Networking & Content Delivery
Tag: Amazon CloudFront
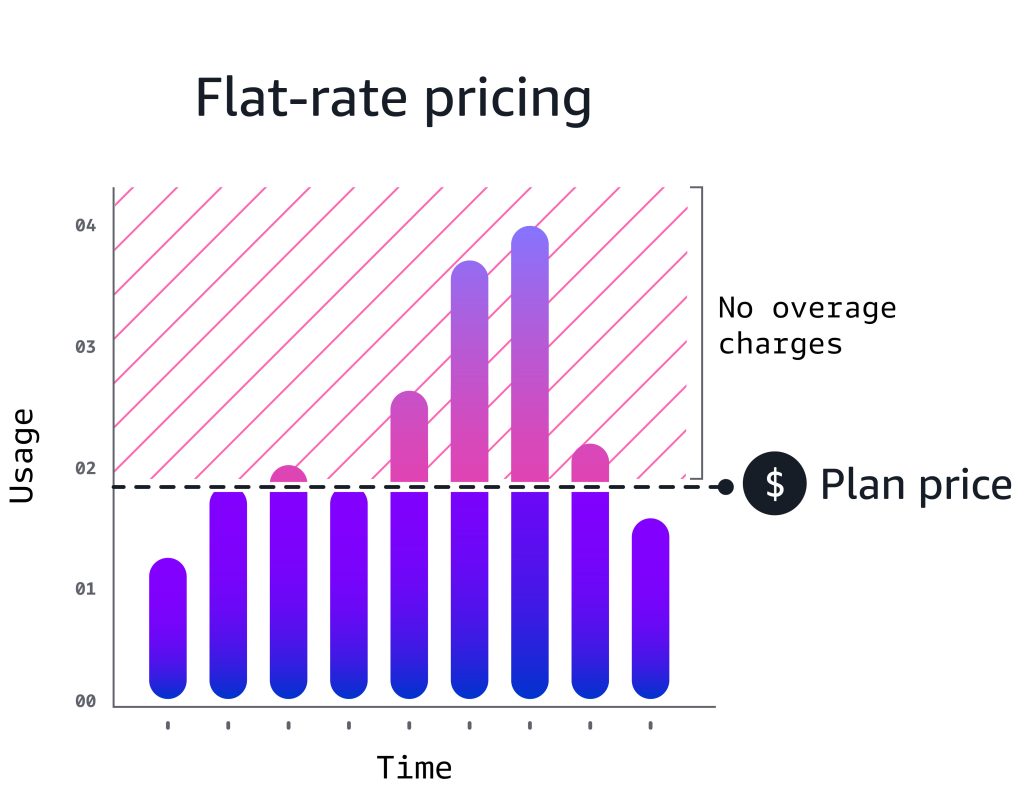
Amazon CloudFront Premium flat-rate pricing plan now supports higher, configurable usage allowances
Running an internet-facing application means estimating and managing costs across many services and features: content delivery, web application firewall (WAF), DNS, logging, and DDoS protection. Each has its own pricing model, its own metering, its own line item on the bill. Traffic from successful launches, organic growth, and AI bots can spike without warning, increasing […]
Tag-based invalidation in Amazon CloudFront
Update (May 2026): Amazon CloudFront now natively supports tag-based cache invalidation — no additional infrastructure required. You can tag cached objects via origin response headers or S3 metadata and invalidate them by tag directly through the CloudFront API. For details, see the CloudFront Developer Guide and the launch blog post. If you are starting fresh, […]
Manage caches with precision using Amazon CloudFront Invalidation by Cache Tag
Today, Amazon CloudFront is launching Invalidation by Cache Tag, a new capability that transforms how developers manage cached content. With this feature, you can invalidate groups of related cached objects using a single invalidation request, regardless of URL structure—making cache management more precise, efficient, and developer-friendly. In this post, we discuss the benefits of this […]
Amazon CloudFront flat-rate pricing plans: new features and expanded capabilities
In November 2025, we launched flat-rate pricing plans for Amazon CloudFront. Since launch, customers have shared feedback and we’ve been adding new capabilities. This post covers what’s new: support for Lambda@Edge, CAPTCHA, mutual TLS (mTLS), and an AI activity dashboard for visibility into AI bot and agent traffic. We’ve also clarified how plans handle traffic […]
Migrate Amazon CloudFront public origins to private VPC origins
Introduction This post demonstrates how to migrate your Amazon CloudFront public origins to Amazon Virtual Private Cloud (Amazon VPC) origins using different strategies. You can also use VPC origins with cross-accounts to support security-first architectures. When designing network architecture for CloudFront workloads, organizations must choose between centralized or distributed models. In a centralized architecture, a […]
Adding HTTP security headers using Amazon CloudFront
This post is written for web developers, DevOps engineers, and security professionals who want to strengthen their application security posture without complex implementations. HTTP security headers represent a critical yet often overlooked layer of defense that can protect your users from common web vulnerabilities such as cross-site scripting (XSS), clickjacking, and man-in-the-middle attacks. They are […]
Implementing dynamic origin modification in Amazon CloudFront – Part 2
In part one of this post, we introduced two methods, Amazon CloudFront Functions and Lambda@Edge, for executing custom code at CloudFront edge Locations to modify request origins dynamically. This second post provides step-by-step setup instructions and code samples for implementing the two approaches for a subscription-based routing use case: CloudFront Functions with query string parameters […]
Understanding dynamic origin modification in Amazon CloudFront – Part 1
In the modern digital landscape, our lives are inescapably dominated by screens and browsers. From global product launches to flash sales and virtual concerts, events that once drew crowds to physical venues now drive millions of users to digital platforms simultaneously. The rapid rise of digital-first experiences has made the need to dynamically adjust content […]
Amazon CloudFront now supports mTLS authentication to origins
Starting today, Amazon CloudFront extends its mutual TLS (mTLS) capabilities to customer origins, which enables true end-to-end authentication throughout the entire connection path—from the viewers to the customer origins. CloudFront has supported viewer mTLS between viewers and CloudFront, so that customers can strongly authenticate clients before traffic ever enters their perimeter. With this launch, that […]
Implementing ingress geo-restriction with AWS to reduce attack surface
Geo-restriction is a critical security control for blocking traffic from high-risk regions. Learn how to implement geographic filtering using Amazon CloudFront, Route 53, AWS WAF, and AWS Network Firewall—and discover when to use each service for your specific architecture needs.