AWS Security Blog
Category: How-To
How to Configure Rate-Based Blacklisting with AWS WAF and AWS Lambda
Note from July 3, 2017: The solution in this post has been integrated into AWS WAF Security Automations, and AWS maintains up-to-date solution code in the companion GitHub repository. One security challenge you may have faced is how to prevent your web servers from being flooded by unwanted requests, or scanning tools such as bots and […]
How to Set Up DNS Resolution Between On-Premises Networks and AWS Using AWS Directory Service and Microsoft Active Directory
In my previous post, I showed how to use Simple AD to forward DNS requests originating from on-premises networks to an Amazon Route 53 private hosted zone. Today, I will show how you can use Microsoft Active Directory (also provisioned with AWS Directory Service) to provide the same DNS resolution with some additional forwarding capabilities. […]
How to Set Up DNS Resolution Between On-Premises Networks and AWS Using AWS Directory Service and Amazon Route 53
As you establish private connectivity between your on-premises networks and your AWS Virtual Private Cloud (VPC) environments, the need for Domain Name System (DNS) resolution across these environments grows in importance. One common approach used to address this need is to run DNS servers on Amazon EC2 across multiple Availability Zones (AZs) and integrate them […]
How to Help Protect Sensitive Data with AWS KMS
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. AWS Key Management Service (AWS KMS) celebrated its one-year launch anniversary in November 2015, and […]
How to Record and Govern Your IAM Resource Configurations Using AWS Config
AWS Config recently added the ability to record changes to the configuration of your AWS Identity and Access Management (IAM) users, groups, and roles (collectively referred to as IAM entities) and the policies associated with them. Using this feature, you can record configuration details for these IAM entities, including details about which policies are associated […]
How to Automatically Update Your Security Groups for Amazon CloudFront and AWS WAF by Using AWS Lambda
July 29, 2025: This blog post is outdated. Use CloudFront’s managed prefix list for Security Groups instead of the Lambda solution. CloudFront now supports VPC origins, allowing secure connectivity to private VPC resources. For details on managed prefix lists, see this post. For VPC origins implementation guide, refer to this post. April 1, 2021: Before […]
How to Set Up SSO to the AWS Management Console for Multiple Accounts by Using AD FS and SAML 2.0
AWS supports Security Assertion Markup Language (SAML) 2.0, an open standard for identity federation used by many identity providers (IdPs). SAML enables federated single sign-on (SSO), which enables your users to sign in to the AWS Management Console or to make programmatic calls to AWS APIs by using assertions from a SAML-compliant IdP. Many of […]
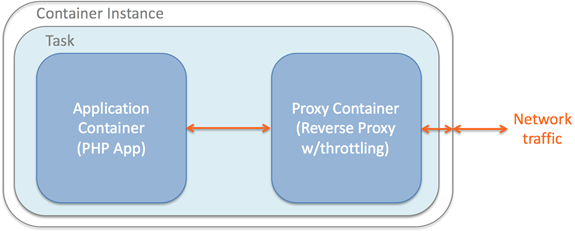
How to Govern Your Application Deployments by Using Amazon EC2 Container Service and Docker
Governance among IT teams has become increasingly challenging, especially when dealing with application deployments that involve many different technologies. For example, consider the case of trying to collocate multiple applications on a shared operating system. Accidental conflicts can stem from the applications themselves, or the underlying libraries and network ports they rely on. The likelihood […]
How to Set Up Federated API Access to AWS by Using Windows PowerShell
When accessing AWS resources in an organization, we recommend that you have a standard and repeatable authentication method for purposes of security, auditability, compliance, and the capability to support role and account separation. As part of my AWS Professional Services engagements, I have helped AWS customers establish such an authentication mechanism via federated access to […]
How to Use a Single IAM User to Easily Access All Your Accounts by Using the AWS CLI
Many AWS customers keep their environments separated from each other: development resources do not interact with production, and vice versa. One way to achieve this separation is by using multiple AWS accounts. Though this approach does help with resource isolation, it can increase your user management because each AWS account can have its own AWS […]