AWS Security Blog
Tag: Security Blog
Introducing Improved User Search Functionality in the IAM Console
We are happy to announce that we recently launched improved search functionality on the Users page in the AWS Identity and Access Management (IAM) console. For starters, we have enabled you to find an IAM user by their access key ID. Simply paste an access key ID in the Filter box on the Users page. If […]
How to Configure Your EC2 Instances to Automatically Join a Microsoft Active Directory Domain
Seamlessly joining Windows EC2 instances in AWS to a Microsoft Active Directory domain is a common scenario, especially for enterprises building a hybrid cloud architecture. With AWS Directory Service, you can target an Active Directory domain managed on-premises or within AWS. How to Connect Your On-Premises Active Directory to AWS Using AD Connector takes you […]
In Case You Missed These: AWS Security Blog Posts from March and April
In case you missed any of the AWS Security Blog posts from March and April, they are summarized and linked to below. The posts are shown in reverse chronological order (most recent first), and the subject matter ranges from the AWS Config Rules repository to automatically updating AWS WAF IP blacklists. April April 28, AWS […]
How to Control Access to Your Amazon Elasticsearch Service Domain
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. With the recent release of Amazon Elasticsearch Service (Amazon ES), you now can build applications without setting up and maintaining your own search cluster on Amazon EC2. One of the key benefits of using Amazon ES is that you can […]
How to Optimize and Visualize Your Security Groups
September 9, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. May 3, 2017: We published a related blog post also written by Guy Denney, How to Visualize and Refine Your Network’s Security by Adding Security Group IDs to Your VPC Flow Logs. Many organizations start their journey with AWS by experimenting […]
How to Import IP Address Reputation Lists to Automatically Update AWS WAF IP Blacklists
Note from July 3, 2017: The solution in this post has been integrated into AWS WAF Security Automations, and AWS maintains up-to-date solution code in the companion GitHub repository. You can use AWS WAF (a web application firewall) to help protect your web applications from exploits that originate from groups of IP addresses that are known […]
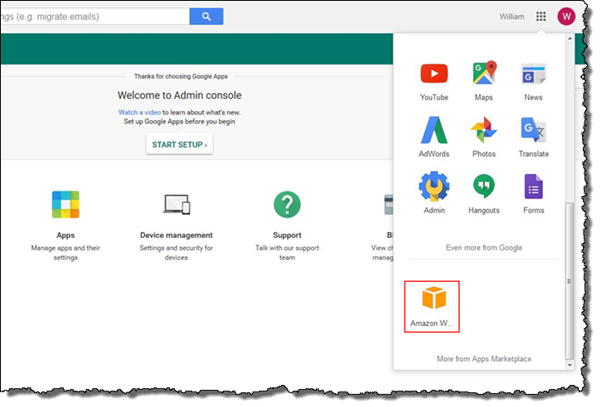
How to Set Up Federated Single Sign-On to AWS Using Google Apps
March 10, 2020: This blog post is out of date. Please refer to this post for updated info: How to set up federated single sign-on to AWS using Google Workspace The AWS Security Blog has covered a variety of solutions for federating single sign-on (SSO) to the AWS Management Console. For example, How to Connect […]
Amazon Cognito Now Provides Sign-Up and Sign-In Functionality for Your Apps (Beta)
Today, Amazon Cognito launched the beta of a new feature that makes it easy for developers to add sign-up and sign-in functionality to mobile and web apps. With this new feature, you get a simple, fully managed service you can use to create and maintain your user pool that can scale to hundreds of millions […]
Now Generally Available: Amazon Inspector
Yesterday, AWS announced that Amazon Inspector, an automated security assessment service, is now available to all customers. Inspector helps you improve the security and compliance of your applications running on Amazon Elastic Compute Cloud (Amazon EC2) by identifying potential security issues, vulnerabilities, or deviations from security standards. You pay only for the assessments you run, with […]
Frequently Asked Questions About HIPAA Compliance in the AWS Cloud
Today, we continue a series of AWS cloud compliance FAQs by focusing on the Health Insurance Portability and Accountability Act (HIPAA) and protected health information (PHI). AWS’s Healthcare and Life Science customers are doing important things for their customers in the AWS cloud, and we are excited to work with our partners to help tackle […]