AWS Cloud Operations Blog
Use existing Logging and Security Account with AWS Control Tower
AWS Control Tower provides the easiest way for you to set up and govern your AWS environment, or landing zone, following prescriptive AWS best practices managed on your behalf. AWS Control Tower orchestrates multiple AWS services (AWS Organizations, AWS CloudFormation StackSets, Amazon Simple Storage Service (Amazon S3), AWS Single Sign-On (AWS SSO), AWS Config, AWS CloudTrail) to build a landing zone in under 30 minutes. Moreover, it sets preventive and detective controls (guardrails) that make sure of best practices.
When you deploy AWS Control Tower, it creates two shared accounts out of the box: the audit account and the log archive account.
- The log archive account is for your team of users that need access to all of the logging information for all of your enrolled accounts within registered Organizational Units (OUs) in your landing zone.
- The audit account is for your team of users that need access to the audit information made available by AWS Control Tower. You can also use this account as the access point for third-party tools that will perform programmatic auditing of your environment to help you audit for compliance purposes.
In order for AWS Control Tower to create these accounts, customers must enter unique email addresses for each account. Once the setup is complete, customers can create new AWS Accounts or bring existing accounts under AWS Control Tower Management. See About AWS accounts in AWS Control Tower to learn more.
Many customers who had already developed custom landing zones told us that they have existing log archive and security accounts that they would like to reuse. Being able to use the existing Logging account will let them consolidate their logs and config aggregators in the same account.
In this post we demonstrate how to reuse existing core or security AWS accounts when deploying AWS Control Tower. Using this feature, customers will save time and effort that may be required to modify AWS native or third-party integrations they have done in their core accounts.
Use case overview
The following use cases are where you would want to use existing AWS account(s) as the AWS Control Towers log archive and audit account.
Let’s assume that you’re using the AWS CloudTrail for an organization feature, which lets you log events for the management account and all member accounts in the organization. Ideally, you’d still want to use the same account to log AWS CloudTrail and AWS Config with AWS Control Tower as well, especially if you have third-party integrations with this account for post-log processing. Now you can use these accounts when deploying AWS Control Tower to make them Audit and Log Archive accounts.
Another use case is when you’re using one of your existing accounts as a delegated admin for different AWS services, such as AWS Security Hub or AWS GuardDuty, and you want the ability to use the same account for this task as AWS Control Tower’s Audit account.
Considerations
The following should be considered before proceeding:
- Check out ‘Consideration for bringing existing security and logging accounts’.
- AWS Control Tower will move these accounts to the OU that it creates as a part of the deployment.
- AWS Control Tower creates its own Config Aggregator in addition to any Config aggregator that you may have.
- If you have AWS Config deployed in any other accounts that you want to enroll with AWS Control Tower and you still want to continue the same AWS Config recorder and Delivery Channel with AWS Control Tower, then you must follow the steps here before deploying AWS Control Tower.
Prerequisites
You must have the following prerequisites before proceeding:
- Prerequisites to deploy AWS Control Tower.
- Existing core or shared account(s) must already be part of your organization.
- Delete the AWS Config recorder and AWS Config Delivery channel from the accounts that you want to use for this feature. This must be done for every region that you want to govern with AWS Control Tower.
Steps to use Deploy Control Tower with existing accounts
The following steps will let you udse Deploy Control Tower with existing accounts:
- Go to AWS Control Tower in your AWS management console.
- Select Set up landing zone.
- Review pricing and select regions.
- Configure OUs.
- Select Use existing account (see the following screenshots).
Here, you will enter the Log Archive account ID
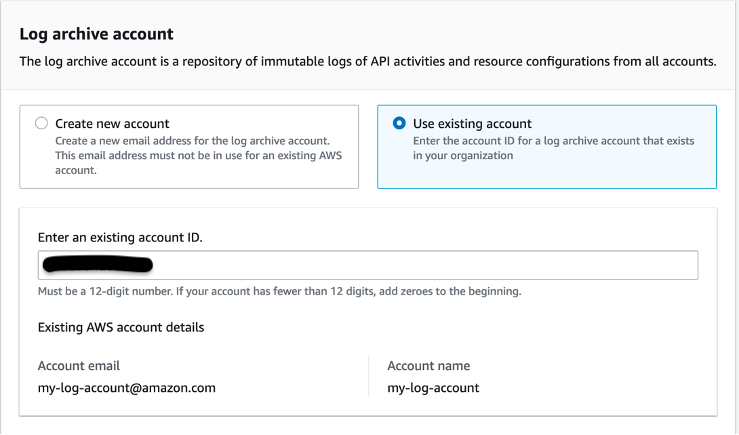
Figure 1. This screen capture illustrates the configuration for using an existing account where you can enter the account id for log archive account
Now, you will enter the Audit account ID
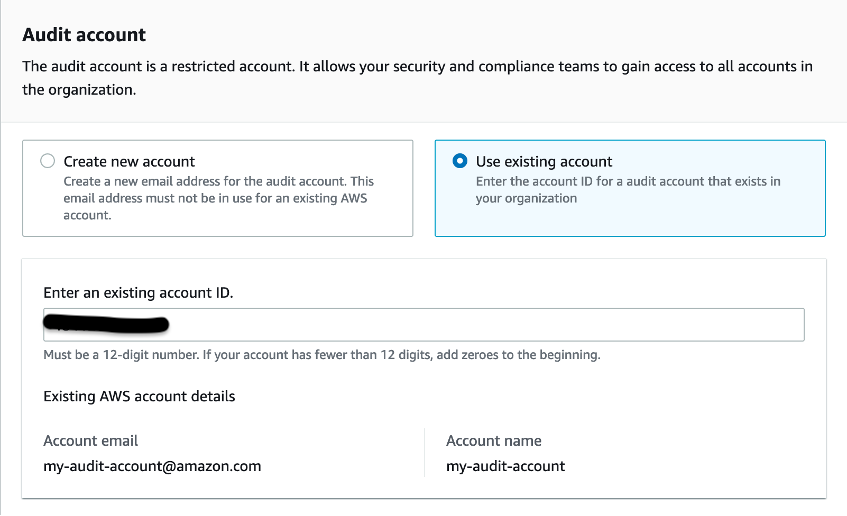
Figure 2. This screen capture illustrates the configuration for using an existing account where you can enter the account id for audit account
- Select Next
- Review the Service permissions, and when you’re ready, choose I understand the permissions AWS Control Tower will use to administer AWS resources and enforce rules on my behalf.
- To finalize your selections and initialize launch, choose Set up landing zone.
Once AWS Control Tower is fully-deployed, you’ll see that the accounts that you used in the steps above are now registered with AWS Control Tower, showing as Enrolled in the AWS Control Tower dashboard. See the following screenshot which shows that the existing accounts security and log-archive that I had chosen to use with AWS Control Tower are now enrolled in AWS Control Tower as AWS Control Towers core accounts.
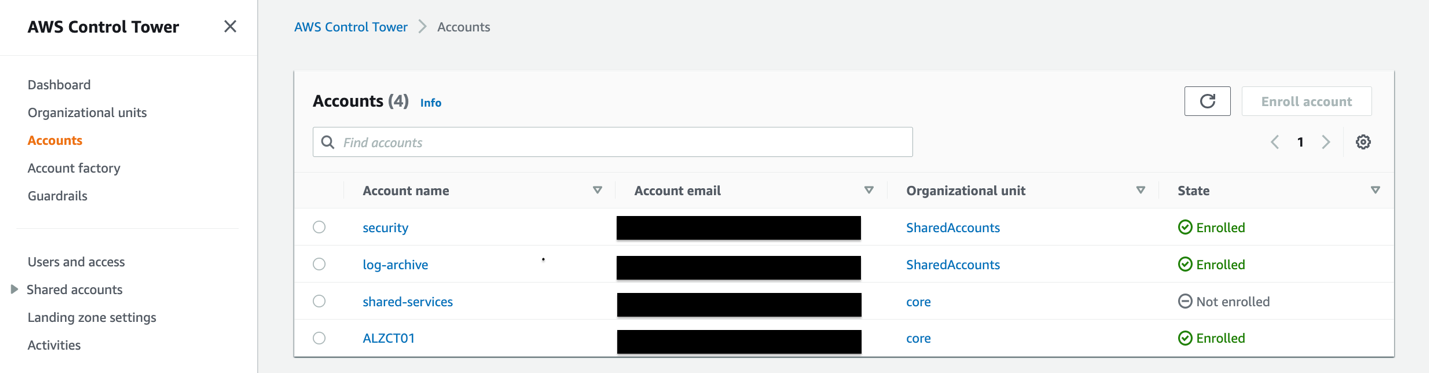
Figure 3. In this screenshot you see once Control Tower is deployed, the existing Log and Audit accounts are being used with Control Tower
Additional CloudTrail trails deployed by AWS Control Tower in the accounts that you chose when deploying AWS Control Tower. See the following screenshot from my AWS account which shows two CloudTrail trails: my-log-account-cloudtrail, which I had before deploying AWS Control Tower, and aws-controltower-BaselineCloudTrail, which AWS Control Tower deploys in the existing accounts that I chose to use with AWS Control Tower. Moreover, the S3 buckets for these two trails are different, as can be seen from the following screenshot.
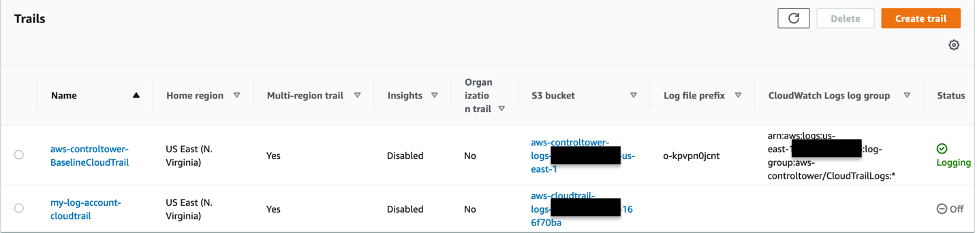
Figure 4. In this screenshot, you will see that Control Tower deploys its own Cloudtrail trail in the existing log account that you used during Control Tower deployment
Similarly, in the following screenshot you’ll see two AWS Config Aggregators: my-custom-aggregator which I had deployed before deploying AWS Control Tower, and aws-controltower-GuardRailsComplianceAggregator that AWS Control Tower deploys in my Audit account.
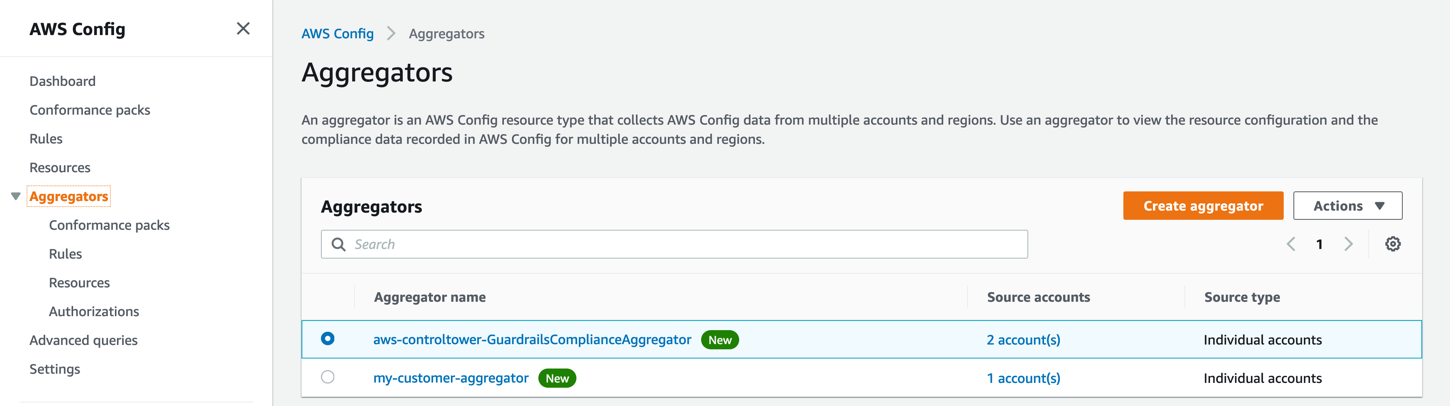
Figure 5. In this screenshot, you see that Control Tower creates its own AWS Config aggregator in the Audit account
Example scenario
Let’s assume you have an existing solution that uses account level CloudTrail logs with AWS Athena to analyze data. The following steps will show you how you can make changes to the existing logging solution to be used with AWS Control Tower deployed resources.
First, in your management account, setup AWS Control Tower with your existing logging account (the following steps). AWS Control Tower will deploy an account level CloudTrail trail in all AWS Control Tower managed accounts and will create an S3 bucket in your existing logging account called aws-controltower-logs-<account-id>-<region>. Once the landing zone has been setup, verify that the CloudTrail logs are being populated in AWS Control Tower created logging bucket.
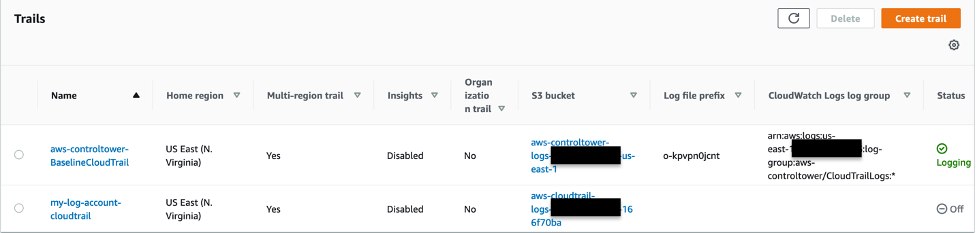
Figure 6. In this screenshot, you will see that Control Tower deploys its own Cloudtrail trail in the existing log account that you used during Control Tower deployment
In the CloudTrail console, select Event History, then select Create Athena Table, select the correct bucket in the drop-down menu, and then select “Create Table”.
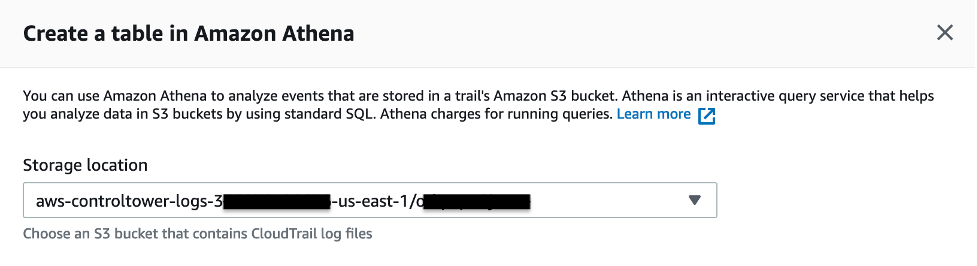
Figure 7. In this screenshot, you will see create a Athena table by entering the S3 location of the logs
You may also copy over the logs from the bucket that your existing trail was logging in into the AWS Control Tower-created S3 bucket for Cloudtrail and Config logs. You have essentially modified your solution to be used with AWS Control Tower’s CloudTrail logs in the existing account.
Once you make sure that your solution works as expected, you can choose to disable the previous CloudTrail trail to avoid log duplication.
Conclusion
In this post, you learned how to reuse your existing logging and security accounts when deploying AWS Control Tower to make them AWS Control Tower’s core or shared account. Therefore, you won’t need to reconfigure integrations that you’ve done with the existing accounts, and you won’t need to worry about importing historical logs or data from these accounts.
If you want to learn more about this feature, read About AWS Accounts in AWS Control Tower and Enroll an existing AWS account.
About the authors: