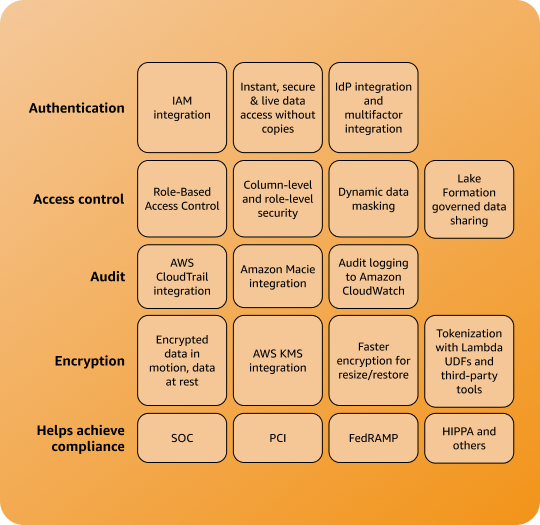
Amazon Redshift Security & Governance
Protect your data through Industry-leading security and access management features, out of the box at no additional cost
Overview
Benefits of Amazon Redshift
-
Amazon Redshift works with AWS Secrets Manager to generate and manage your admin credentials. AWS Secrets Manager supports the entire lifecycle maintenance for your Amazon Redshift admin credentials, relieving you from complex credential management activities. Control network access to your data warehouse cluster through firewall rules. Using Amazon Virtual Private Cloud (VPC), isolate your Redshift data warehouse cluster in your own virtual network. You can keep your data encrypted at rest and in transit. AWS is architected to be the most secure global cloud infrastructure on which to build, migrate, and manage applications and workloads.
-
Integration with AWS IAM Identity Center enables you to use third-party Identity Providers (IdP) for a seamless single sign-on experience. Role-based Access Control (RBAC) simplifies security permissions in Amazon Redshift and controls end user access to data at a broad or granular level based on permission rights and data sensitivity. Restrict access to data at row or column level and based on roles with column-level security (CLS) and row-level security (RLS) controls. Combine these controls to enforce granular access to data. Use dynamic data masking in Amazon Redshift to selectively mask personal information data at query time based on job role/permission rights and level of data sensitivity.
-
Amazon Redshift integrates with AWS CloudTrail to audit all Redshift API calls. Amazon Redshift logs all SQL operations, including connection attempts, queries, and changes to your data warehouse. It enables faster delivery of audit logs for analysis by minimizing latency while also including Amazon CloudWatch as a new log destination. You can choose to stream audit logs directly to Amazon CloudWatch for real-time monitoring. Amazon Redshift offers a strong compliance framework and advanced tools and security measures that customers can use to evaluate, meet, and demonstrate compliance with applicable legal and regulatory requirements.
-
Simplify governance of Amazon Redshift Data Sharing with AWS Lake Formation to centrally manage data being shared across your organization. With AWS Lake Formation governing data sharing, you now have better visibility and control of data being shared across accounts within your organization. Data administrators can define policies once and execute them consistently across Amazon Redshift Data Shares to improve the security of your data, and to manage granular entitlements.
Customers
LexisNexis
"We are delighted about the row level security (RLS) feature within Amazon Redshift. We had to apply workarounds through views to handle our RLS requirements. With the new RLS within Amazon Redshift, it allows us to create/attach granular policies that apply to the entire set of users/roles and ensure they comply with the organization's standards for data security, compliance, and privacy.”
Deepak Senthilkumar, Director of Software Engineering – LexisNexis
Baffle
Baffle delivers data-centric protection for enterprises via a data security platform that is transparent to applications and unique to data security.
“Our mission is to seamlessly weave data security into every data pipeline. Previously, to apply data masking to an Amazon Redshift data source, we had to stage the data in an Amazon S3 bucket. Now, by utilizing the Amazon Redshift Dynamic Data Masking capability, our customers can protect sensitive data throughout the analytics pipeline, from secure ingestion to responsible consumption reducing the risk of breaches.”
Ameesh Divatia, CEO & co-founder of Baffle
United Airlines
United Airlines is in the business of connecting people and uniting the world.
"As a data-driven enterprise, United is trying to create a unified data and analytics experience for our analytics community that will innovate and build modern data-driven applications. We believe we can achieve this by building a purpose-built data mesh architecture using a variety of AWS services like Athena, AuroraDB, Amazon Redshift, and Lake Formation to simplify management and governance around granular data access and collaboration."
Ashok Srinivas, Director of ML Engineering and Sarang Bapat, Director of Data Engineering – United Airlines

EnergyAustralia
EnergyAustralia is an Australian energy retailer and generator with 1.6 million customers across eastern Australia that today focuses on keeping the lights on for its customers through its energy generation facilities, whilst leading the delivery of the clean energy system of the future.
"EnergyAustralia is a leading Australian energy retailer and generator, with a mission to lead the clean energy transition for customers in a way that is reliable, affordable and sustainable for all," says William Robson, Data Solutions Design Lead, EnergyAustralia. “We enable all corners of our business with data and analytics capabilities that are used to optimize business processes and enhance our customers’ experience."
"Keeping our customers’ data safe is a top priority across our teams. In the past, this involved multiple layers of custom built security policies that could make it cumbersome for analysts to find the data they require. The new AWS dynamic data masking feature will significantly simplify our security processes so we continue to keep customer data safe, while also reducing the administrative overhead."
William Robson, Data Solutions Design Lead, EnergyAustralia