AWS Security Blog
Category: Amazon Simple Storage Service (S3)
A framework for securely collecting forensic artifacts into S3 buckets
When customers experience a security incident, they need to acquire forensic artifacts to identify root cause, extract indicators of compromise (IoCs), and validate remediation efforts. NIST 800-86, Guide to Integrating Forensic Techniques into Incident Response, defines digital forensics as a process comprised of four basic phases: collection, examination, analysis, and reporting. This blog post focuses […]
How to update CRLs without public access using AWS Private CA
Certificates and the hierarchy of trust they create are the backbone of a secure infrastructure. AWS Private Certificate Authority is a highly available certificate authority (CA) that you can use to create private CA hierarchies, secure your applications and devices with private certificates, and manage certificate lifecycles. A certificate revocation list (CRL) is a file […]
Secure file sharing solutions in AWS: A security and cost analysis guide: Part 2
As introduced in Part 1 of this series, implementing secure file sharing solutions in AWS requires a comprehensive understanding of your organization’s needs and constraints. Before selecting a specific solution, organizations must evaluate five fundamental areas: access patterns and scale, technical requirements, security and compliance, operational requirements, and business constraints. These areas cover everything from […]
Secure file sharing solutions in AWS: A security and cost analysis guide, Part 1
Securely share sensitive data with time-limited, nonce-enhanced presigned URLs that prevent replay attacks, minimizing exposure risks through granular access controls and rigorous monitoring.
How to use AWS Transfer Family and GuardDuty for malware protection
Organizations often need to securely share files with external parties over the internet. Allowing public access to a file transfer server exposes the organization to potential threats, such as malware-infected files uploaded by threat actors or inadvertently by genuine users. To mitigate this risk, companies can take steps to help make sure that files received […]
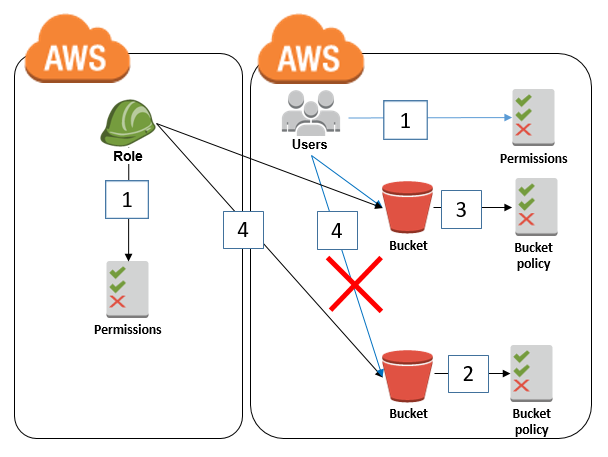
How to restrict Amazon S3 bucket access to a specific IAM role
February 14, 2025: This post was updated with the recommendation to restrict S3 bucket access to an IAM role by using the aws:PrincipalArn condition key instead of the aws:userid condition key. April 2, 2021: In the section “Granting cross-account bucket access to a specific IAM role,” we updated the second policy to fix an error. […]
Writing IAM Policies: Grant Access to User-Specific Folders in an Amazon S3 Bucket
Mar 25, 2024: We have fixed the JSON code examples which caused errors by replacing the curly quotes with straight quotes. November 14, 2023: We’ve updated this post to use IAM Identity Center and follow updated IAM best practices. In this post, we discuss the concept of folders in Amazon Simple Storage Service (Amazon S3) […]
IAM Policies and Bucket Policies and ACLs! Oh, My! (Controlling Access to S3 Resources)
September 11, 2023: This post has been updated. Updated on July 6, 2023: This post has been updated to reflect the current guidance around the usage of S3 ACL and to include S3 Access Points and the Block Public Access for accounts and S3 buckets. Updated on April 27, 2023: Amazon S3 now automatically enables […]
Top 10 security best practices for securing data in Amazon S3
With more than 100 trillion objects in Amazon Simple Storage Service (Amazon S3) and an almost unimaginably broad set of use cases, securing data stored in Amazon S3 is important for every organization. So, we’ve curated the top 10 controls for securing your data in S3. By default, all S3 buckets are private and can […]
How to securely create and store your CRL for AWS Private CA
June 25, 2025: As of Sept 28, 2022, AWS has changed the name of ACM Private CA to AWS Private CA. This post has been updated to reflect this change. December 4, 2023:We’ve updated the new Amazon CloudFront security feature Origin Access Control in place of the Origin Access Identity. December 14, 2021:The code in […]