Amazon CloudFront
CloudFront Points of Presence (PoPs)
Points of Presence (PoPs)
North America
Canada: Calgary (2), Montreal (3), Toronto (4), Vancouver (3),
Mexico: Santiago de Queretaro (10),
United States: Atlanta (29), Boston (6), Chicago (32), Columbus (5), Dallas (27), Denver (7), Houston (6), Kansas City (4), Los Angeles (21), Miami (19), Minneapolis (5), Nashville 2), Newark, New York (26), Philadelphia (4), Phoenix (4), Pittsburgh (2), Portland (4), Salt Lake City (2), San Francisco (14), Seattle (12), Tampa (3), Washington D. C. (31),
South America
Argentina: Buenos Aires (5)
Brazil: Fortaleza (6), Guarulhos (16), Rio de Janeiro (6)
Chile: Santiago (5),
Colombia: Bogota (5),
Peru: Lima (3)
Europe
Austria: Vienna (5),
Belgium: Brussels (2),
Bulgaria: Sofia (2)
Croatia: Zagreb,
Czech Republic: Prague
Denmark: Copenhagen (2)
Finland: Helsinki (7),
France: Marseille (9),Paris (15),
Germany: Berlin (8), Dusseldorf (6), Frankfurt (33), Hamburg (6), Munich (6),
Greece: Athens (2)
Hungary: Budapest (2)
Ireland: Dublin (4)
Italy: Milan (12), Rome (7),
Netherlands: Amsterdam (11),
Norway: Oslo (2),
Poland: Warsaw (6),
Portugal: LisbonRomania: Bucharest (3)
Spain: Barcelona (2), Madrid (13),
Sweden: Stockholm (4),
Switzerland: Zurich (3)
United Kingdom: London (32), Manchester (6)
Middle East:
Bahrain: Bahrain (5),
Israel: Tel Avivi (3),
Kingdom of Saudi Arabia: Jeddah (4), Riyadh (2)
Oman: Muscat (3)
Qatar: Doha (2)
Turkey: Istanbul (6),
United Arab Emirates: Dubai (4),
Africa:
Egypt: Cairo (3),
Kenya: Nairobi (3),
Nigeria: Lagos (2)
South Africa: Cape Town (2), Johannesburg (3),
Asia-Pacific
Australia: Brisbane (2), Melbourne (2), Perth, Sydney (5)
Hong Kong: Chek Lap Kok (5),
India: Bengaluru (4), Chennai (5), Kolkata (4), Maharashtra (4), Mumbai (13), New Delhi (13), Telangana (6),
Indonesia: Jakarta (8),
Japan: Narita (27), Osaka (9),
Malaysia: Kuala Lumpur (4),
New Zealand: Auckland (4),
Philippines: Manila (5)
Singapore (12)
South Korea: Seoul (10),
Taiwan: Taipei (4),
Thailand: Bangkok (5),
Vietnam: Hanoi (4), Saigon (4)
Embedded Points of Presence (PoPs)
Argentina: Buenos Aires, Cordoba, Rosario,
Brazil: Belo Horizonte, Brasalia, Campinas, Centro, Curitiba, Cuiaba, Duque de
Caxias, Florianapolis, Fortalexa, Franca, Goiania, Guara, Joao Pessoa, Juazeiro do
Norte, Manaus, Natal, Pedreira, Porto Alegre, Recife, Rio de Janeiro, Sao Paulo,
Salvador, Uberlandia,
Canada: Brampton, Burnaby, Calgary, Edmonton, Fort McMurray, Halifax,
Hamilton, Kamloops, Kelowna, Kitchener, Kamloops, London, Mississauga,
Moncton, Nanaimo, Ottawa, Red Deer, Regina, Saskatoon, Trois-Rivia, Utopia,
Vancouver, Victoria, Winnipeg,
Chile: Santiago
Ecuador: Guayaquil, Quito,
France: Aubagne, Bordeaux, Cesson-Sevigne, Courbevoie, Marcq-en-Baroeul,
Mitry-mory, Montpellier, Nice, Strasbourg, Toulouse, Trappes, Valenton,
Venissieux,
Germany: Aurich, Berlin, Bremen, Bremerhaven, Cloppenburg, Coventy, Dusseldorf, Dortmund, Emden, Frankfurt, Georgsmarienhuette, Haar, Hamburg, Hannover, Haselunne, Koln, Leer, Lehrte, Mainz, Meppen, Oldenburg, Osnabruck, Osterholz-Schlarmbeck, Papenburg, Rotenburg, Zeven
Great Britain: Basingstoke, Belfast, Birmingham, Bletchley, Brentford, Bristol,
Cardiff, Chester-Le-Street, Corsham, East Sussex, Edinburgh, Farnborough,
Glasgow, Gloucester, Guildford, Hampshire, Havant, Hayes, Hull, Kent, Keynes,
Leeds, Leicester, Liverpool, London, Manchester, Middlesborough, Middlesex,
Milton Keynes, Newbury, Newcastle, Nottingham, Reading, Sheffield, Slough
Berkshire, South Rettendon, Stoke, Surrey, York
Isle of Man: Douglas,
India: Abilene, Ahmedabad, Ambala, Asansol, Bangalore, Baroda, Bengaluru,
Bhopal, Bhubaneswar, Chandigarh, Chennai, Coimbtore, Delhi, Dombivali, Ernakulam, Guwahati, Haryana, Hosur, Hyderabad, Jaipur, Jammu, Kanpur, Kirlampudi, Kolkata, Kozhikode, Lucknow, Ludhiana, Mangalore, Meerut, Mohali, Moradabad, Mumbai, Nagpur, Navi Mumbai, Nellore, New Delhi, Palghar, Patna, Pune, Raipur, Raiahmundry, Rajkot, Ranchi, Shilong, Shimla, Sion, Srinagar, Surat, Thiruvananthapuram, Thrissur, Vijayawada, Warangal
Italy: Ancona, Bari, Bergamo, Bologna, Cagliari, Casoria, Firenze, Florence,
Genova, Grugliasco, Milan, Naples, Padua, Palermo, Pescara, Rome, Salerno, Sesto San Giovanni, Settimo, Turin, Venezia, Venice, Verona
Japan: Chiyoda-ku, Chuo-ku, Fukuoka, Kasuyagun, Kita-ku, Koto-ku, Matsuyama,
Moriguchi-shi, Nagoya City, Nerima-ku, Nishinomiya-shi, Nisshin City, Osaka-shi,
Takamatsu, Takarazuka-shi
Mexico: Apodaca, Colonia Nuevo Repueblo, Cuautitlan Izcalli, Guadalajara,
Jiutepec, Juarex, Merida, Monterrey, Puebla, Tijuana, Tlalnepantla, Tlaquepaque,
Torreon, Zapopan
Monaco: Monaco
New Zealand: Auckland, Christchurch, Hamilton, Wellington
Panama: Panama
Puerto Rico: Luquillo, Ponce, Vea Baja,
Spain: Barcelona, Gran Canaria, Madrid, Sevilla,
Thailand: Bangkok, Khlong Nueng, Laksi, Nonthaburi, Pathumthaini, PomPrap
Sattru Phai, Tambon Klong Tamru,
United States: Alamogordo, Amarillo, Anchorage, Ardmore, Arvada, Ashburn,
Ashwaubenon, Atlanta, Austin, Bay City, Beltsville, Bend, Billerica, Biloxi,
Birmingham, Bismarck, Boerne, Boise, Bossier, Broken Arrow, Bryan, Burlington,
Butler, Canyon Lake, Charleston, Charlotte, Chicago, Cincinnati, Cleveland,
Colombia, Contoocook, Corpus Christi, Dallas, Denver, Detroit, Durham, Elgin,
Englewood, Eureka, Evansville, Fargo, Fitzgerald, Flagstaff, Georgetown, GrandePrairie, Greenville, Grinnell, Hawthorne, Henrico, Hicksville, Hobbs, Honolulu, Hudson, Irvine, Jacksonville, Jonesboro, Joplin, Kansas City, Katy, Kingwood, Lake Charles, Lake Havasu, Las Vegas, Lawrence, Lexington, Lincoln, Lisle, Little Rock, Live Oak, Louisville, Lubbock, Madison, Manchester, Memphis, Miami, Minneapolis, Monroe, Mooresville, Mt. Juliet, Nashville, Natchitoches, New Orleans, Norcross, Norfolk, North Lima, Norton, Odessa, Oklahoma City, Omaha, Orlando, Owatonna, Oxford, Palmerton, Parkersburg, Parsippany, Phoenix, Pittsburgh, Pontotoc, Prescott, Richmond, Road Norfolk, Rocky Mt., Russellville, Sacramento, Salt Lake City, San Angelo, San Antonio, San Diego, San Francisco, San Marcos, Santa Clara, Seattle, Silverton, Sioux Falls, South Bed, Southfield, St. George, St. Louis, Starkville, Tallahassee, Toledo, Truckee, Tukwila, Vincennes, Waco, Washington, West Sacramento, White Plains, Wilkes Barre, Zelienople, Zionsville
Use cases
Reusable configurations that let you manage
CloudFront distribution for numerous web applications without the need to create new configurations for each distribution.
Tailored security and origin settings including tenant level overrides to help you meet your customer’s needs.
Enhanced integrations with AWS services to
deliver automated certificate management, unified security controls, and hassle-free configuration control for your customers at scale.
Global Edge Network
Reliable, low latency and high throughput network connectivity
Network Connectivity and Backbone
Amazon CloudFront peers with thousands of Tier 1/2/3 telecom carriers globally, is well connected with all major access networks for optimal performance, and has hundreds of terabits of deployed capacity. CloudFront edge locations are seamlessly connected to AWS Regions through the fully redundant AWS network backbone. This backbone is comprised of multiple 400GbE parallel fibers across the globe and interfaces with tens of thousands of networks for improved origin fetches and dynamic content acceleration.
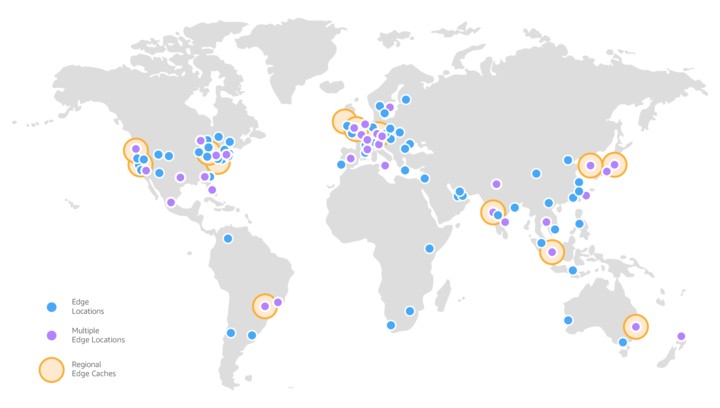
Amazon CloudFront has three types of infrastructure to securely deliver content with high performance to end users:
CloudFront Regional Edge Caches (RECs) are situated within AWS Regions, between your applications’ web server and CloudFront Points of Presence (POPs) and embedded Points of Presence. CloudFront has 15 RECs globally.
CloudFront Points of Presence are situated within the AWS network and peer with internet service provider (ISP) networks. CloudFront has 750+ POPs in 100+ cities across 50+ countries.
CloudFront embedded Points of Presence are situated within internet service provider (ISP) networks, closest to end viewers. In addition to CloudFront POPs, there are 1,140+ embedded POPs across 300+ cities in North America, Europe, and Asia.
Security
Protection against network and application layer attacks
Amazon CloudFront, AWS Shield, AWS Web Application Firewall (WAF), and Amazon Route 53 work seamlessly together to create a flexible, layered security perimeter against multiple types of attacks including network and application layer DDoS attacks. All of these services co-reside at the AWS edge and provide a scalable, reliable, and high-performance security perimeter for applications and content. With CloudFront as the “front door” to an application and infrastructure, the primary attack surface is moved away from critical content, data, code and infrastructure.
With Amazon CloudFront, content, APIs or applications can be delivered over HTTPS using the latest version Transport Layer Security (TLSv1.3) to encrypt and secure communication between viewer clients and CloudFront. AWS Certificate Manager (ACM) can be used to easily create a custom SSL certificate and deploy to an CloudFront distribution for free. ACM automatically handles certificate renewal, eliminating the overhead and costs of a manual renewal process. Additionally, CloudFront provides a number of TLS optimizations and advanced capabilities such as full/half bridge HTTPS connections, OCSP stapling, Session Tickets, Perfect Forward Secrecy, TLS Protocol Enforcements and Field-Level Encryption.
With Amazon CloudFront, access is restricted to content through a number of capabilities. With Signed URLs and Signed Cookies, Token Authentication is supported to restrict access to only authenticated viewers. Through geo-restriction capability, users can be prevented in specific geographic locations from accessing content that is distributed through CloudFront. With Origin Access Identity (OAI) feature, access can be restricted to an Amazon S3 bucket, making it only accessible from CloudFront.
CloudFront infrastructure (excluding CloudFront embedded POPs) and processes are all compliant with PCI-DSS Level 1, HIPAA, and ISO 9001, ISO/IEC 27001:2013, 27017:2015, 27018:2019, SOC (1, 2 and 3), FedRAMP Moderate and more to ensure secure delivery for sensitive data.
Availability
Origin Shield
Web applications often need to contend with spikes in traffic during peak periods of activity. By using Amazon CloudFront, the volume of application origin requests is automatically reduced. Content is stored in CloudFront’s edge and regional caches and only fetched from origins when needed. The load on application origins can be further reduced by using Origin Shield to enable a centralized caching layer. Origin Shield optimizes cache hit ratios and collapses requests across regions leading to as few as one origin request per object. This reduced traffic to your origins helps increase the availability of your applications.
Enabling redundancy for origins
CloudFront supports multiple origins for backend architecture redundancy. CloudFront’s native origin failover capability automatically serves content from a backup origin when the primary origin is unavailable. The origins set up with origin failover can be any combination of AWS origins like EC2 instances, Amazon S3 buckets, or Media Services, or non-AWS origins like an on-premises HTTP server. Additionally, you can implement advanced origin failover capabilities with CloudFront and Lambda@Edge.
Edge computing
CloudFront Functions
Amazon CloudFront offers programmable and secure edge CDN computing capabilities through CloudFront Functions and AWS Lambda@Edge. CloudFront Functions is ideal for high scale and latency sensitive operations like HTTP header manipulations, URL rewrites/redirects, and cache-key normalizations. These types of short running, lightweight operations support traffic that is often unpredictable and spiky. For example, you can use CloudFront Functions to redirect requests to language specific versions of your site based on the Accept-Language header of the incoming request. Because these functions execute at all of CloudFront’s edge locations, they can scale instantly to millions of requests per second with minimal latency overhead, typically under one millisecond. You can also utilize CloudFront KeyValueStore, a global, low-latency, key value data store to store and retrieve lookup data from within CloudFront Functions. CloudFront KeyValueStore makes CloudFront Functions more customizable by allowing independent data updates.
Lambda@Edge
AWS Lambda@Edge is a general-purpose serverless compute feature that supports a wide range of computing needs and customizations. Lambda@Edge is best suited for computationally intensive operations. This could be computations that take longer to complete (several milliseconds to seconds), take dependencies on external 3rd party libraries, require integrations with other AWS services (e.g., S3, DynamoDB), or need networks calls for data processing. Some of the popular advanced use cases include HLS streaming manifest manipulation, integrations with 3rd party authorization and bot detection services, server-side rendering (SSR) of single-page apps (SPA) at the edge and more.
Real-time metrics and logging
Real-time metrics
Amazon CloudFront is integrated with Amazon CloudWatch, and automatically publishes six operational metrics per distribution, which are displayed in a set of graphs in the CloudFront console. Additional, granular metrics are available with simple click on the console or via API.
Standard and real-time logging
CloudFront provides two ways to log the requests delivered from your distributions: Standard logs and Real-time logs. Standard logs are delivered to the Amazon S3 bucket of your choice (log records are delivered within minutes of a viewer request). When enabled, CloudFront will automatically publish detailed log information in a W3C extended format into an Amazon S3 bucket that you specify. CloudFront real-time logs are delivered to the data stream of your choice in Amazon Kinesis Data Streams (log records are delivered within seconds of a viewer request). You can choose the sampling rate for your real-time logs—that is, the percentage of requests for which you want to receive real-time log records.
DevOps friendly
CloudFront offers fast change propagation and invalidations, within a matter of minutes. Typically, changes are propagated to the edge in a matter of a few minutes, and invalidation times are under two minutes
Amazon CloudFront provides developers with a full-featured API to create, configure and maintain CloudFront distributions. In addition, developers have access to a number of tools such as AWS CloudFormation, CodeDeploy, CodeCommit and AWS SDKs to configure and deploy their workloads with Amazon CloudFront.
Your CloudFront distribution can be configured with multiple behaviors which govern how CloudFront will process your request and what features will be applied. Customize CloudFront behaviors, such as: how CloudFront caches, how CloudFront communicates with your origin, what headers and metadata are forwarded to your origin, create content variants with flexible cache-key manipulation, select compression modes, what headers are added to your HTTP responses, and more. With built-in device detection, CloudFront can detect the device type (Desktop, Tablet, Smart TV, or Mobile device) and pass that information in the form of new HTTP Headers to your application to easily adapt content variants or other responses. Amazon CloudFront can also detect the country-level location of the requesting user for further customization of the response.
Continuous deployment
Continuous deployment with CloudFront gives you a high level of deployment safety. You can now deploy two separate but identical environments—blue and green, and enable simple integration into your continuous integration and delivery (CI/CD) pipelines with the ability to roll out releases gradually without any domain name system (DNS) changes. It ensures that your viewer gets a consistent experience through session stickiness by binding the viewer session to the same environment. Additionally, you can compare the performance of your changes by monitoring standard and real-time logs and quickly revert to the previous configuration when a change negatively impacts a service. Typical use cases for this feature include checking for backward compatibility, post-deployment verification, and validating new features with a smaller group of viewers.
Cost effective
CloudFront offers personalized pricing options including pay-as-you-go, the CloudFront Security Savings Bundle, and custom pricing. Pay-as-you-go pricing is simple with no upfront fees. If you are looking for a discount, the CloudFront Security Savings Bundle that helps you save up to 30% on your CloudFront bill in exchange for a monthly spend commitment for a 1-year term. The savings bundle also includes free AWS WAF usage up to 10% of the monthly committed spend. For customers who are willing to make certain minimum traffic commitments (typically 10 TB/month or higher), we also offer additional discounts with private committed pricing.
If AWS origins such as Amazon S3, Amazon EC2 or Elastic Load Balancing are used, there is no charge incurred for data transferred from origins to CloudFront Edge locations (this type of data transfer is known as origin fetch). To learn more about all Amazon CloudFront features, and how to configure them, please refer to the Amazon CloudFront Developer Guide.
Not all origins are alike and some may involve processes such as just-in-time packaging that are more computationally expensive per GB than fetching content out of storage. CloudFront provides regional edge caches at no additional cost to decrease the operational burden on origins and lower operating costs. Further reduction in origin-related costs are available using Origin Shield to minimize the number of origin fetches. Origin Shield provides centralized caching to optimize cache-hit ratios and collapse requests across regions resulting in as few as one origin request per object.