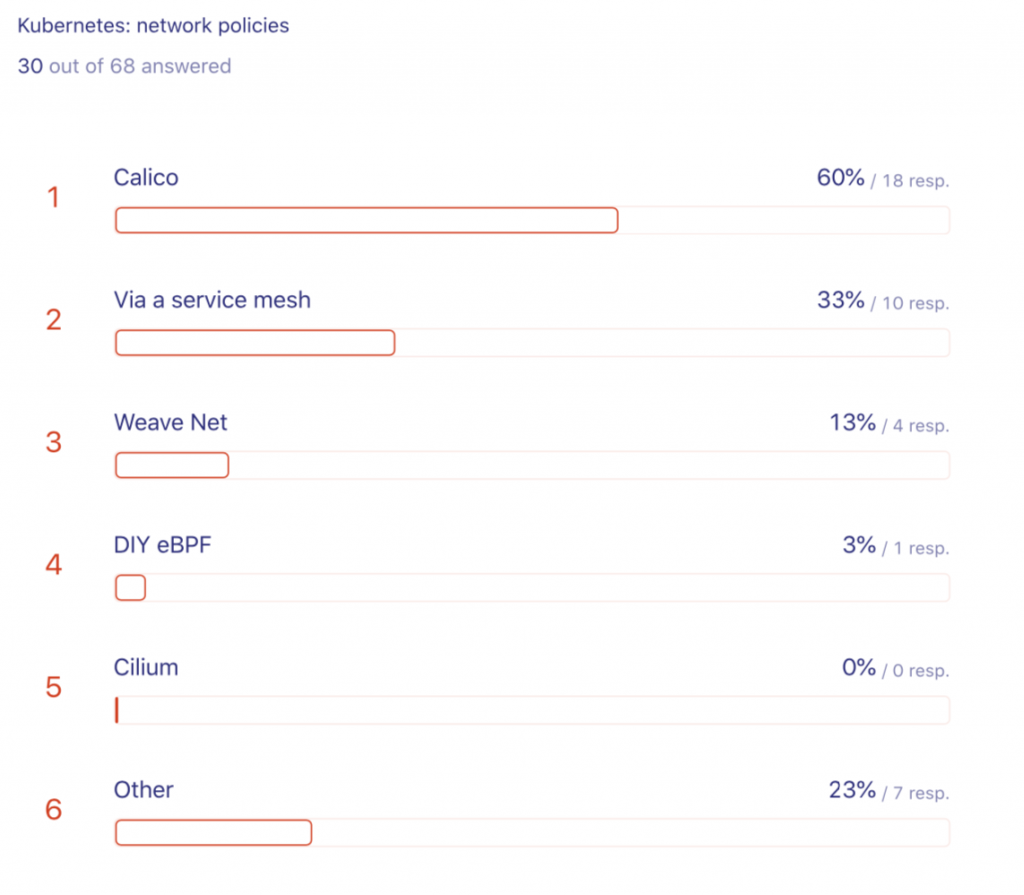
Seems like a good uptake with Calico leading the pack comfortably and service meshes as a second popular option. I honestly was surprised to find that not a single respondent said they’re using Cilium (an eBPF-based solution). How comes?
Next up were global runtime security policies, or PSPs as we kewl kids say. Given the current discussion about promoting PSP to GA (or not?) and potentially using OPA as a replacement, these results make sense, I suppose:

Then, we asked about user management. Now, Kubernetes intentionally outsourced user management and doesn’t really treat users as first class resources. They are global and it’s up to you to find a solution to map existing group memberships and similar things into Kubernetes. What we found was:

Interestingly enough, plain old IAM users/roles are still clearly leading with SSO-based solutions such as OIDC coming in second.
Continuing down the authn/authz path we asked about pod-level least privileges management.

Seems like the AWS-native IAM Roles for Service Account (IRSA) feature we launched in 09/2019 is enjoying increased uptake with a somewhat sobering 25% of the folks saying they are (still) assigning roles to the nodes. Please, reconsider.
OK, that was it for the current (or better say 2019) state of the world concerning container security in AWS. All the details are available via GitHub and I’d like to thank you again for your time, if you did participate. If not, there will be another one, later in 2020, so there’s your chance to show off!