Risk Management for SMB Business Leaders: Guidance for Compliance on AWS
by Kunle Adeleke, John Sol, and Pichaimani Rajesh Kumar on 09 OCT 2024 | Thought Leadership
Overview
Integrating robust cybersecurity measures offers small and medium-sized businesses (SMBs) a valuable opportunity to enhance their operations and competitiveness. By prioritizing security and compliance, SMB leaders can protect valuable assets, build trust with customers and partners, and potentially unlock new business opportunities.
The National Institute of Standards and Technology’s (NIST) Cybersecurity Framework (CSF) is a common security framework used by both public and private sectors to establish a strong security posture. Adopting NIST recommendations will help SMBs meet industry standards such as Payment Card Industry (PCI), System and Organization Controls (SOC), and the Health Insurance Portability and Accountability Act (HIPAA). In this post, we will examine NIST, the Institute of Internal Audit’s (IIA’s) Three Lines Model to manage compliance, and a way to architect this using Amazon Web Services (AWS).
Business drivers and context
NIST is a government entity, part of the U.S. Department of Commerce, with a mission to “promote innovation and industrial competitiveness by advancing measurement science, standards, and technology in ways that enhance economic security and improve our quality of life.” NIST’s CSF is often used by businesses to manage security risk to conduct business with the U.S. Federal government.
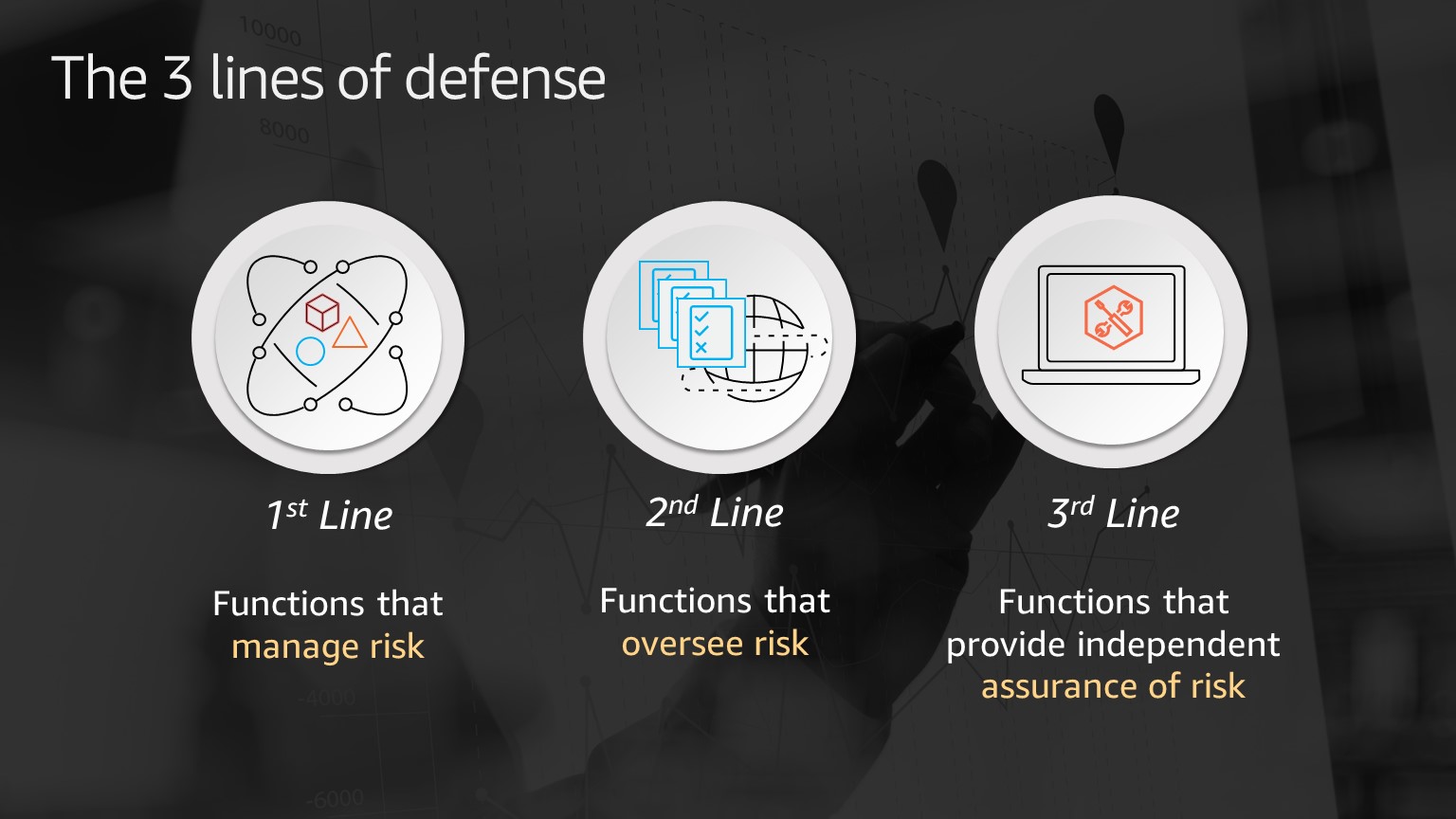
The Three Lines Model is a framework to help business leaders manage security and compliance risk and may be used to help ensure compliance with NIST standards or other standards such as PCI, SOC, etc.
We understand that navigating compliance requirements can be a challenging process. It often necessitates specialized expertise and a thorough understanding of regulatory frameworks to successfully implement compliance initiatives.
To help our customers meet security and compliance requirements, AWS provides a Global Security and Compliance Acceleration program that can help a customer find an AWS Partner Network (APN) partner to accelerate compliance.
Common compliance use cases
We’ve seen our SMB customers focus on three common use cases:
- How to automate compliance management and manage risk
IIA’s first line functions are responsible for delivering products and services to customers and operating the business. First line functions manage risk through risk-based decision making and application of resources. When creating, delivering, and operating products and services, risk should be managed throughout the lifecycle and mitigated as early as possible. Tooling is important to provide the requisite information for decision making and implementing resultant actions. Examples include creating security policies that implement separation of duties and least-privilege access to sensitive information. Or following the four-eyes principle (or two person review) to guard against fraud and reduce risk in highly secure activities. - How to implement continuous oversight and oversee risk
IIA’s second line functions are responsible for providing complementary services to first line functions to manage risk. Chief Risk Officers (CRO) and Chief Compliance Officers (CCO) are typically second line roles. Second line functions include specialists that are responsible for defining and implementing risk management practices, defining and ensuring compliance with applicable laws and regulations, cybersecurity, and internal controls. First line and second line functions work together to ensure that risk is managed effectively and with a return on investment (ROI) that maximizes business value. Examples include auditing user activity, recording resource configurations and monitoring it for compliance with standards, etc. - How to assess and independently gather assurance of risk management
IIA’s third line functions are independent of first and second line functions and provide objective assessment and assurance of risk management. Third line functions are responsible for verifying compliance with standards such as NIST. As such, first and second line functions collect and present evidence of compliance to third line functions. Examples include automatically collecting evidence, such as audit logs and configuration compliance reports, to prove compliance with NIST standards. All three lines should be implemented and considered as a cost of doing business.
Compliance capabilities
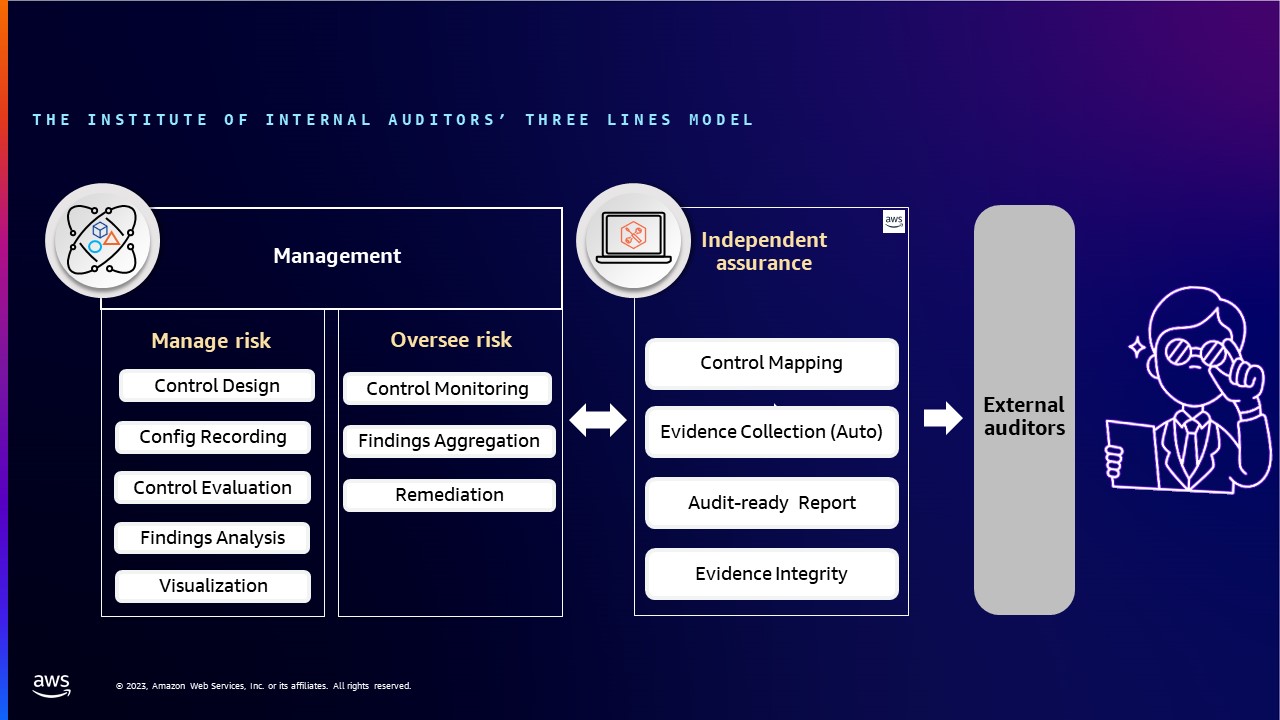
Using the IIA’s Three Lines Model helps craft a view of few of the core capabilities needed to manage, oversee, and provide assurance.
NIST CSF
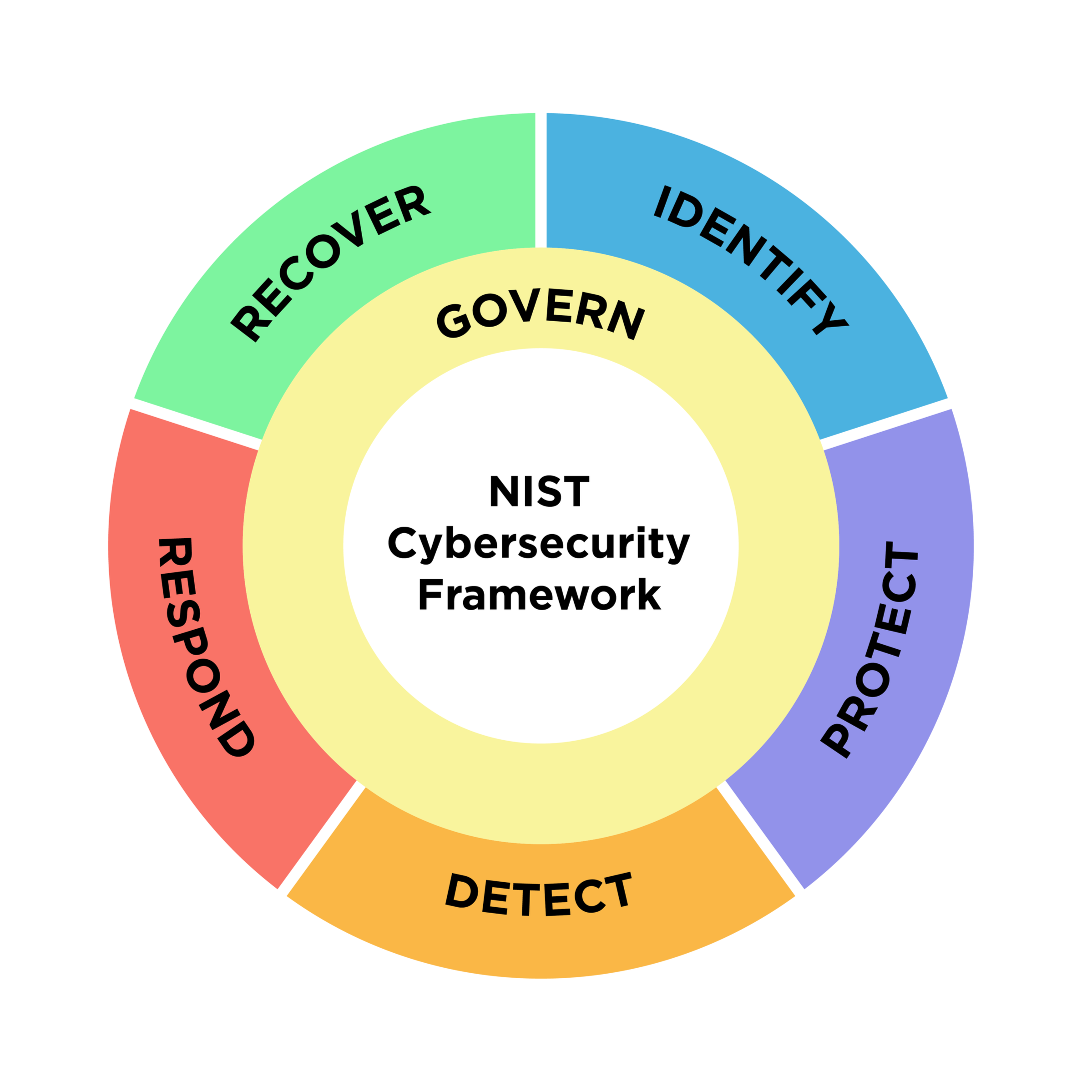
The NIST CSF 2.0 outcomes is arranged into six core functions. The outcomes described are not a prescriptive list of actions; rather, they represent goals that organizations should aim for. The specific steps taken to accomplish each outcome, and the individuals responsible for those steps, will differ depending on the organization and use case.
- Govern: The organization’s cybersecurity risk management strategy
- Identify: The organization’s current cybersecurity risks are understood
- Protect: Safeguards to manage the organization’s cybersecurity risks are used
- Detect: Possible cybersecurity attacks and compromises are found and analyzed
- Respond: Actions regarding a detected cybersecurity incident are taken
- Recover: Assets and operations affected by a cybersecurity incident are restored
Mapping of the lines of defense with NIST framework
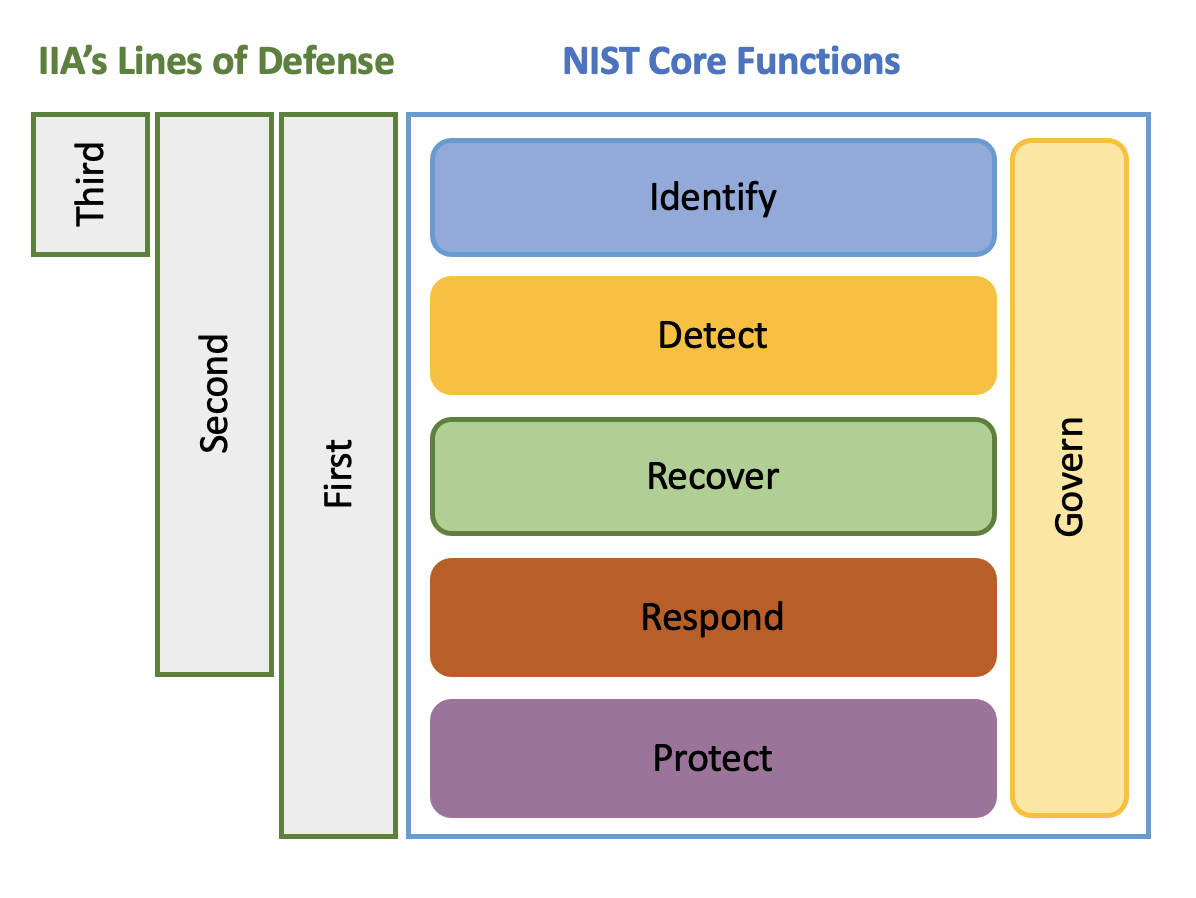
The IIA’s Three Lines Model and the NIST CSF are both frameworks designed to help organizations manage risks, but they have different focuses and approaches. However, they can be merged into one framework.
Sample use case for NIST compliance
Assume an SMB retail customer at the initial or foundational level of security implementation. Its board of directors realizes a level of security policy must be implemented soon to enhance their operational efficiency, reputation, and market competitiveness. This customer would like to take proactive steps to follow certain compliance standards and begins the implementation process with the goal to achieve 80 percent to 90 percent of their organizational standards.
The Landing Zone Accelerator on AWS helps customers deploy a foundational set of capabilities designed to align with AWS best practices and multiple global compliance frameworks. With this AWS solution, SMBs can better manage and govern their multi-account environments with highly-regulated workloads and complex compliance requirements. When used in coordination with other AWS services, it provides a comprehensive, low-code solution across more than 35 AWS services.
For existing customers or customers exploring migrating their workload to AWS, AWS provides foundational set of capabilities that is designed to align with industry best practices and multiple global compliance frameworks to accelerate achieving security compliance. This is achieved through automation of risk management activities, data security suitable for target data classification, and provision of foundational infrastructure for compliance.
AWS provides tools that customers can use to implement the Three Lines Model for compliance governance. By using these tools, customers avoid the expense of building compliance tools and integrating them into the AWS environment. Using NIST as an example, this document provided a reference architecture for NIST compliance using AWS native services.
Next steps
Let us help you develop an automated compliance strategy that can help manage your business risks. Learn more about compliance on AWS and contact an SMB expert to learn more.
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages