AWS Architecture Blog
Field Notes: Enabling Guardrails in New AWS Regions the AWS Control Tower Supports
Originally published March 2020 to the Field Notes blog, and updated in January 2021, to highlight that AWS Control Tower supports the updating of enrolled accounts from the dashboard. Follow the instructions from Update existing OUs and accounts in addition to this blog.
For the first time since the launch of AWS Control Tower, we are happy to add support for the AWS Sydney Region. The AWS Control Tower service released a new version with additional AWS Region Support. In order to enable the newly supported AWS Regions, existing customers will need to update their AWS Control Tower landing zone to the most current version.
Although this blog content refers to the Sydney Region, the instructions provided are also applicable to five additional supported Regions (Canada, Frankfurt, Stockholm, London, Singapore were added in Nov 2020).
Version 2.3 of the AWS Control Tower landing zone extends AWS Control Tower support to the Sydney Region. If you already have an AWS Control Tower setup and you plan on running workloads in the Sydney Region, you must update your AWS Control Tower landing zone to version 2.3, via the Settings page of AWS Control Tower. If you have launched AWS Control Tower after the launch of the Sydney Region support (March 6, 2020), then you will be automatically running on the latest version of the AWS Control Tower landing zone, which supports the Sydney Region (as of this writing – Version 2.3).
If you launched AWS Control Tower’s landing zone before March 6, 2020, and would like to immediately take advantage of the Sydney Region and apply new detective guardrails to your existing AWS Organizations organizational units (OUs) that are under AWS Control Tower management. Then you must also update all existing Account Factory accounts in your AWS Control Tower environment.
In this blog, I show you how to update your accounts in an automated fashion.
Background
Here’s a quick review of some terms used in this post:
- An update script is a Python program that interacts with multiple AWS services, identify, and update the existing account factory accounts in AWS Control Tower environment.
- An AWS Account Factory account is an AWS account provisioned using account factory in AWS Control Tower.
- AWS Cloud9 is a cloud-based integrated development environment (IDE) that lets you write, run, and debug your code with just a browser.
- The tag is a custom attribute label that you add to an AWS resource to make it easier to identify, organize, and search for resources.
- AWS Service Catalog allows you to centrally manage commonly deployed IT services. In the context of this blog, account factory uses AWS Service Catalog to provision new AWS Accounts.
- A provisioned product is an instance of the product that is provisioned by AWS Service Catalog. In this post, any new AWS account created used account factory is a provisioned product.
- AWS Organizations helps you centrally govern your environment as you grow and scale your workloads on AWS.
- AWS Single Sign-On (SSO) makes it easy to centrally manage access to multiple AWS accounts. It also provides users with single sign-on access to all their assigned accounts from one place.
Prerequisites
- You need to log into the AWS Control Tower master account with AWSAdministratorAccess role if using AWS SSO or equivalent permissions, if you are using other federations.
- Optionally, launch AWS Cloud9. Here you can run a Python boto3 script where sessions can securely run for longer duration.
- If you decide to skip AWS Cloud9, ensure you have
python 3.7or higher andboto3 version 1.12.33or higher in your compute environment.
- If you decide to skip AWS Cloud9, ensure you have
- Increase the timeout of your AWS Cloud9 environment to 1 week, the max supported timeout.
- Go to Preferences > PROJECT SETTINGS > PROJECT > EC2 Instance and change Stop my environment to After a week. Alternatively, you could select this setting while deploying AWS Cloud9 environment.
- This solution uses a dummy AWS SSO user while it updates the provisioned products. Alternatively, you could use your own secured email address. If you decide to go with latter, you must Identify a secure SSO user with restricted access.
IMPORTANT: The credentials used to deploy this solution is given AWSAdminstratorAccess to all the updated accounts using this solution. We highly recommend deleting the user once your accounts have been updated.
Following are few additional things you need to know about this solution.
- As mentioned in the prerequisites, this solution creates a dummy SSO user. The cleanup steps section of this blog walks you through the deletion of the dummy SSO user. However, the SSO user will have Administrator access to all the updated account factory accounts while updating the remaining account factory accounts as part of this solution.
- Once successfully updated, the account will have an additional tag with a key: value pair
PP_UPDATE:TRUE. This tag helps in identifying the accounts that are not updated successfully. Please do not delete this tag, while the accounts are still being updated. - In addition, the account tags mentioned above will not be automatically removed after the update process completes. You may choose to delete them manually using the instructions provided at the cleanup steps section of this post.
How it works
The following diagram shows the overview of the solution.

As a Control Administrator, you perform the following tasks:
- Log in to your AWS Control Tower master account and launch an AWS Cloud9 environment
- Open AWS Cloud9 Service Console.
- Launch an environment AWS Cloud9 > Your environments > Create environment.
- Name the environment as needed and choose Next step.
- Change Cost-saving setting to After a week and leave all other defaults and choose Next step.
- Review the options selected and choose Create environment.
- Download the update script in to your AWS Cloud9 environment.
$ wget https://raw.githubusercontent.com/aws-samples/aws-control-tower-reference-architectures/master/customizations/AccountFactory/BatchUpdate/update_pp.py- Execute the script in your AWS Cloud9 environment.
$ python update_pp.py - The script will sequentially update all the existing account factory accounts, one at a time, in your AWS Control Tower environment. Each account update takes up to 20 minutes. Depending on the number of accounts you have in your environment, the script could run for a longer duration. Wait for the script to complete updating all the accounts.
- If the script is interrupted for some reason, wait for the last provisioned product status change from
UNDER_CHANGEtoAVAILABLEorTAINTEDbefore restarting the script. Restarting the script while an account is actively updated, will result in following message and the script will exit.
$ python update_pp.py
Update in progress. Allow UNDER_CHANGE or PLAN_IN_PROGRESS stacks to complete:['SC-Launch-for-VinjakSB33']- When you restart an interrupted script, it will check and skip the previously updated accounts based of the resource tag
PP_UPDATEon each account.
$ python update_pp.py
Account – 111122223333 Skipped, Updated already
Account – 444455556666 Skipped, Updated already
Account – 777788889999 Skipped, Updated already
Updating Provisioned Account : 666666666666
Status: UNDER_CHANGE. Waiting for: 6.0 minutes before checking back To check the tag on each account, go to AWS Organizations Console, choose the AWS account you want to check, and look under tags section on the right side bar.
Congratulations! You have successfully updated all your existing account factory accounts and enabled guardrails on the new Region that AWS Control Tower supported. You could verify this by using below steps:
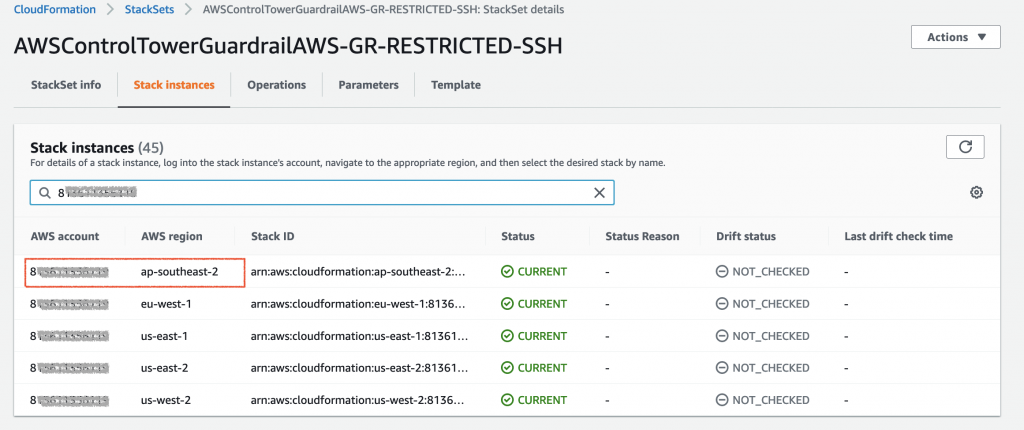
- Go to AWS CloudFormation StackSet console, and choose the StackSet that starts with
AWSControlTowerGuardrailAWS, and select the Stack Instances tab. - You could see the guardrails enabled on the newly supported Region for one of your account factory accounts.
Cleanup steps
On successful completion of updating the existing account factory accounts, you could clean up the below resources used for this solution.
- Delete the AWS Cloud9 environment you created to run update script. This will prevent any future billing charges.
- Delete the AWS SSO user (default:
noreply@example.com).- Go to AWS SSO Console, and choose Users.
- Select the user you want to delete and choose Delete users.
- You could optionally delete the tags on AWS accounts that are set by the update process. Please note, that if you rerun the script, the accounts without the
PP_UPDATEtag will be whitelisted for another update.
Conclusion
In this post, I have shown you how to enable your AWS Control Tower accounts to recognize and support a new Region implementation. As AWS Control Tower continues to add additional Region support, there is a need to update your AWS Control Tower landing zone. When you update the landing zone version, the update process will baseline your accounts to operate actively in the new Region. It will not update the existing Account Factory accounts within your organizational units (OUs) that are managed by AWS Control Tower. By using the procedure in this post, you now have an automated method for updating your accounts.