AWS Security Blog
Tag: Security Blog
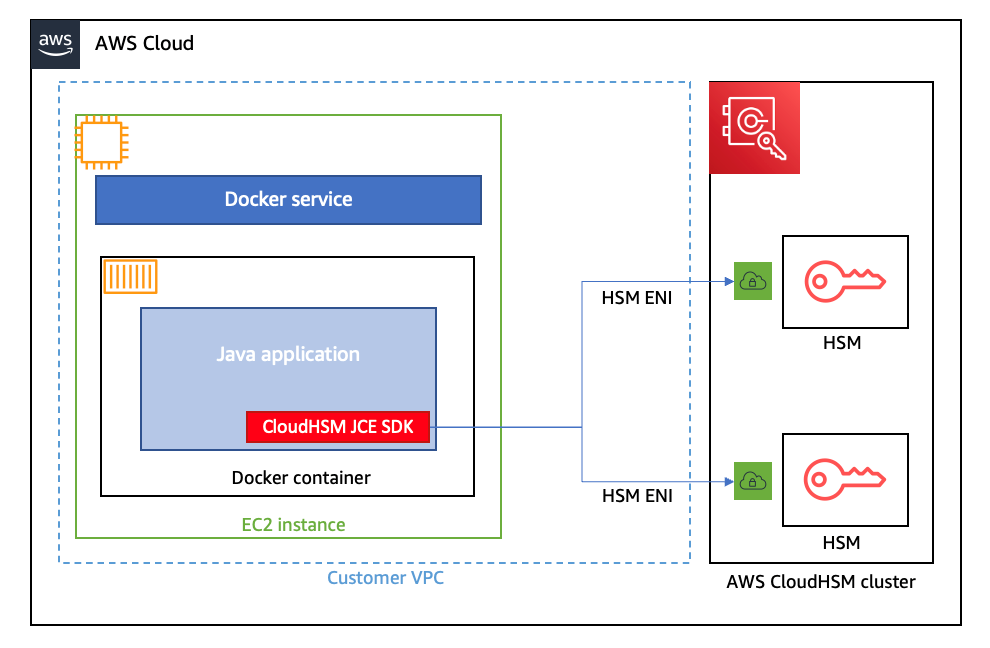
How to run AWS CloudHSM workloads in container environments
January 25, 2023: We updated this post to reflect the fact that CloudHSM SDK3 does not support serverless environments and we strongly recommend deploying SDK5. AWS CloudHSM provides hardware security modules (HSMs) in the AWS Cloud. With CloudHSM, you can generate and use your own encryption keys in the AWS Cloud, and manage your keys […]
United Arab Emirates IAR compliance assessment report is now available with 58 services in scope
Amazon Web Services (AWS) is pleased to announce the publication of our compliance assessment report on the Information Assurance Regulation (IAR) established by the Telecommunications and Digital Government Regulatory Authority (TDRA) of the United Arab Emirates. The report covers the AWS Middle East (UAE) Region, with 58 services in scope of the assessment. The IAR […]
How to improve security incident investigations using Amazon Detective finding groups
Uncovering the root cause of an Amazon GuardDuty finding can be a complex task, requiring security operations center (SOC) analysts to collect a variety of logs, correlate information across logs, and determine the full scope of affected resources. Sometimes you need to do this type of in-depth analysis because investigating individual security findings in insolation […]
Deploy a dashboard for AWS WAF with minimal effort
July 30, 2025: AWS rolled out the Traffic Overview dashboard, which delivers near-real-time CloudWatch metrics summaries for AWS WAF. This new dashboard includes comprehensive monitoring of various metrics such as total requests, blocked requests, bot categories, CAPTCHA solve rates, and top 10 matched rules. Additionally, in January 2025, AWS launched the Top Insights section, specifically […]
AWS CloudHSM is now PCI PIN certified
June 12, 2023: We updated this post to explain how CloudHSM meets the PCI PIN operational controls. Amazon Web Services (AWS) is pleased to announce that AWS CloudHSM is certified for Payment Card Industry Personal Identification Number (PCI PIN) version 3.1. With CloudHSM, you can manage and access your keys on FIPS 140-2 Level 3 […]
Use AWS WAF CAPTCHA to protect your application against common bot traffic
June 1, 2023: In April 2023, AWS WAF Captcha launched JavaScript API support which gives developers the ability to embed CAPTCHA within client-rendered web applications. The update to this blog introduces the new functionality and how to get started with it. In this blog post, you’ll learn how you can use a Completely Automated Public […]
Fall 2022 SOC reports now available in Spanish
Spanish version >> We continue to listen to our customers, regulators, and stakeholders to understand their needs regarding audit, assurance, certification, and attestation programs at Amazon Web Services (AWS). We are pleased to announce that Fall 2022 System and Organization Controls (SOC) 1, SOC 2, and SOC 3 reports are now available in Spanish. These […]
C5 Type 2 attestation report now available with 156 services in scope
We continue to expand the scope of our assurance programs at Amazon Web Services (AWS), and we are pleased to announce that AWS has successfully completed the 2022 Cloud Computing Compliance Controls Catalogue (C5) attestation cycle with 156 services in scope. This alignment with C5 requirements demonstrates our ongoing commitment to adhere to the heightened […]
Fall 2022 PCI DSS report available with six services added to compliance scope
We’re continuing to expand the scope of our assurance programs at Amazon Web Services (AWS) and are pleased to announce that six additional services have been added to the scope of our Payment Card Industry Data Security Standard (PCI DSS) certification. This provides our customers with more options to process and store their payment card […]
AWS achieves HDS certification in two additional Regions
We’re excited to announce that two additional AWS Regions—Asia Pacific (Jakarta) and Europe (Milan)—have been granted the Health Data Hosting (Hébergeur de Données de Santé, HDS) certification. This alignment with HDS requirements demonstrates our continued commitment to adhere to the heightened expectations for cloud service providers. AWS customers who handle personal health data can use […]