Networking & Content Delivery
Dynamic Whole Site Delivery with Amazon CloudFront
Written by Tino Tran, AWS Solutions Architect
It’s common practice to use Amazon CloudFront to accelerate the delivery of static web assets stored in Amazon Simple Storage Service (Amazon S3) to end users. CloudFront can cache content at edge locations closer to your viewers giving them greater performance, instant global reach, and higher platform availability. For Amazon Elastic Compute Cloud (Amazon EC2) origins serving dynamic and/or static content, you should also consider using CloudFront because it offers a number of additional benefits. In this blog post, we will provide an overview of the performance, security, and cost benefits you get when using CloudFront to serve dynamic and/or static assets from Amazon EC2. We will also walk through the exercise of configuring CloudFront for Amazon EC2 origins. To learn more about edge networking with AWS, click here.
Performance
- Cacheable Content. While most applications serve static content from Amazon S3, origins in Amazon EC2 that serve static content can also benefit from caching content at the edge. By leveraging the CloudFront edge locations and regional edge caches, applications can reduce the origin’s workload and bandwidth utilization while bringing content closer to viewers. This reduces the latency of serving static content.
- Global Reach. The CloudFront global network, which consists of over 100 points of presence (POP), reduces the time to establish viewer-facing connections because the physical distance to the viewer is shortened. This reduces overall latency for serving both static and dynamic content.
- Persistent Connections. CloudFront maintains a pool of persistent connections to the origin, thus reducing the overhead of repeatedly establishing new connections to the origin. Over these connections, traffic between CloudFront and AWS origins are routed over a private backbone network for reliability and performance. This reduces overall latency for serving both static and dynamic content.
- Collapsed Forwarding. During traffic spikes, CloudFront collapses simultaneous requests for cache misses before forwarding the request to your origin reducing unnecessary load to your origin.
Security
- Distributed Denial of Service (DDOS). As with other AWS services, AWS Shield Standard is included at no additional cost when you use CloudFront. CloudFront provides added protection against DDOS attacks by distributing traffic across multiple points of presence (POP) locations and filtering requests to ensure that only valid HTTP(S) requests are forwarded to backend hosts. With the CloudFront geo restrictions feature, also known as geoblocking, you can use CloudFront to isolate attacks originating from a particular geographic location.
- Encryption in Transit. You can configure CloudFront to strictly enforce SSL protocols. CloudFront integrates with AWS Certificate Manager (ACM), where you can request, upload, and manage your certificates at no additional cost. CloudFront supports both Server Name Indication (SNI) and custom dedicated IP address certificates. While HTTPS requests are charged a fraction of a penny more per request, there is no additional charge for using SNI certificates.
- Web Application Firewall (WAF). CloudFront integrates with AWS WAF, which allows you to configure rules to filter malicious requests (such as SQL injection, cross-site scripting, etc.) that may be harmful to your service. Requests are filtered inline at each POP location to minimize the latency. This extends your security perimeter to the edge, keeping threats away from your origin infrastructure.
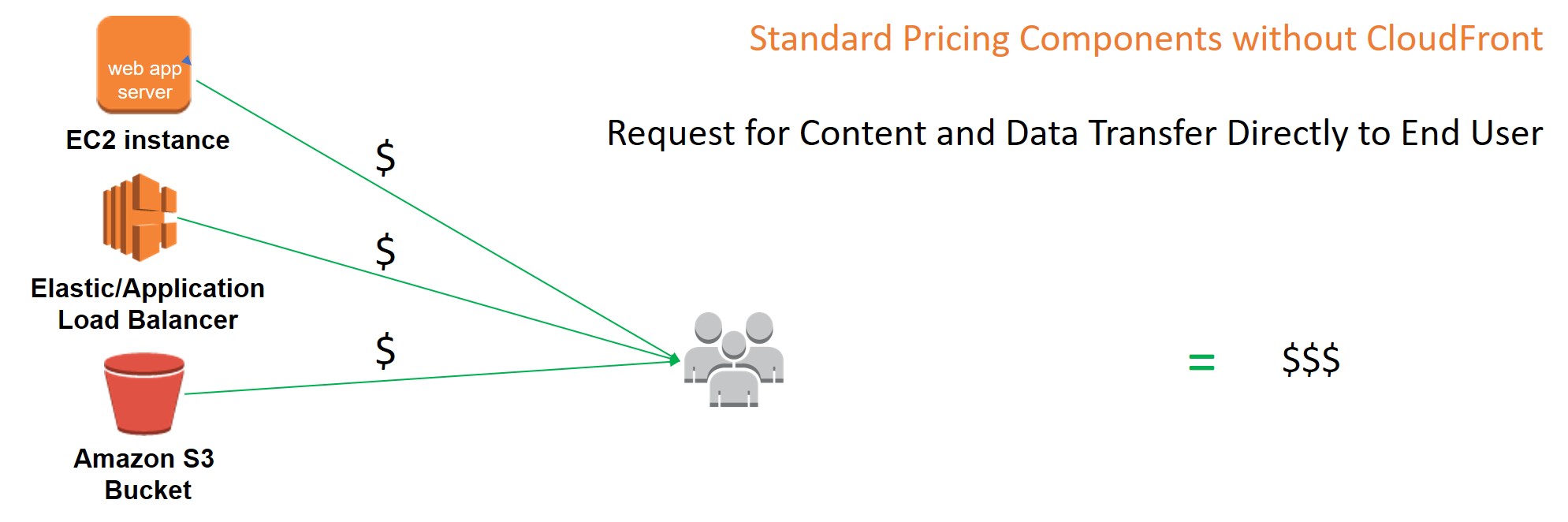
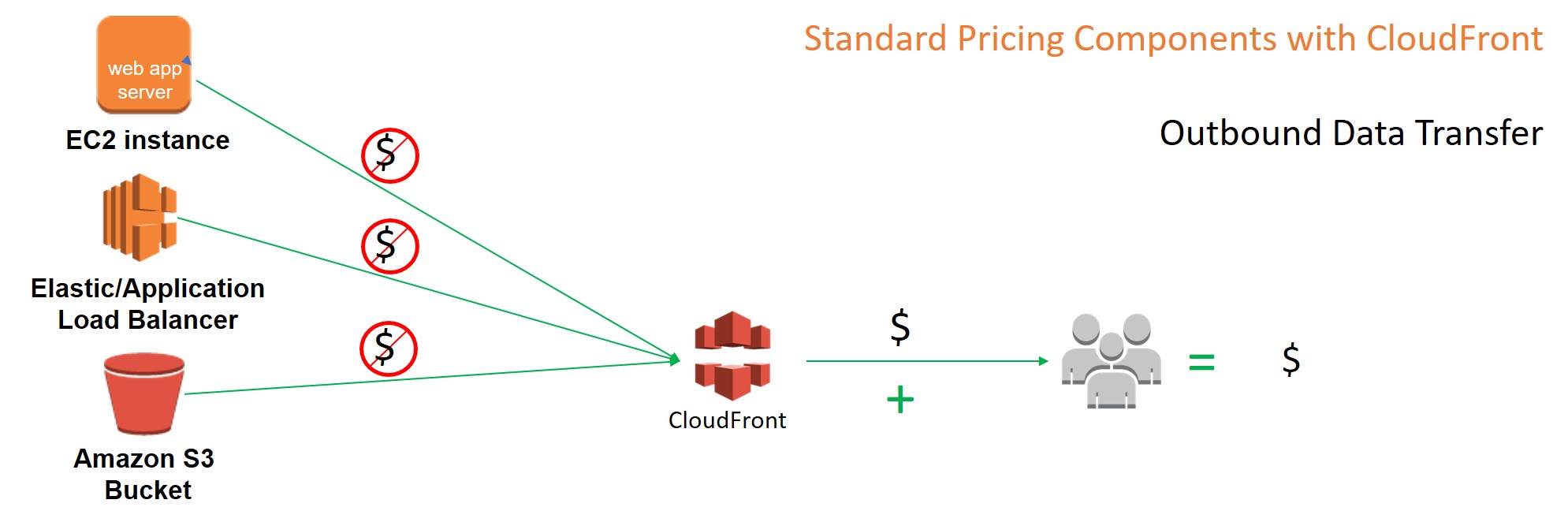
Cost
Outbound data transfer charges from AWS services to CloudFront is $0/GB. The cost coming out of CloudFront is typically half a cent less per GB than data transfer for the same tier and Region. What this means is that you can take advantage of the additional performance and security of CloudFront by putting it in front of your Application Load Balancers (ALB), AWS Elastic Beanstalk, Amazon S3, and other AWS resources delivering HTTP(S) objects for next to no additional cost. CloudFront does charge request fees per object. Check your estimated CloudFront cost in the calculator here.
Now let’s set up CloudFront for an EC2 origin
In this exercise, we will show you how to configure CloudFront to serve static and dynamic content for an origin running in Amazon EC2.
Step 1 – Create an Amazon EC2 origin
If you already have an EC2 origin with an ALB or ELB endpoint that you want to use, please skip to step 2. Otherwise, you can follow this tutorial to create a high availability Drupal website in Amazon EC2.
After completing the tutorial, you should now have an ELB endpoint for your origin.
Step 2 – Create an Amazon S3 log bucket
2.1. Go to the Amazon S3 console from the CloudFront console and choose Create Bucket.
2.2. Provide a name for the S3 bucket and choose Create.

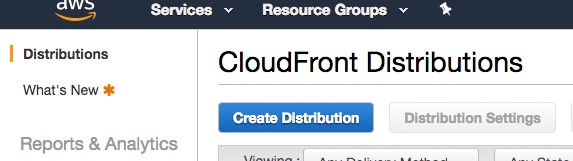
Step 3 – Create a CloudFront distribution
3.1. Go to the CloudFront console and choose Create Distribution.
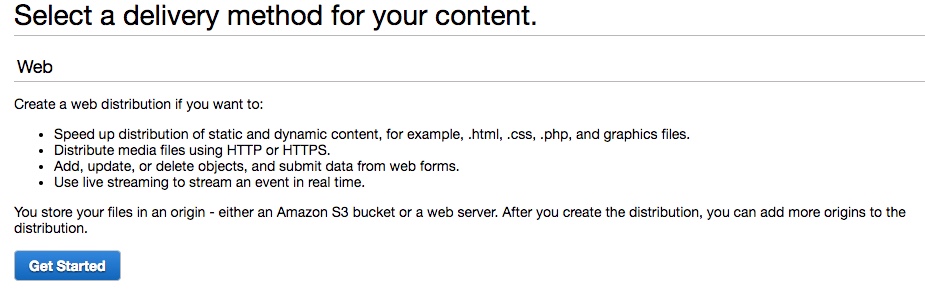
3.2. For this exercise we will create a web distribution. Choose Get Started to continue.
3.3. On the Create Distribution page, provide the following parameters:
3.4 Under Origin Settings
- Origin Domain Name: Select the ALB or ELB endpoint that you created in Step 1.
Note: You can input the FQDN hostname value associated with your origin. For convenience, the console will pre-populate with ALB/ELB endpoints that you have available on your payer account.

3.5. Under Default Cache Behaviors Settings select the following:
- Viewer Protocol Policy: Redirect HTTP to HTTPS
- Allowed Methods: Get, Head, Options, Put, Post, Patch, Delete
- Compress Object Automatically: Yes
- Leave the remaining setting to the default value
Note: We will default to using the origins cache-control headers for determining how long objects stay in the CloudFront cache. If no cache-control header is returned, in this case CloudFront will set a default Time To Live (TTL) of 24 hours.
3.6. Under Distribution Settings set the following parameters and leave the remaining at the default values:
- Logging: On
- Bucket for Logs: Select the bucket created in Step 2.
- Comment: Drupal Distribution
3.7. Choose Create Distribution.
Step 4 – Add a Cache Behavior for Dynamic (Non-cacheable) Content.
In this example, we treat content for Drupal administrators as non-cacheable.
4.1. Select the distribution you just created in the CloudFront console.
4.2. Choose the Behaviors tab and choose Create Behavior.
4.3. Provide the following parameters:
- Path Pattern: admin
- Origin: select the ELB origin created in step 1.
- Viewer Protocol Policy: Redirect HTTP to HTTPS
- Allowed Methods: Get, Head, Options, Put, Post, Patch, Delete
- Cached Based on Selected Request Headers: ALL
- Leave the remaining setting to the default value
Note: When you configure your cache behavior to forward all headers to the origin CloudFront treats the content as Dynamic, bypassing all the caching layers of the service.
4.4. Choose Create.
Congratulations! You now have a CloudFront distribution configured to accelerate your Amazon EC2 origin for both dynamic and static content. To find out more about CloudFront features, visit the Amazon CloudFront product details page.