AWS Security Blog
Tag: Amazon S3
IAM Access Analyzer makes it easier to implement least privilege permissions by generating IAM policies based on access activity
In 2019, AWS Identity and Access Management (IAM) Access Analyzer was launched to help you remove unintended public and cross account access by analyzing your existing permissions. In March 2021, IAM Access Analyzer added policy validation to help you set secure and functional permissions during policy authoring. Now, IAM Access Analyzer takes that a step […]
How to scale your authorization needs by using attribute-based access control with S3
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. May 26, 2021: In the section “Secure your tags using an AWS Organizations service control […]
Validate access to your S3 buckets before deploying permissions changes with IAM Access Analyzer
AWS Identity and Access Management (IAM) Access Analyzer helps you monitor and reduce access by using automated reasoning to generate comprehensive findings for resource access. Now, you can preview and validate public and cross-account access before deploying permission changes. For example, you can validate whether your S3 bucket would allow public access before deploying your […]
How to visualize multi-account Amazon Inspector findings with Amazon Elasticsearch Service
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. Amazon Inspector helps to improve the security and compliance of your applications that are deployed on Amazon Web Services (AWS). It automatically assesses Amazon Elastic Compute Cloud (Amazon EC2) instances and applications on those instances. From that assessment, it generates […]
Use Macie to discover sensitive data as part of automated data pipelines
Data is a crucial part of every business and is used for strategic decision making at all levels of an organization. To extract value from their data more quickly, Amazon Web Services (AWS) customers are building automated data pipelines—from data ingestion to transformation and analytics. As part of this process, my customers often ask how […]
Discover sensitive data by using custom data identifiers with Amazon Macie
As you put more and more data in the cloud, you need to rely on security automation to keep it secure at scale. AWS recently launched Amazon Macie, a fully managed service that uses machine learning and pattern matching to help you detect, classify, and better protect your sensitive data stored in the AWS Cloud. […]
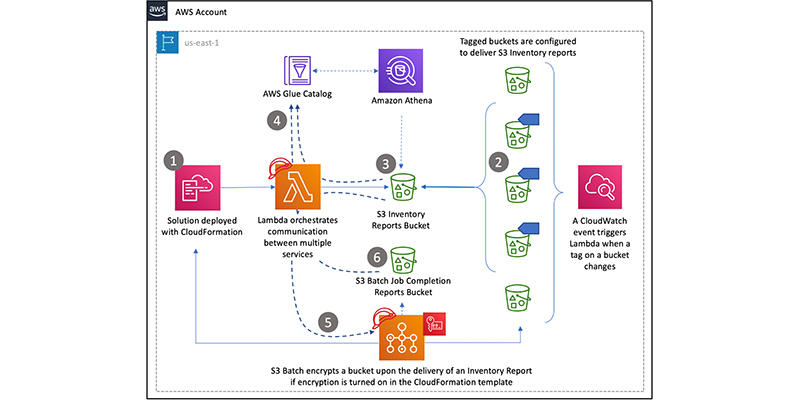
How to retroactively encrypt existing objects in Amazon S3 using S3 Inventory, Amazon Athena, and S3 Batch Operations
February 5, 2026: Amazon S3 now supports the UpdateObjectEncryption API so you can atomically update the server-side encryption type of existing encrypted objects from server-side encryption with S3 managed encryption (SSE-S3) to server-side encryption with AWS Key Management Service (AWS KMS) encryption keys (SSE-KMS). Read the documentation. November 1, 2021: AWS KMS is replacing the […]
Tighten S3 permissions for your IAM users and roles using access history of S3 actions
September 28, 2023: IAM is incrementally adding support for actions from more services. For a list of services that report action last accessed information, see IAM action last accessed information services and actions. Customers tell us that when their teams and projects are just getting started, administrators may grant broad access to inspire innovation and […]
IAM Access Analyzer flags unintended access to S3 buckets shared through access points
Customers use Amazon Simple Storage Service (S3) buckets to store critical data and manage access to data at scale. With Amazon S3 Access Points, customers can easily manage shared data sets by creating separate access points for individual applications. Access points are unique hostnames attached to a bucket and customers can set distinct permissions using […]
How to use KMS and IAM to enable independent security controls for encrypted data in S3
August 31, 2021:AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. Typically, when you protect data in Amazon Simple Storage Service (Amazon S3), you use a combination […]