Implementing Zero Trust security: A practical approach for SMBs
by Ramesh Chidirala, Sr. Solutions Architect, AWS, Deepthi Paruchuri, Sr. Solutions Architect, AWS, Henrique Trevisan, Sr. Solutions Architect, AWS, and Yeswanth Narra, Sr. Technical Account Manager, AWS | 31 May 2024 | Thought Leadership
Overview
In today’s digital landscape, traditional network-based security approaches are no longer sufficient to protect systems and data. With users, applications, and workloads spread across various environments, businesses of all sizes need a security model that does not rely on network location as the sole factor for granting access.

What is a Zero Trust security model?
A Zero Trust security model is based on the principle of “never trust, always verify.” It uses identity and network capabilities together to break down traditional security silos and make integrated access decisions based on correlated data. It focuses on providing granular, policy-based access controls for systems and data based on factors such as identity and device posture regardless of the user’s location as outlined:
- With identity and access management (IAM), you can control who is authenticated (signed-in) and authorized (has permissions) to use resources.
- IAM database authentication enhances security by eliminating the need to store database credentials and centralizes database access management.
- Using trusted identity propagation, simplifies data access management for users, auditing, and improves the sign-on process.
- Verified access provides secure access to business applications without a virtual private network (VPN)
Some use cases include secure access to your most-used business apps, managing work devices remotely, and confirming who on your team can view confidential data.”
Zero Trust has gained significant traction since President Biden’s 2021 Executive Order mandating federal agencies to adopt Zero Trust architecture. The global Zero Trust Security Market is projected to grow rapidly from $27.4B USD in 2022 to $60.7B USD by 2027, at a CAGR of 17.3 percent, driven by heightened cybersecurity concerns and regulatory requirements.
How can SMBs adopt a Zero Trust security model?
Adopting a Zero Trust model does not require a complete overhaul of security systems. This allows SMBs to gain major security advantages with a relatively small upfront investment and ongoing operational costs.
Principles and components of a Zero Trust security model
- Principles: Zero Trust assumes any user or device requesting access could be an increased risk. It verifies every access attempt and grants only the least privilege needed to complete a task.
- Components: Strong identity and access management (IAM), multi-factor authentication (MFA), continuous monitoring, and micro-segmentation of networks are all key components.
Taking action: a step-by-step guide
- Inventory and classify: Identify all data, applications, and devices in your environment. Classify them based on sensitivity.
- Implement Multi-Factor Authentication (MFA): Make MFA mandatory for all user accounts, including privileged ones.
- Enforce least privilege access: Grant users access only to the specific resources they need for their job functions.
- Secure devices: Implement endpoint security solutions and enforce device hygiene policies.
- Segment your network: Divide your network into smaller zones to limit lateral movement in case of inadvertent access.
- Monitor continuously: Actively monitor user activity and network traffic for suspicious behavior.
Key considerations and best practices
- Start small, scale gradually: Begin with a few key areas and gradually expand your scope.
- User education and training: Educate employees about Zero Trust principles and best practices for secure access.
- Seek expert guidance: Consider consulting with an AWS Partner, who can help with planning, implementation, and enablement over a period of time.
- Leverage cloud-based solutions: Cloud security tools can simplify implementation for SMBs.
- Regular review and updates: Continuously evaluate your implementation and update policies as needed.
By following these steps and best practices, SMBs can significantly improve their security posture.
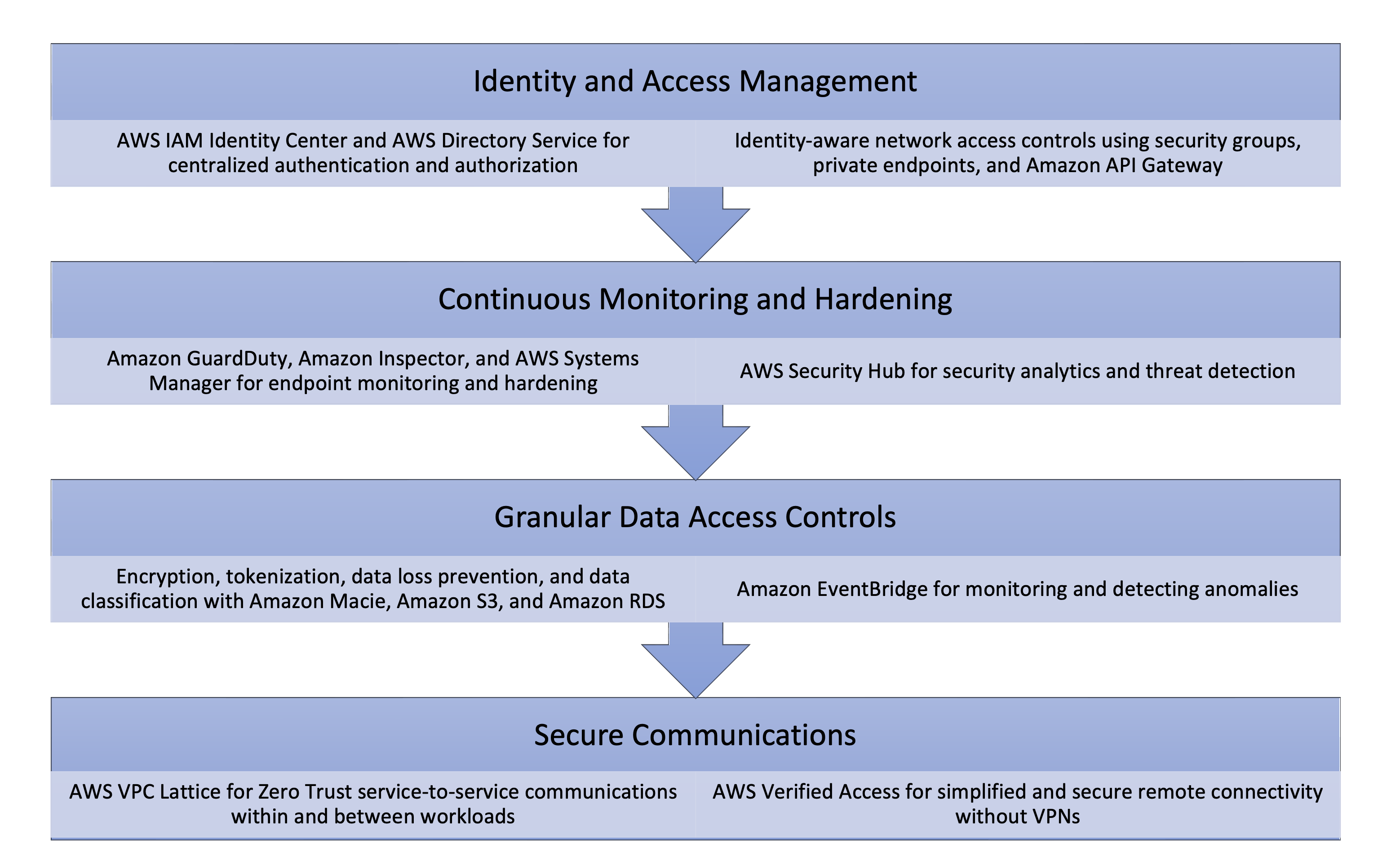
Key AWS Zero Trust capabilities
AWS provides a comprehensive set of Zero Trust capabilities (outlined in diagram) to help businesses implement granular access controls, centralized identity management, continuous monitoring, security analytics, and secure service-to-service communication. By using these native services, organizations can adopt a Zero Trust approach to securing their cloud environment without having to build custom solutions from scratch. These capabilities combined with data protection and durable data storage services enable businesses of all sizes safeguard their operations and maintain customer trust.
Roles and responsibilities in adopting a Zero Trust security model
The adoption of a Zero Trust security model involves a top-down, bottom-up approach, with leadership driving the initiative, security teams implementing the necessary controls and architectures, developers focusing on core application logic, and end-users benefiting from improved security and access facilitated by Zero Trust principles. AWS recognizes that no two SMBs are the same, whether your business has existing in-house teams to manage these responsibilities, or you need to leverage support, an AWS Partner has demonstrated expertise and proven customer success to help .
Conclusion
Implementing a Zero Trust Security Model is no longer an option but a necessity for SMBs. Adoption is not a one-time effort but an ongoing journey that requires continuous evaluation. By staying vigilant and proactive, SMBs can ensure the long-term security and success of their businesses. Embrace Zero Trust today and safeguard your organization’s future. Speak with an AWS SMB cloud expert or seek out a free consultation from our vetted AWS Partner Network consultants.
Did you find what you were looking for today?
Let us know so we can improve the quality of the content on our pages