AWS Security Blog
Category: Top Posts
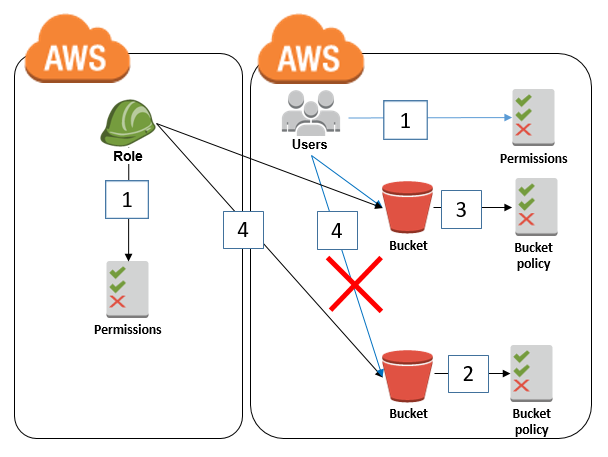
How to restrict Amazon S3 bucket access to a specific IAM role
February 14, 2025: This post was updated with the recommendation to restrict S3 bucket access to an IAM role by using the aws:PrincipalArn condition key instead of the aws:userid condition key. April 2, 2021: In the section “Granting cross-account bucket access to a specific IAM role,” we updated the second policy to fix an error. […]
How to enforce creation of roles in a specific path
May 20, 2024: This blog post has been updated with use case examples. The Optimize AWS administration with IAM paths blog post delves into the fundamental workings of the AWS Identity and Access Management (IAM) path feature. This post explores how you can use IAM paths to strike a balance between centralized IT and development […]
Writing IAM Policies: Grant Access to User-Specific Folders in an Amazon S3 Bucket
Mar 25, 2024: We have fixed the JSON code examples which caused errors by replacing the curly quotes with straight quotes. November 14, 2023: We’ve updated this post to use IAM Identity Center and follow updated IAM best practices. In this post, we discuss the concept of folders in Amazon Simple Storage Service (Amazon S3) […]
Top 10 security items to improve in your AWS account
August 10, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. If you’re looking to improve your cloud security, a good place to start is to follow the top 10 most important cloud security tips […]
How to define least-privileged permissions for actions called by AWS services
August 31, 2021: AWS KMS is replacing the term customer master key (CMK) with AWS KMS key and KMS key. The concept has not changed. To prevent breaking changes, AWS KMS is keeping some variations of this term. More info. February 21, 2020: We fixed a missing comma in a policy example. March 3, 2020: […]
Automated Response and Remediation with AWS Security Hub
June 2, 2021: The instructions in this blog post have been implemented in an AWS Solution, AWS Security Hub Automated Response and Remediation, that includes remediations for more than 20 security controls. To learn more about implementing the solution, see How to deploy the AWS Solution for Security Hub Automated Response and Remediation. AWS Security […]
Where’s My Secret Access Key?
March 12, 2019: You can now find and update your access keys from a single, central location in the AWS Management Console. Learn how in this post. In this blog post, I’ll discuss what you should do in case you’ve lost your secret access key or need a new one. This post assumes that you are […]