AWS Architecture Blog
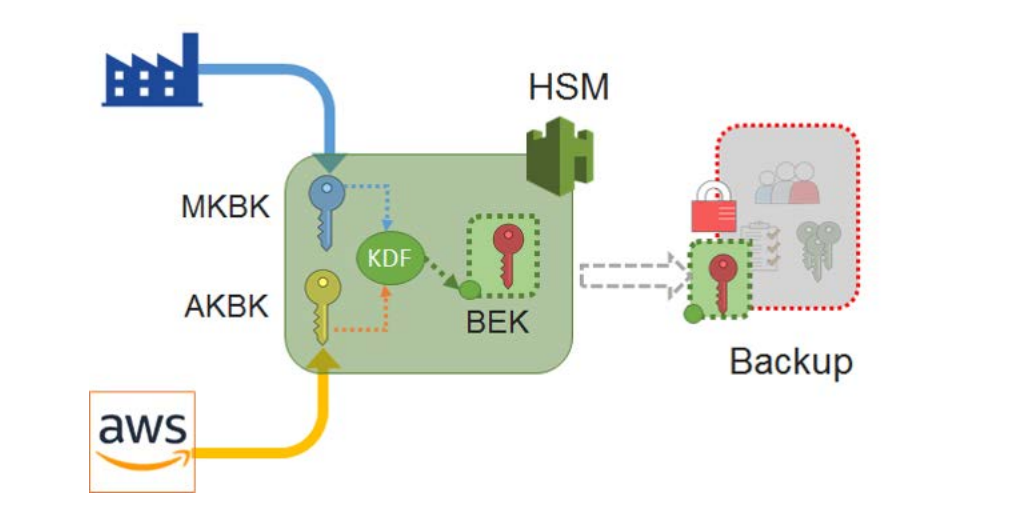
Security of Cloud HSMBackups
Today, our customers use AWS CloudHSM to meet corporate, contractual and regulatory compliance requirements for data security by using dedicated Hardware Security Module (HSM) instances within the AWS cloud. CloudHSM delivers all the benefits of traditional HSMs including secure generation, storage, and management of cryptographic keys used for data encryption that are controlled and accessible only by you.
As a managed service, it automates time-consuming administrative tasks such as hardware provisioning, software patching, high availability, backups and scaling for your sensitive and regulated workloads in a cost-effective manner. Backup and restore functionality is the core building block enabling scalability, reliability and high availability in CloudHSM.
You should consider using AWS CloudHSM if you require:
- Keys stored in dedicated, third-party validated hardware security modules under your exclusive control
- FIPS 140-2 compliance
- Integration with applications using PKCS#11, Java JCE, or Microsoft CNG interfaces
- High-performance in-VPC cryptographic acceleration (bulk crypto)
- Financial applications subject to PCI regulations
- Healthcare applications subject to HIPAA regulations
- Streaming video solutions subject to contractual DRM requirements
We recently released a whitepaper, “Security of CloudHSM Backups” that provides in-depth information on how backups are protected in all three phases of the CloudHSM backup lifecycle process: Creation, Archive, and Restore.