Outbound identity federation
Securely federate your AWS identities to external cloud providers, SaaS platforms and self-hosted applications
Securely and easily federate your AWS identities to external services
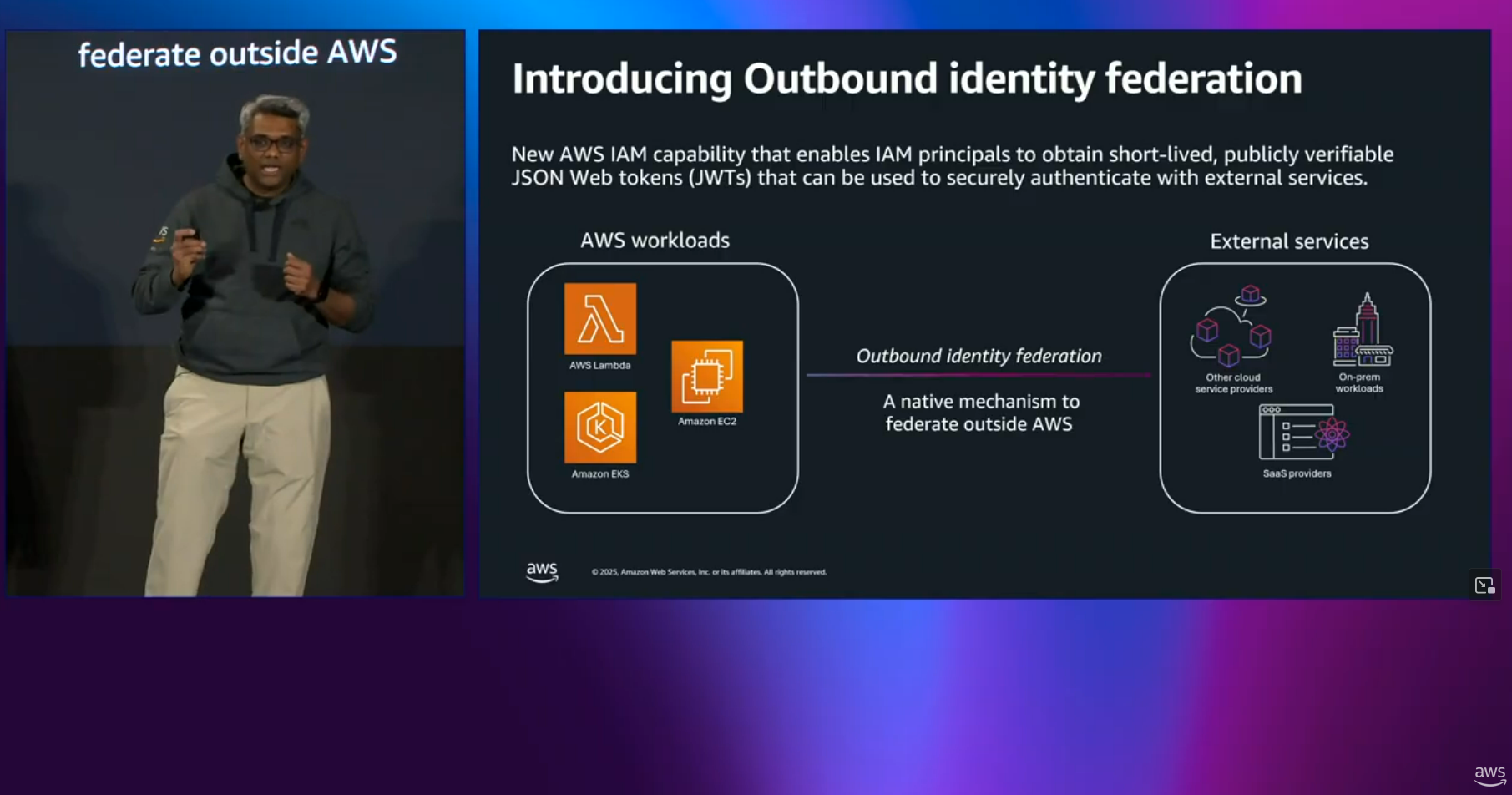
AWS Identity and Access Management (IAM) outbound identity federation enables you to securely federate your AWS identities to external services. This capability makes it easy and secure to authenticate your AWS workloads with a wide range of cloud providers, SaaS platforms and self-hosted applications.
IAM principals can now obtain JSON Web Tokens (JWTs) that are short-lived, cryptographically signed and publicly verifiable. These tokens contain standard OIDC claims along with custom claims that provide rich context about the IAM principal, enabling external services to implement fine-grained access control. The standardized JWT tokens eliminate the need for you to store long-term credentials for external services, improving your security posture. Administrators can control access to token generation through familiar IAM policies and monitor token usage using CloudTrail logs, enabling them to meet their organization’s security and compliance requirements.
Benefits of AWS outbound identity federation services
Securely and efficiently federate to external services
Eliminate long-term credentials
AWS workloads can securely authenticate with external services using short-lived JSON Web Tokens. This eliminates the need to store and manage long-term credentials like API keys and passwords. Using short-term credentials helps improves your security posture and eliminates the operational burden of credential rotation.
Use a standards-aligned approach
The JSON Web Tokens are cryptographically signed, publicly verifiable and compatible with any external service performing token validation as per the OpenID Connect (OIDC) specification. This enables broad compatibility with third-party providers without custom integration work.
Enable fine-grained authorization
Tokens are enriched with identity-specific context like Account ID and Principal tags, and session context like EC2 instance ARNs and Lambda source function ARNs that assert your workload's AWS identity to external services. External services can use this context to implement fine-grained access controls.
Control access to token generation and monitor usage
Restrict access to token generation and enforce token properties such as lifetime and permitted audiences using IAM policies. This ensures that only authorized workloads can obtain tokens to connect to external services. All token generation requests are logged to CloudTrail for security monitoring and compliance purposes.
Customer testimonial
The National Archives is the official archivist and publisher for the UK Government, holder of historic national documents such as the Domesday Book and the Magna Carta, with extensive digital records from Government, UK Parliament, Ministry of Defence and other public bodies. Our cloud-based digital archiving systems and applications are hosted in AWS, and in some cases need to securely ingest data from Azure Storage.
"To meet our security policy and comply with UK government standards, this inter-cloud connection needs to be fully authenticated, auditable, encrypted in transit, without the use of long-term static credentials which require regular rotation and could become compromised. We were excited at the launch of AWS IAM outbound federation, because it neatly solves this problem, with a robust implementation that is standards-based for full interoperability between clouds, and straightforward to implement. Even better, once set up, it's zero maintenance, with no secrets or certificates to rotate."
Kurtis Mash, Lead Technical Architect
The National Archives

Outbound identity federation use cases
Access resources across cloud providers
AWS workloads can securely access resources and services hosted on external cloud providers such as Azure and GCP without using long-term credentials. For example, an AWS Lambda function processing data can use short-lived tokens to access an external cloud provider's storage service or query their database.
Integrate with SaaS platforms
AWS workloads can securely connect to external software-as-a-service (SaaS) providers like Databricks and Snowflake for analytics, data processing, monitoring, and more without storing long-term credentials like API keys or passwords in your code or secrets manager. For example, AWS Lambda functions can use short-lived tokens to send metrics to observability platforms or push data to analytics services.
Authenticate to hybrid and on-premises applications
AWS workloads can securely connect to your own applications hosted on-premises, in other cloud environments, or across hybrid architectures. For example, an AWS workload can use short-lived tokens to interact with containerized applications running in your on-premises Kubernetes cluster. This eliminates the need to store secrets or use custom authentication mechanisms.