Networking & Content Delivery
Category: Security, Identity, & Compliance
Implementing fine-grained Amazon Route 53 access using IAM condition keys (Part 2)
In Part 1 of this series, we demonstrated a scalable solution of using Amazon Web Services Identity and Access Management (AWS IAM) conditional keys and AWS principal tags for fine-grained access control of shared Amazon Route 53 hosted zones, public or private, in the same AWS account. As user environments grow, AWS administrators and network […]
Deploy VPC Block Public Access across AWS Organizations
Managing security configurations across hundreds or thousands of Amazon Web Services (AWS) accounts present significant challenges for enterprise organizations. Without centralized control, you face manual configuration across accounts, inconsistent security posture, and ongoing maintenance overhead when new accounts are created. When Amazon Virtual Private Cloud (Amazon VPC) introduced VPC Block Public Access (BPA) in November […]
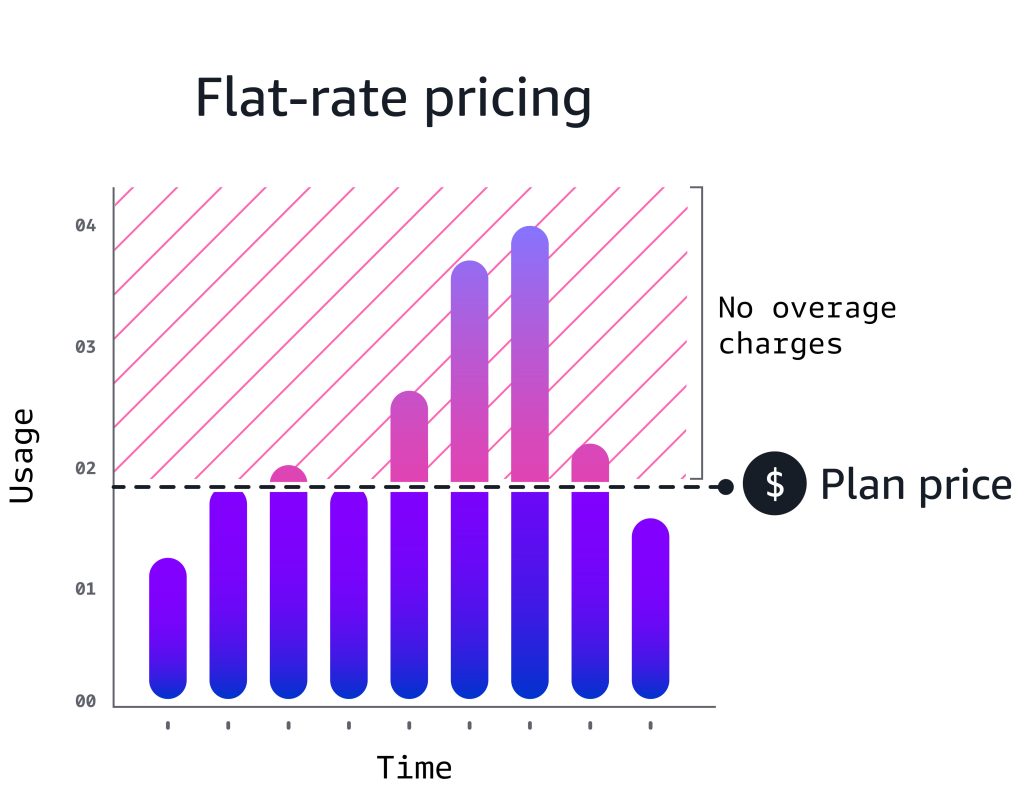
Amazon CloudFront flat-rate pricing plans: new features and expanded capabilities
In November 2025, we launched flat-rate pricing plans for Amazon CloudFront. Since launch, customers have shared feedback and we’ve been adding new capabilities. This post covers what’s new: support for Lambda@Edge, CAPTCHA, mutual TLS (mTLS), and an AI activity dashboard for visibility into AI bot and agent traffic. We’ve also clarified how plans handle traffic […]
How Betsson Services Limited elevated AWS hybrid connectivity to new heights with AWS Cloud WAN
Betsson Services Limited (or Betsson Group) is a leading global sports betting and gaming operator, delivering entertainment to millions of players through more than 20 award-winning brands, including its flagship brand, Betsson. With a proprietary technology stack and a diverse product offering, Betsson serves customers both directly (B2C) and indirectly (B2B). At Betsson, our vision […]
Using cross-account CloudFront VPC origins for multi-account private API Gateway architecture
In November 2025, Amazon CloudFront introduced cross-account support for Virtual Private Cloud (VPC) origins, which allows you to keep Amazon VPC origins and CloudFront distributions in separate Amazon Web Services (AWS) accounts. In turn, organizations with multi-account strategies can use VPC origins while maintaining their desired account structure. This enables a new architectural pattern for […]
Implementing consistent DNS Query Logging with Amazon Route 53 Profiles
Managing DNS query logging across multiple Amazon Virtual Private Clouds (VPCs) has long been a significant challenge for enterprise teams. The traditional approach required manual configuration of DNS query logging for each VPC individually, creating a cascade of operational problems. This fragmented process led to inconsistent implementation across different environments, compliance gaps due to missed […]
Implementing ingress geo-restriction with AWS to reduce attack surface
Geo-restriction is a critical security control for blocking traffic from high-risk regions. Learn how to implement geographic filtering using Amazon CloudFront, Route 53, AWS WAF, and AWS Network Firewall—and discover when to use each service for your specific architecture needs.
Distributing Amazon VPC IP Address Manager costs to member accounts in AWS Organizations
In this post, we demonstrate how to distribute Amazon VPC IP Address Manager (IPAM) costs from the IPAM owner account to the member accounts in AWS Organizations and implement chargeback. We walk through analyzing IPAM usage in AWS Cost Explorer from both member and management accounts. Furthermore, we cover key considerations and best practices for communication and […]
Securing Egress Architectures with Network Firewall Proxy
Note: Dec 4, 2025 – expanded with additional section on application networking integrations. Customers who control access out of their AWS environments using self-managed proxies often find it challenging to deploy, scale, and patch their EC2 or container-based proxy fleets. With the recent launch of AWS Network Firewall proxy preview, AWS is taking over the […]
Introducing flat-rate pricing plans with no overages
Today, Amazon Web Services (AWS) is launching flat-rate pricing plans with no overages for website delivery and security. The pricing plans, available with Amazon CloudFront, combine global content delivery (CDN) with multiple AWS services and features into a monthly price with no overage charges, regardless of whether your website or application goes viral or faces […]