AWS Security Blog
Protect your generative AI applications against encoding-based attacks with Amazon Bedrock Guardrails
Amazon Bedrock Guardrails provides configurable safeguards to help you safely build generative AI applications at scale. It offers integrated safety and privacy protections that work across multiple foundation models (FMs), including models available in Amazon Bedrock and models hosted outside Amazon Bedrock from other providers. Bedrock Guardrails currently offers six key safeguards to help prevent […]
Simplified model access in Amazon Bedrock
October 22, 2025: This post was updated to reflect additional IAM permissions necessary for Amazon Bedrock serverless models offered through AWS Marketplace. Amazon Bedrock has simplified how you access foundation models, streamlining the integration of AI capabilities into your applications. Here’s what’s changed and how to maintain control over model access in your organization. What’s […]
Securing AI agents with Amazon Bedrock AgentCore Identity
By using Amazon Bedrock AgentCore, developers can build agentic workloads using a comprehensive set of enterprise-grade services that help quickly and securely deploy and operate AI agents at scale using any framework and model, hosted on Amazon Bedrock or elsewhere. AgentCore services are modular and composable, allowing them to be used together or independently. To […]
How to configure and verify ACM certificates with trust stores
In this post, we show how to configure customer trust stores to work with public certificates issued through AWS Certificate Manager (ACM). Organizations can encounter challenges when configuring trust stores for ACM certificates and incorrect trust store configuration can lead to SSL/TLS errors and application downtime. While most modern web browsers and operating systems trust […]
Should I use managed login or create a custom UI in Amazon Cognito?
October 8, 2025: This blog post has been updated to include the Amazon Cognito managed login experience. The managed login experience has an updated look, additional features, and enhanced customization options. September 8, 2023: It’s important to know that if you activate user sign-up in your user pool, anyone on the internet can sign up […]
New AWS whitepaper: Security Overview of Amazon EKS Auto Mode
Amazon Web Services (AWS) has released a new whitepaper: Security Overview of Amazon EKS Auto Mode, providing customers with an in-depth look at the architecture, built-in security features, and capabilities of Amazon Elastic Kubernetes Service (Amazon EKS) Auto Mode. The whitepaper covers the core security principles of Amazon EKS Auto Mode, highlighting its unique approach […]
Defending against supply chain attacks like Chalk/Debug and the Shai-Hulud worm
Building on top of open source packages can help accelerate development. By using common libraries and modules from npm, PyPI, Maven Central, NuGet, and others, teams can focus on writing code that is unique to their situation. These open source package registries host millions of packages that are integrated into thousands of programs daily. Unfortunately, […]
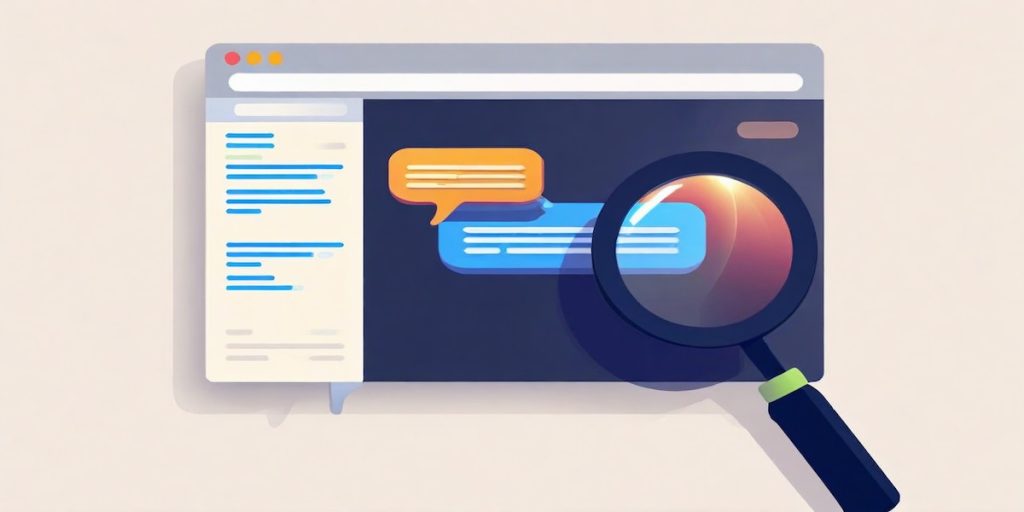
Defending LLM applications against Unicode character smuggling
When interacting with AI applications, even seemingly innocent elements—such as Unicode characters—can have significant implications for security and data integrity. At Amazon Web Services (AWS), we continuously evaluate and address emerging threats across aspects of AI systems. In this blog post, we explore Unicode tag blocks, a specific range of characters spanning from U+E0000 to […]
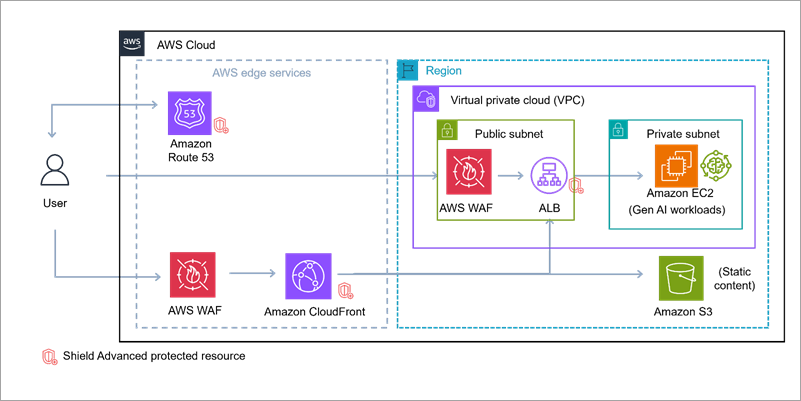
Build secure network architectures for generative AI applications using AWS services
As generative AI becomes foundational across industries—powering everything from conversational agents to real-time media synthesis—it simultaneously creates new opportunities for bad actors to exploit. The complex architectures behind generative AI applications expose a large surface area including public-facing APIs, inference services, custom web applications, and integrations with cloud infrastructure. These systems are not immune to […]
Enabling AI adoption at scale through enterprise risk management framework – Part 2
In Part 1 of this series, we explored the fundamental risks and governance considerations. In this part, we examine practical strategies for adapting your enterprise risk management framework (ERMF) to harness generative AI’s power while maintaining robust controls. This part covers: Adapting your ERMF for the cloud Adapting your ERMF for generative AI Sustainable Risk […]