AWS Security Blog
Category: Security, Identity, & Compliance
New AWS whitepaper: Security Overview of Amazon EKS Auto Mode
Amazon Web Services (AWS) has released a new whitepaper: Security Overview of Amazon EKS Auto Mode, providing customers with an in-depth look at the architecture, built-in security features, and capabilities of Amazon Elastic Kubernetes Service (Amazon EKS) Auto Mode. The whitepaper covers the core security principles of Amazon EKS Auto Mode, highlighting its unique approach […]
Defending against supply chain attacks like Chalk/Debug and the Shai-Hulud worm
Building on top of open source packages can help accelerate development. By using common libraries and modules from npm, PyPI, Maven Central, NuGet, and others, teams can focus on writing code that is unique to their situation. These open source package registries host millions of packages that are integrated into thousands of programs daily. Unfortunately, […]
Defending LLM applications against Unicode character smuggling
When interacting with AI applications, even seemingly innocent elements—such as Unicode characters—can have significant implications for security and data integrity. At Amazon Web Services (AWS), we continuously evaluate and address emerging threats across aspects of AI systems. In this blog post, we explore Unicode tag blocks, a specific range of characters spanning from U+E0000 to […]
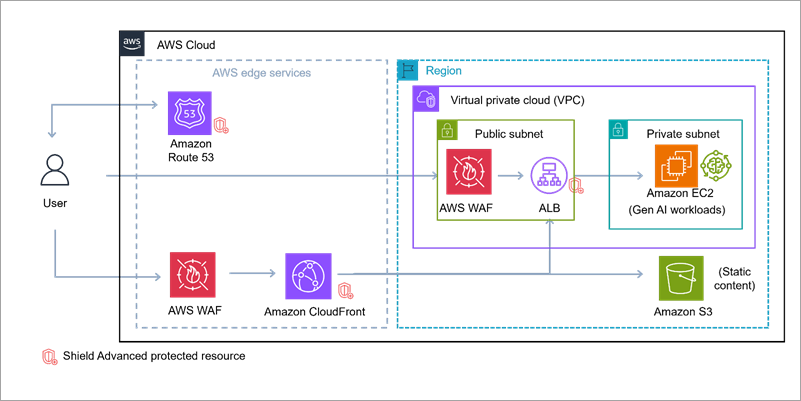
Build secure network architectures for generative AI applications using AWS services
As generative AI becomes foundational across industries—powering everything from conversational agents to real-time media synthesis—it simultaneously creates new opportunities for bad actors to exploit. The complex architectures behind generative AI applications expose a large surface area including public-facing APIs, inference services, custom web applications, and integrations with cloud infrastructure. These systems are not immune to […]
Enabling AI adoption at scale through enterprise risk management framework – Part 2
In Part 1 of this series, we explored the fundamental risks and governance considerations. In this part, we examine practical strategies for adapting your enterprise risk management framework (ERMF) to harness generative AI’s power while maintaining robust controls. This part covers: Adapting your ERMF for the cloud Adapting your ERMF for generative AI Sustainable Risk […]
Enabling AI adoption at scale through enterprise risk management framework – Part 1
According to BCG research, 84% of executives view responsible AI as a top management responsibility, yet only 25% of them have programs that fully address it. Responsible AI can be achieved through effective governance, and with the rapid adoption of generative AI, this governance has become a business imperative, not just an IT concern. By […]
Optimize security operations with AWS Security Incident Response
Security threats demand swift action, which is why AWS Security Incident Response delivers AWS-native protection that can immediately strengthen your security posture. This comprehensive solution combines automated triage and evaluation logic with your security perimeter metadata to identify critical issues, seamlessly bringing in human expertise when needed. When Security Incident Response is integrated with Amazon […]
Minimize risk through defense in depth: Building a comprehensive AWS control framework
Security and governance teams across all environments face a common challenge: translating abstract security and governance requirements into a concrete, integrated control framework. AWS services provide capabilities that organizations can use to implement controls across multiple layers of their architecture—from infrastructure provisioning to runtime monitoring. Many organizations deploy multi-account environments with AWS Control Tower, or […]
How to accelerate security finding reviews using automated business context validation in AWS Security Hub CSPM
October 1, 2025: This post was updated to reflect the new name of Security Hub, which is AWS Security Hub CSPM (Cloud Security Posture Management). Security teams must efficiently validate and document exceptions to AWS Security Hub (Cloud Security Posture Management, previously known as Security Hub) findings, while maintaining proper governance. Enterprise security teams need […]
Unlock new possibilities: AWS Organizations service control policy now supports full IAM language
Amazon Web Service (AWS) recently announced that AWS Organizations now offers full AWS Identity and Access Management (IAM) policy language support for service control policies (SCPs). With this feature, you can use conditions, individual resource Amazon Resource Names (ARNs), and the NotAction element with Allow statements. Additionally, you can now use wildcards at the beginning or middle of […]