AWS Storage Blog
Maintain your compliance requirements by using AWS PrivateLink with Amazon EFS
Amazon Elastic File System (Amazon EFS) serves tens of thousands of companies across the world, in every industry and vertical. Many of our customers have very specific network and network management policies, based on compliance or regulatory requirements. Today, I will show you how you can meet or enhance your compliance posture by using AWS PrivateLink to create Amazon VPC Endpoints for Amazon EFS.
Amazon EFS provides a simple, scalable, elastic NFS file service for Linux-based workloads for use with AWS Cloud services and on-premises resources. AWS PrivateLink simplifies the security of data shared with cloud-based applications by preventing any traffic from traversing the public Internet, and provides private connectivity between VPCs, AWS services, and on-premises applications, securely on the Amazon network.
Amazon EFS already supports industry standard TLS to secure encryption of data in transit, whether or not you use AWS PrivateLink. Many of our customers also use the Amazon EFS APIs to automate the creation and management of their EFS file systems. You can now use Amazon VPC Endpoints to call Amazon EFS APIs from VPCs that are not connected to the public Internet, without using public IP addresses and without leaving Amazon’s network. This helps you to meet your applicable security and compliance requirements and access services hosted on AWS easily and securely by keeping your network traffic within the AWS network.
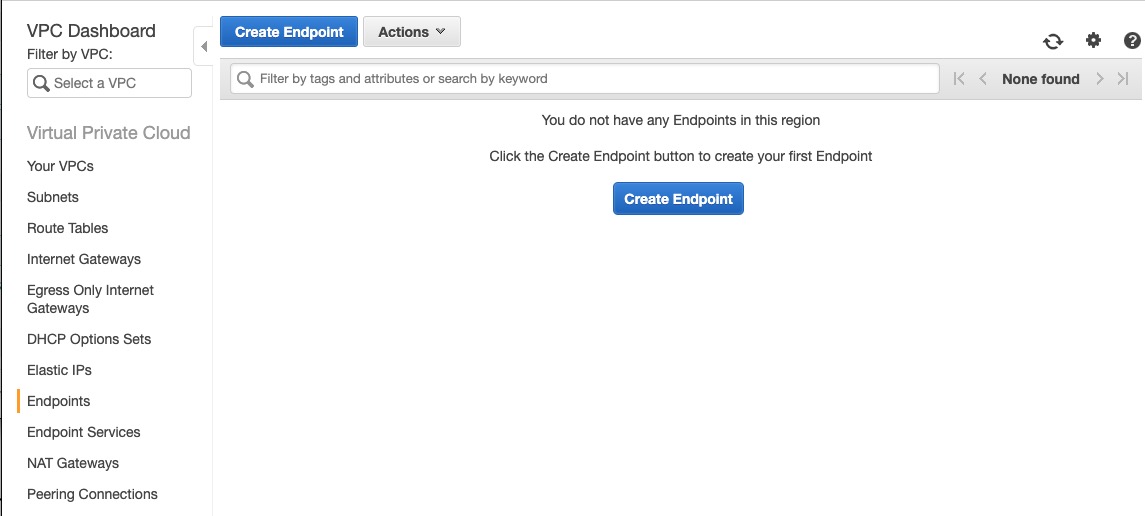
To use AWS PrivateLink, create an interface VPC endpoint for Amazon EFS in your VPC using the Amazon VPC console, SDK or CLI. I’ll show you how to use the console to get started.
From the VPC console, select Endpoints and Create a New Endpoint.
Select Amazon EFS from the list of supported services, and select the endpoint for EFS.

After selecting the service endpoint, you can pick from your existing VPCs and subnets, select whether you will be using private DNS for your VPC selection, and either select an existing security group, or Create a new security group.

You can also create a custom VPC Endpoint policy. A default policy is provided, as shown below. Select Create endpoint to complete the process.
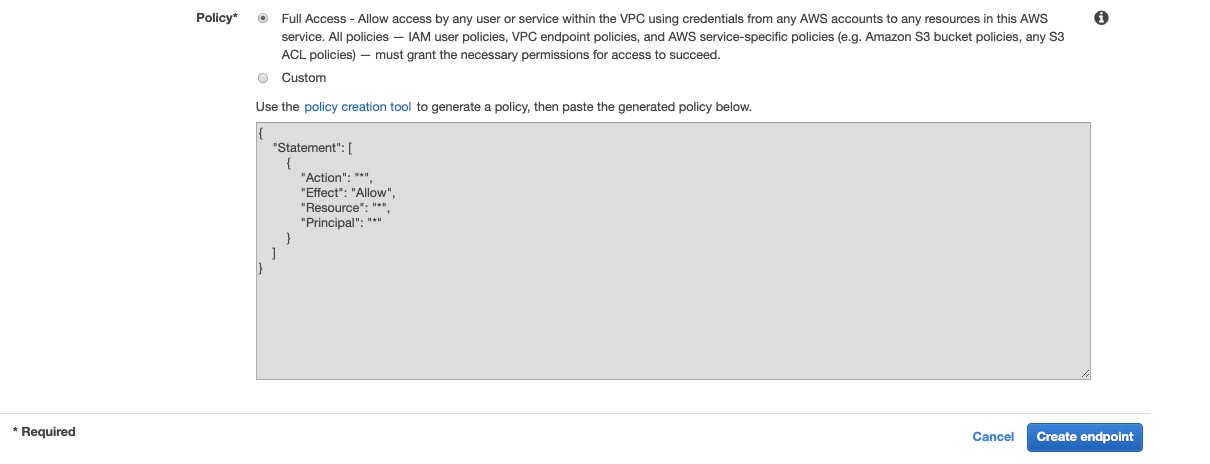
You have now created an Elastic Network Interface (ENI) in your subnet with a private IP address that serves Amazon EFS API requests. You can also access the VPC endpoint from on-premises environments or from other VPCs using AWS VPN, AWS Direct Connect, or VPC Peering.
You can view and manage your VPC endpoint settings, and your VPC endpoint policies from the VPC console at any time.

We would love to hear your feedback in the comments section below. To learn more, visit the Amazon EFS website, or get started in the AWS Console.