AWS News Blog
IAM Roles for AWS Elastic Beanstalk
What’s an IAM Role?
An AWS IAM (Identity and Access Management) role allows an application running on Amazon EC2 or AWS Elastic Beanstalk to act on your behalf.
A role must be assumed by an entity (the instance or the application) and is used to create a set of temporary AWS security credentials that will have the permissions specified by the role.
You can watch the following video to learn more about IAM roles:
AWS Elastic Beanstalk now supports IAM roles to make it easier for you to securely access AWS services from your application. Elastic Beanstalk already makes it easy to run your applications on AWS by automatically provisioning, configuring, and managing many AWS resources on your behalf.
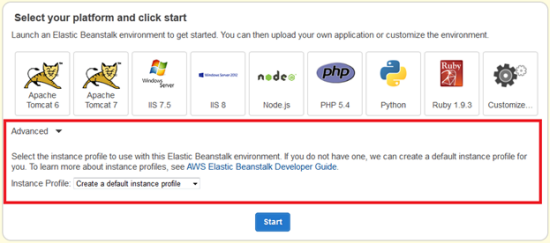
The Elastic Beanstalk management console and the eb command line can now provision an IAM role and its associated instance profile, and then assign it to your environment. You can also use an existing role if you have one that you want to share across environments.
To learn more about Elastic Beanstalk and IAM roles, visit the AWS Elastic Beanstalk Developer Guide. You may also want to read about IAM Roles for EC2 Instances
Roles and Profiles in Action
In the past, if your application needed to call an AWS service API (such as DynamoDB or CloudWatch), you most likely passed the AWS access key and secret key to your application using Elastic Beanstalk environment variables.
You start by creating a new instance profile or selecting an existing one when you create your Elastic Beanstalk application. Among other things, the instance profile contains the IAM role:
With IAM roles, temporary AWS credentials are securely provisioned on EC2 instances within your environment. These temporary credentials are automatically rotated for you multiple times per day. To use the credentials with an AWS SDK, you simply initialize the client of your choice and the AWS SDK will do the rest. Heres an example that puts a data point into CloudWatch:
// Notice I didn’t have to pass any credentials
AmazonCloudWatchClient client = new AmazonCloudWatchClient ( ) ;
// Record the metric data where numOfUsers is tracked in your application
MetricDatum dataPoint = new MetricDatum()
.withDimensions(new Dimension()
.withName(“Environment”)
.withValue(“MyProductionEnvironment”))
.withMetricName(“Users”)
.withValue(numOfUsers);
// Create the request to CloudWatch and define a namespace for my application
PutMetricDataRequest request = new PutMetricDataRequest()
.withNamespace(“myapp/prod”)
.withMetricData(dataPoint);
// Put the metrics in CloudWatch
client.putMetricData(request);
The IAM role must have the necessary permissions to call the CloudWatch API. Heres a sample policy:
“Statement” : [ {
“Effect” : “Allow” ,
“Action” : [ “cloudwatch: putMetricData” ] ,
“Resource” : “*”
}
]
}
Roll With It
This feature is available now and you can start using it today.
— Saad and Jeff
<span style=”color: #008080; font-style: italic;”>// Notice I didn’t have to pass any credentials</span><br />
AmazonCloudWatchClient client <span style=”color: #008000;”>=</span> <a style=”color: #000060;” href=”http://www.google.com/search?q=new+msdn.microsoft.com”><span style=”color: #008000;”>new</span></a> AmazonCloudWatchClient<span style=”color: #008000;”>(</span><span style=”color: #008000;”>)</span><span style=”color: #008000;”>;</span><br />
<br />
<span style=”color: #008080; font-style: italic;”>// Record the metric data where numOfUsers is tracked in your application</span><br />
MetricDatum dataPoint <span style=”color: #008000;”>=</span> <a style=”color: #000060;” href=”http://www.google.com/search?q=new+msdn.microsoft.com”><span style=”color: #008000;”>new</span></a> MetricDatum<span style=”color: #008000;”>(</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withDimensions</span><span style=”color: #008000;”>(</span><a style=”color: #000060;” href=”http://www.google.com/search?q=new+msdn.microsoft.com”><span style=”color: #008000;”>new</span></a> Dimension<span style=”color: #008000;”>(</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withName</span><span style=”color: #008000;”>(</span><span style=”color: #666666;”>”Environment”</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withValue</span><span style=”color: #008000;”>(</span><span style=”color: #666666;”>”MyProductionEnvironment”</span><span style=”color: #008000;”>)</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withMetricName</span><span style=”color: #008000;”>(</span><span style=”color: #666666;”>”Users”</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withValue</span><span style=”color: #008000;”>(</span>numOfUsers<span style=”color: #008000;”>)</span><span style=”color: #008000;”>;</span><br />
<br />
<span style=”color: #008080; font-style: italic;”>// Create the request to CloudWatch and define a namespace for my application</span><br />
PutMetricDataRequest request <span style=”color: #008000;”>=</span> <a style=”color: #000060;” href=”http://www.google.com/search?q=new+msdn.microsoft.com”><span style=”color: #008000;”>new</span></a> PutMetricDataRequest<span style=”color: #008000;”>(</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withNamespace</span><span style=”color: #008000;”>(</span><span style=”color: #666666;”>”myapp/prod”</span><span style=”color: #008000;”>)</span><br />
<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>withMetricData</span><span style=”color: #008000;”>(</span>dataPoint<span style=”color: #008000;”>)</span><span style=”color: #008000;”>;</span><br />
<br />
<span style=”color: #008080; font-style: italic;”>// Put the metrics in CloudWatch</span><br />
client<span style=”color: #008000;”>.</span><span style=”color: #0000FF;”>putMetricData</span><span style=”color: #008000;”>(</span>request<span style=”color: #008000;”>)</span><span style=”color: #008000;”>;</span></div>