AWS Security Blog
Category: Amazon Simple Storage Service (S3)
Use IAM Access Analyzer to generate IAM policies based on access activity found in your organization trail
January 25, 2024: The path of the bucket was updated in this post. In April 2021, AWS Identity and Access Management (IAM) Access Analyzer added policy generation to help you create fine-grained policies based on AWS CloudTrail activity stored within your account. Now, we’re extending policy generation to enable you to generate policies based on […]
Strengthen the security of sensitive data stored in Amazon S3 by using additional AWS services
October 13, 2021: We’ve added a section on redacting and transforming personally identifiable information with Amazon S3 Object Lambda. In this post, we describe the AWS services that you can use to both detect and protect your data stored in Amazon Simple Storage Service (Amazon S3). When you analyze security in depth for your Amazon […]
Security is the top priority for Amazon S3
Amazon Simple Storage Service (Amazon S3) launched 15 years ago in March 2006, and became the first generally available service from Amazon Web Services (AWS). AWS marked the fifteenth anniversary with AWS Pi Week—a week of in-depth streams and live events. During AWS Pi Week, AWS leaders and experts reviewed the history of AWS and […]
How to scale your authorization needs by using attribute-based access control with S3
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. May 26, 2021: In the section “Secure your tags using an AWS Organizations service control […]
Validate access to your S3 buckets before deploying permissions changes with IAM Access Analyzer
AWS Identity and Access Management (IAM) Access Analyzer helps you monitor and reduce access by using automated reasoning to generate comprehensive findings for resource access. Now, you can preview and validate public and cross-account access before deploying permission changes. For example, you can validate whether your S3 bucket would allow public access before deploying your […]
Learn and use 13 AWS security tools to implement SEC recommended protection of stored customer data in the cloud
Most businesses collect, process, and store sensitive customer data that needs to be secured to earn customer trust and protect customers against abuses. Regulated businesses must prove they meet guidelines established by regulatory bodies. As an example, in the capital markets, broker-dealers and investment advisors must demonstrate they address the guidelines proposed by the Office […]
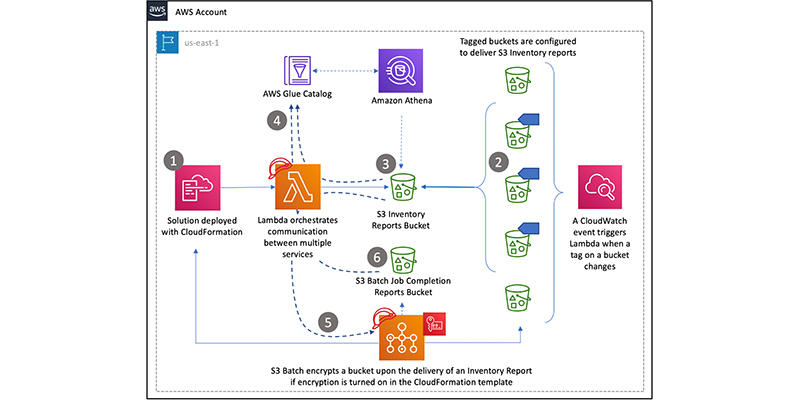
How to retroactively encrypt existing objects in Amazon S3 using S3 Inventory, Amazon Athena, and S3 Batch Operations
February 5, 2026: Amazon S3 now supports the UpdateObjectEncryption API so you can atomically update the server-side encryption type of existing encrypted objects from server-side encryption with S3 managed encryption (SSE-S3) to server-side encryption with AWS Key Management Service (AWS KMS) encryption keys (SSE-KMS). Read the documentation. November 1, 2021: AWS KMS is replacing the […]
Tighten S3 permissions for your IAM users and roles using access history of S3 actions
September 28, 2023: IAM is incrementally adding support for actions from more services. For a list of services that report action last accessed information, see IAM action last accessed information services and actions. Customers tell us that when their teams and projects are just getting started, administrators may grant broad access to inspire innovation and […]
IAM Access Analyzer flags unintended access to S3 buckets shared through access points
Customers use Amazon Simple Storage Service (S3) buckets to store critical data and manage access to data at scale. With Amazon S3 Access Points, customers can easily manage shared data sets by creating separate access points for individual applications. Access points are unique hostnames attached to a bucket and customers can set distinct permissions using […]
Continuously monitor unused IAM roles with AWS Config
February 19, 2024: You can now use IAM Access Analyzer to easily identify unused roles. Read this blog post to learn more. January 6, 2021: We updated this post to fix a bug related to allow listing noncompliant roles. January 6, 2020: We updated this post to reflect a valid STS session duration if configured […]