AWS News Blog
AWS CloudTrail Expands Again – More Locations and Services
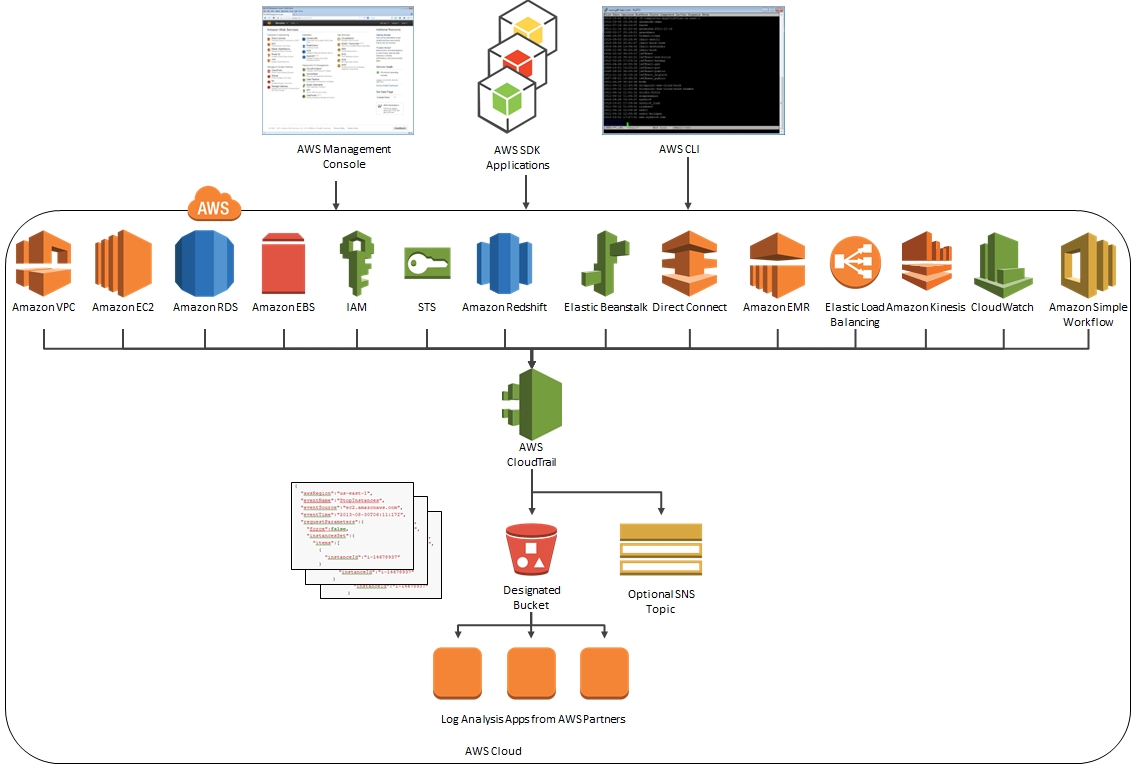
AWS CloudTrail records the API calls made in your AWS account and publishes the resulting log files to an Amazon S3 bucket in JSON format, with optional notification to an Amazon SNS topic each time a file is published.
Earlier this month we expanded CloudTrail’s service coverage with the addition of support for seven more services. Today we adding support for the Simple Workflow Service and are also making CloudTrail available in three additional AWS Regions:
- US West (Northern California)
- Asia Pacific (Sydney)
- EU (Ireland)
Note: If you have configured CloudTrail to store log files generated in multiple AWS Regions in the same S3 bucket, you will have to update the bucket’s policy statement so that it can accept logs from the new Regions. To do this, visit the Amazon S3 Bucket Policy section in the CloudTrail documentation. If CloudTrail creates the bucket on your behalf, it will also apply a policy that allows access from all of the Regions that exist at the time.
The Big Picture
Here’s the latest and greatest version of the diagram that I first presented when we launched CloudTrail:
CloudTrail Webinar With Splunk
 At 10:00 AM PT on May 20, AWS and Splunk will present the Stronger Security and Compliance on AWS with Log Collection and Analysis webinar. In the webinar you will learn how CloudTrail collects and stores your AWS log files so that software from Splunk can be used as a Big Data Security Information and Event Management (SIEM) system. You will hear how AWS log files are made available for many security use cases, including incident investigations, security and compliance reporting, and threat detection/alerting. FINRA (a joint Splunk/AWS customer) will explain how they leverage Splunk on AWS to support their cloud efforts.
At 10:00 AM PT on May 20, AWS and Splunk will present the Stronger Security and Compliance on AWS with Log Collection and Analysis webinar. In the webinar you will learn how CloudTrail collects and stores your AWS log files so that software from Splunk can be used as a Big Data Security Information and Event Management (SIEM) system. You will hear how AWS log files are made available for many security use cases, including incident investigations, security and compliance reporting, and threat detection/alerting. FINRA (a joint Splunk/AWS customer) will explain how they leverage Splunk on AWS to support their cloud efforts.
— Jeff;