AWS Cloud Operations Blog
Automate enrollment of accounts with existing AWS Config resources into AWS Control Tower
Customers who deployed AWS Control Tower in their existing organization will begin enrolling existing member accounts located under Organization Units (OU) to bring those accounts under the governance of Control Tower. In most cases, the customer has already enabled AWS Config to record, and evaluate AWS resource configurations in existing accounts.
Previously, customers who would want to enroll these existing accounts with existing AWS Config resources first needed to delete AWS Config resources from the account. Here are the types of AWS Config resources that would need to be modified so that you can enroll your account into AWS Control Tower.
However, many customers don’t want to delete these AWS Config resources because it will stop resource recording in their accounts. In other uses cases, this might not be allowed according to their security and compliance requirements.
AWS released a feature for customers to update their existing AWS Config resources to be compatible with AWS Control Tower. This update needed a few manual steps to be performed in all of the existing accounts. This can be cumbersome if you have many accounts and many regions under the assessment of AWS Config.
In this post, we provide you automation via python scripts for manual tasks that are currently required to enroll accounts that have existing AWS Config resources.
Considerations
The following points must be considered before executing the script given in this post.
- AWS Control Tower is deployed and you have access to the management account (through AWS SSO for example) with the required privileges (administrator access recommended) to ensure running of the automated script.
- There are no custom Service Control Policies (SCP) applied on the OU that might prevent the automation or OU registration process.
- Enable trust access with AWS Organizations for AWS CloudFormation StackSets if it isn’t already.
- We suggest executing the script (provided within this post) on Test or Dev OU before running it on Production OUs.
- Make sure that you have Python 3 installed on the local terminal. If not, then download it here. For CloudShell instance, it’s already installed.
Description
An AWS Control Tower Administrator will rely on their SSO credentials (administrator access) to run the scripts provided in this post that baseline all accounts and update existing AWS Config resources. This process will be conducted on one OU at a time.

In this post, we provide two python scripts that will automate the task mentioned here. The following is a short summary:
1 – fetch-account-details.py fetches the required details to submit a support case to allow-list accounts.
2 – prepare_ou.py conducts a series of actions to baseline an OU:
- Collect all of the details required from your environment to update the AWS Config resources.
- List all of the accounts existing in the provided OU.
- Deploy the required AWS Identity and Access Management (IAM) roles to make sure that the required access rights are available in the accounts as per AWS Control Tower requirements.
- For each account, loop over all of the AWS regions managed by AWS Control Tower and detect AWS Config resources.
- Finally, update the existing AWS Config resources present in AWS Control Tower governed regions, and, if not present already, create new resources as required by AWS Control Tower.
Execution Steps
If you have nested OUs, then you must first run the next three phases for the parent OU, and then for the nested OUs as described in the documentation.
Phase 1
Phase 1 consists of gathering the account IDs of the accounts that you wish to enroll to AWS Control Tower and that have existing AWS Config resources. You must contact customer support with a ticket to add the accounts to the AWS Control Tower allow list.
To fetch these details, execute the script fetch-account-details.py by using your SSO administrator user.
- You might want to opt for one of these login options:
- CloudShell: (see Getting started with AWS CloudShell)
- AWS SSO CLI in your local environment: (see AWS SSO CLI)
- Exporting the AWS SSO to your local environment: Login to SSO portal, and copy the ControlTower administrator user temporary credentials. For more details, refer to How to retrieve short-term credentials for CLI use with AWS Single Sign-on. Export user credentials. Copy and paste from the SSO portal (not needed if using CloudShell with SSO administrator user).
- Export the Control Tower home region (region where Control Tower deployed) environment variable.
- Download the script
fetch-account-details.pyfrom here. - The script needs an AWS OU ID as an input parameter. Identify the OUs that comprise of the accounts with AWS Config enabled since those accounts must be enrolled in AWS Control Tower. Copy the OU ID from the Organization console. For more information on getting OU ID, check here.
- Execute the script with the following command:
A successful execution of the above command will print the details that you need for the support ticket.
If you have multiple OUs where AWS Config is present under their accounts, then run the above script for every OU, and continue copying the account numbers under it. Consolidate all of these account numbers and create a single AWS Support ticket for all of the accounts.
Once your customer support ticket has been processed, then you can proceed to Phase 2.
Phase 2
In this phase, you run the Python script that will baseline the accounts and prepare them for enrollment into AWS Control Tower. This will require 3 steps:
- You will again need to fetch access credentials in a similar manner as in Phase 1, Steps 1 and 2.
- Download the script
prepare_ou.pyfrom here. - Execute the scripts.
The script offers the Dry run mode(-d) that prints the different actions that it performs. Note that this mode will deploy the “AWSControlTowerExecution” IAM role on all of the member accounts of the desired OU in order to read the details.
In the case of a successful execution, the dry run will log information about the IAM roles to be deployed and AWS Config resources to be changed. If those changes are correct as per your current setup, then run the next command to make actual changes.
Execute the script with the following command (fetch the OU ID as mentioned in Phase 1, Step 5):
In the case of a successful execution, the script will log information about the IAM roles deployed and AWS Config resource changed. If there are any errors, then the script will output the errors.
The script will take approximatively 15 seconds per region per account to run.
Once the script is executed successfully, you can move to Phase 3.
Phase 3
There are two ways to enroll existing accounts into AWS Control Tower governance:
- Register OU functionality (recommended)
- Enroll account by account – single account enrollment
In this post, we will opt for “Register OU” method. See the single account enrolment process here.
As of today, you can register OUs containing up to 300 accounts (refer quota). If an OU contains over 300 accounts, then you can’t register it in AWS Control Tower. In this case, you could split the accounts in multiple OUs or nested OUs.
Log in (with SSO) to the AWS Control Tower Console using an AWS Control Tower administrator role. In the left-pane navigation menu, choose Organizational units. Select the previous OU that you baselined in Phase 2, and select Register OU.
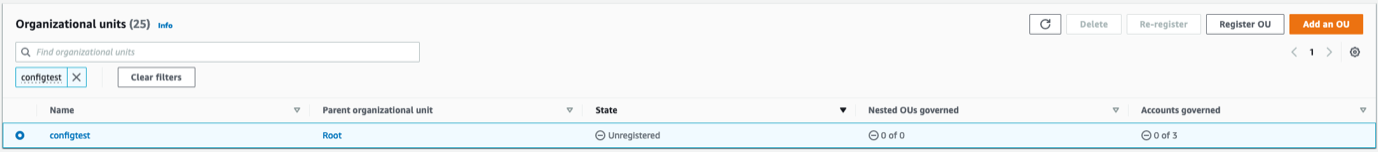
Next, the console will provide the account list of the accounts that will enroll (under this OU), in addition to the Risks and expectations (preventive and detective guardrails that will be enabled). Agree to terms, and then select “Register OU” and start enrolling the OU.
Once the registration process is complete, you can see the enrolled status in front of all of the accounts under the registered OU. If you have nested OU underneath it, repeat the above Register OU steps like parent OU.
Conclusion
In this post, we showed you how to automate enrollment of an OU with accounts that have exiting AWS Config resources into AWS Control Tower. You can also modify this automation as needed.