AWS Security Blog
AWS Achieves Spain’s ENS High Certification Across 29 Services
AWS has achieved Spain’s Esquema Nacional de Seguridad (ENS) High certification across 29 services. To successfully achieve the ENS High Standard, BDO España conducted an independent audit and attested that AWS meets confidentiality, integrity, and availability standards. This provides the assurance needed by Spanish Public Sector organizations wanting to build secure applications and services on […]
AWS Key Management Service now offers FIPS 140-2 validated cryptographic modules enabling easier adoption of the service for regulated workloads
May 24, 2023: As of May 2023, AWS KMS is now certified at FIPS 140-2 Security Level 3. AWS Key Management Service (KMS) now uses FIPS 140-2 validated hardware security modules (HSM) and supports FIPS 140-2 validated endpoints, which provide independent assurances about the confidentiality and integrity of your keys. Having additional third-party assurances about […]
How we reduce complexity and rapidly iterate on Amazon GuardDuty: twelve new detections added
We’re relentlessly innovating on your behalf at AWS, especially when it comes to security. Last November, we launched Amazon GuardDuty, a continuous security monitoring and threat detection service that incorporates threat intelligence, anomaly detection, and machine learning to help protect your AWS resources, including your AWS accounts. Many large customers, including General Electric, Autodesk, and […]
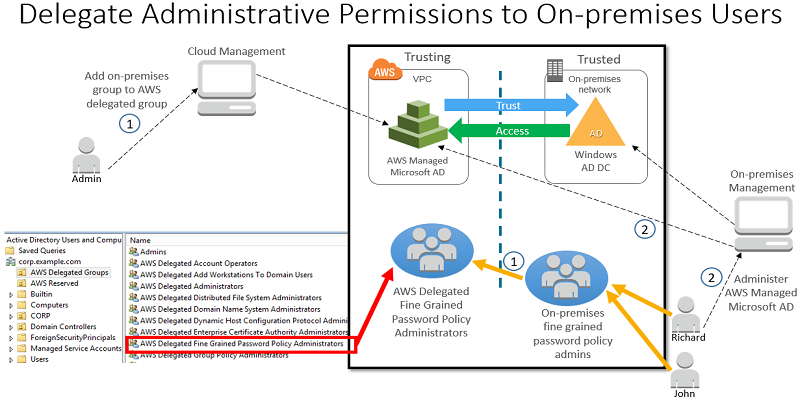
How to Delegate Administration of Your AWS Managed Microsoft AD Directory to Your On-Premises Active Directory Users
You can now enable your on-premises users administer your AWS Directory Service for Microsoft Active Directory, also known as AWS Managed Microsoft AD. Using an Active Directory (AD) trust and the new AWS delegated AD security groups, you can grant administrative permissions to your on-premises users by managing group membership in your on-premises AD directory. […]
AWS Secret Region expands to include 11 new services
As a follow up to our initial region availability on November 20, 2017, I’m happy to announce that we have expanded the number of accredited services available in the AWS Secret Region by an additional 11 services. We continue to be the only cloud service provider with accredited regions to address the full range of […]
How to Use Bucket Policies and Apply Defense-in-Depth to Help Secure Your Amazon S3 Data
Amazon S3 provides comprehensive security and compliance capabilities that meet even the most stringent regulatory requirements. It gives you flexibility in the way you manage data for cost optimization, access control, and compliance. However, because the service is flexible, a user could accidentally configure buckets in a manner that is not secure. For example, let’s […]
AWS Federated Authentication with Active Directory Federation Services (AD FS)
Today we’d like to walk you through AWS Identity and Access Management (IAM), federated sign-in through Active Directory (AD) and Active Directory Federation Services (ADFS). With IAM, you can centrally manage users, security credentials such as access keys, and permissions that control which resources users can access. Customers have the option of creating users and […]
How to retrieve short-term credentials for CLI use with AWS IAM Identity Center
May 23, 2022: This blog post is out of date. Please refer here for current info: https://docs.aws.amazon.com/cli/latest/userguide/cli-configure-sso.html September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. Today, AWS made it easier to use […]
How to Use New Advanced Security Features for Amazon Cognito User Pools
September 8, 2023: It’s important to know that if you activate user sign-up in your user pool, anyone on the internet can sign up for an account and sign in to your apps. Don’t enable self-registration in your user pool unless you want to open your app to allow users to sign up. Amazon Cognito […]
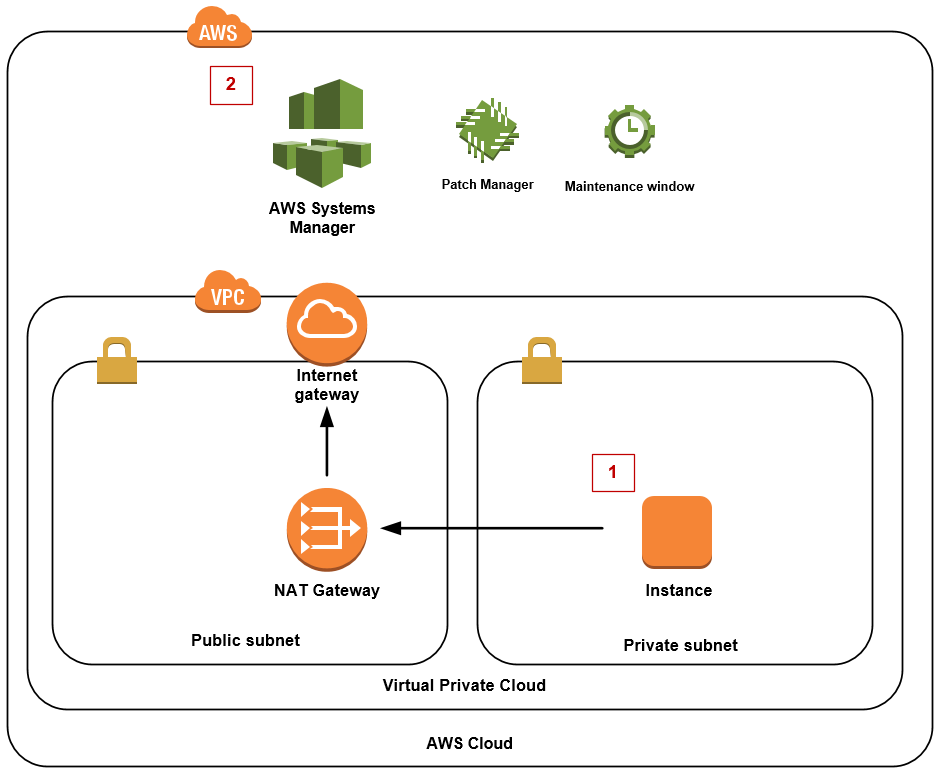
How to Patch Linux Workloads on AWS
Most malware tries to compromise your systems by using a known vulnerability that the operating system maker has already patched. As best practices to help prevent malware from affecting your systems, you should apply all operating system patches and actively monitor your systems for missing patches. In this blog post, I show you how to […]