AWS Partner Network (APN) Blog
Defending Against Ransomware with AWS and Cohesity FortKnox
By Edwin Galang, Cloud Solutions Architect – Cohesity
By Girish Chanchlani, Principal Solutions Architect – AWS
 |
| Cohesity |
 |
With an increase in frequency and severity of ransomware incidents worldwide, enterprises are under pressure to better safeguard their mission-critical data.
Organizations have deployed a variety of solutions to isolate their data from threats, such as offsite tape storage which is secure but slow to recover data and can lead to missed service-level agreements (SLAs). To overcome this, customers have deployed do-it-yourself (DIY) data vaults at remote sites that make data more accessible but only somewhat secure.
The challenge with these solutions is that they are complex, error-prone, and costly to manage. More importantly, the responsibility of maintaining these solutions and ensuring data resiliency falls on enterprises which are already struggling with a shortage of resources. This forces them to look for trusted partners to help share the responsibility.
To address this, Cohesity launched FortKnox, a modern data isolation and recovery-as-a-service solution that runs on Amazon Web Services (AWS). It helps customers maintain an immutable virtual air-gapped copy of backup data that acts as an additional layer of protection against ransomware and other cybersecurity threats.
Cohesity is an AWS Storage Competency Partner that’s redefining data management to lower total cost of ownership (TCO) while simplifying the way businesses manage and protect their data.
FortKnox is a software-as-a-service (SaaS) solution that enables companies to quickly deploy, maintain, and monitor isolated copies of their critical data in a secure, offsite environment, all managed by Cohesity. The protected copy of backup data in FortKnox can be recovered to the original or alternate “clean room” location, including a private or public cloud in case of a security breach.
FortKnox is part of Cohesity Data Management as a Service (DMaaS), a portfolio of “as-a-service” offerings that enable organizations to meet their data protection, business continuity, disaster recovery and data isolation requirements.
In this post, we will walk through the process of configuring Cohesity FortKnox for protecting your backup data from ransomware. You’ll learn how to prevent unauthorized access to the backup data and recover it in case of a ransomware attack. We will also highlight how FortKnox ensures your backup data is kept free from infections via its built-in anomaly detection capabilities.
Overview of Cohesity FortKnox
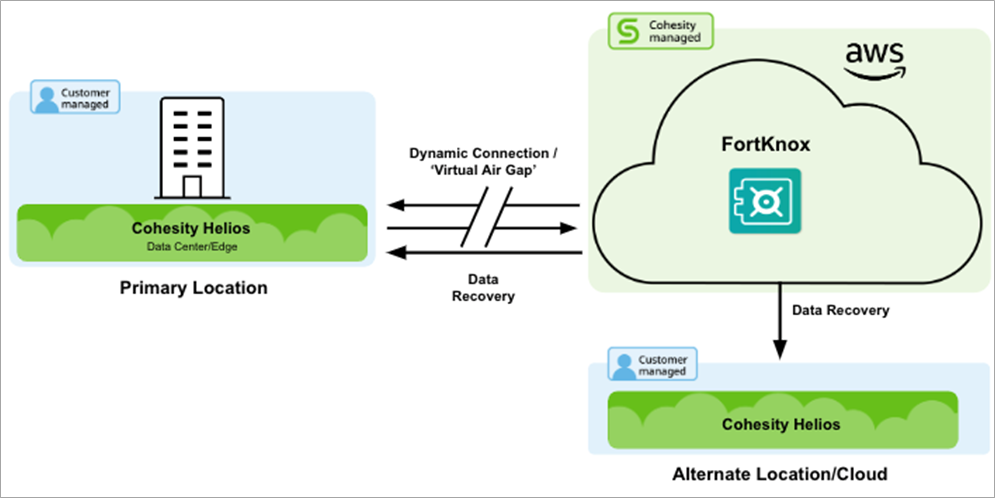
Cohesity FortKnox provides a secure, virtual air-gapped vault for storing backup data. Cohesity’s clusters, deployed either on premises or in the cloud, use FortKnox for securing backup data from malware such as ransomware.
Figure 1 – Cohesity FortKnox overview.
At the core of FortKnox is a multilayered defense-in-depth strategy that goes beyond Zero Trust to ensure the vaulted copy of data is the gold standard that customers can fall back on in case of a cybersecurity attack.
This is achieved through geographical, network, and operational isolation that ensures the vault data and policies are inaccessible to both external and internal bad actors, limiting data exfiltration vectors.
Here are some of the ways that FortKnox keeps data safe:
- Virtual air gap through a secure and temporary network connection between the backup (secondary) copy and the vault (tertiary) copy that is cut off once the data has been vaulted.
- Operational isolation through Cohesity or customer-managed key management system or AWS Key Management Service (AWS KMS), to prevent users who have access to the backup cluster from accessing or restoring vault data.
- Tamper resistance via immutability offered by Amazon Simple Storage Service (Amazon S3) object lock, data-at-rest and data-in-flight encryption, and separate workflows for vaulting and recovering data.
- Access controls through role-based access control (RBAC), multi-factor authorization (MFA), and short-term token-based authentication to prevent unauthorized access of vault data.
- Quorum that requires at least two authorized users to approve critical actions such as recovery of vault data. This prevents any unilateral changes to the vault policies.
- Anomaly detection through machine learning (ML) intelligence, which helps identify a clean copy of data for recovery.
Configuring Cohesity FortKnox
Cohesity Helios is the centralized control plane running as a SaaS service on AWS that provides customers a single pane of glass to manage their Cohesity clusters and DMaaS services including Cohesity FortKnox.
After a customer has registered their Cohesity cluster or clusters in Helios, they are ready to configure, manage, and use the FortKnox service.
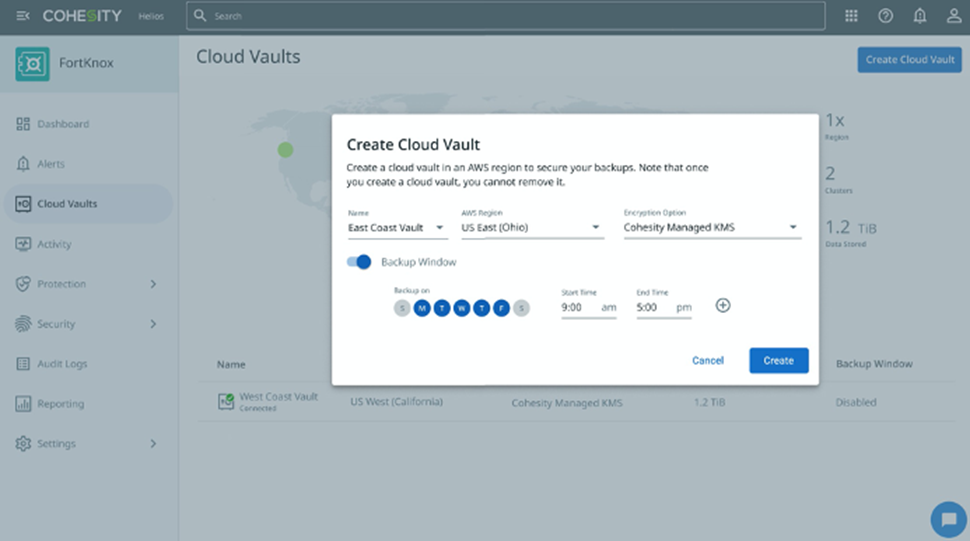
From the Helios dashboard, you can navigate to the FortKnox dashboard. As shown below, the first step to using FortKnox is to create a cloud vault by selecting a region where you would like to vault your data.
For added security, you can select a backup window that only allows data to be written to your cloud vault during that window.
Figure 2 – Create FortKnox cloud vault with schedule.
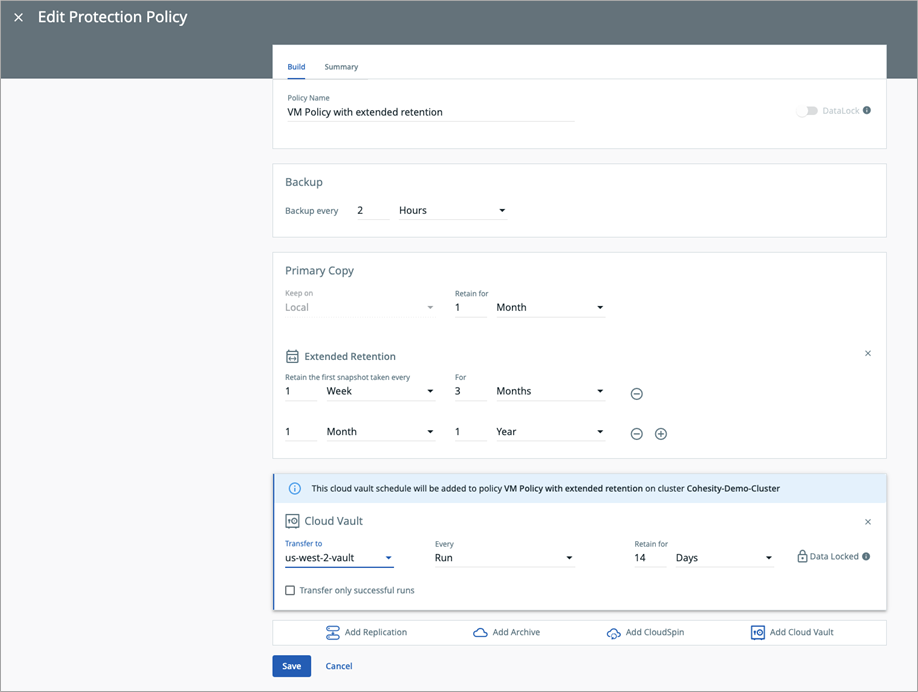
After the cloud vault has been created, you can configure a protection policy or policies to use the cloud vault to store your data. In the protection policy, you click on Add a Cloud Vault and select the cloud vault, when the data should be written to the vault, and how long the data should be retained for.
The data stored in the cloud vault will be immutable until retention date expires.
Figure 3 – Configure protection policy to store data in FortKnox cloud vault.
When the next backup runs, the data will be replicated and stored in the cloud vault.
Using Quorum Groups to Control Operations in FortKnox
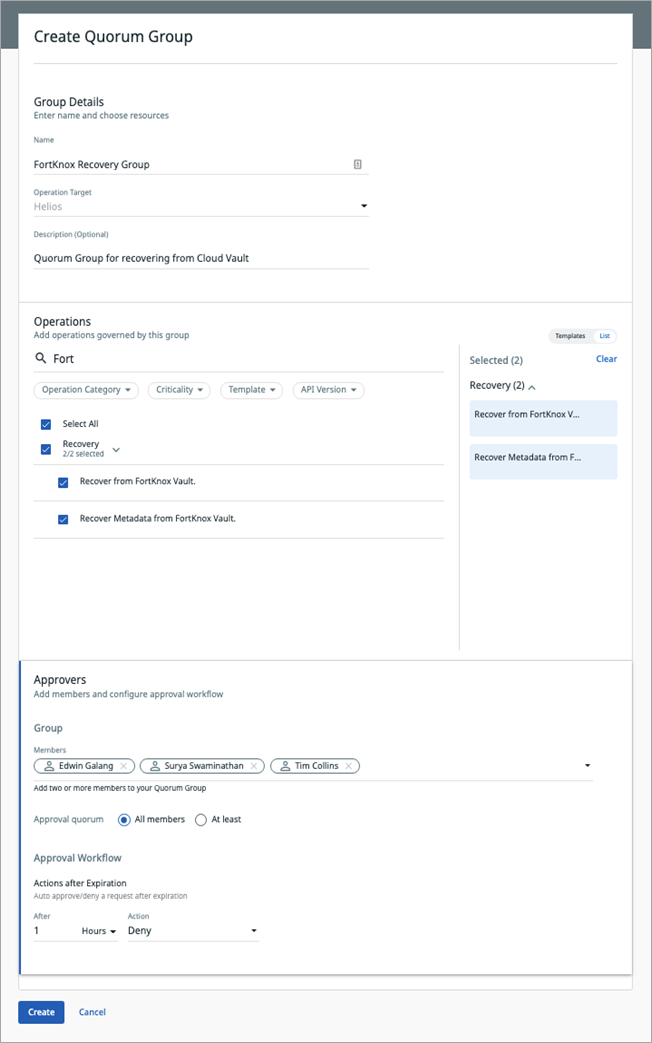
To control operations like recovering data from a cloud vault in FortKnox, a quorum group is configured that requires a minimum of two quorum group members to approve the operation before it can run. This feature provides an additional safeguard against rogue admins or users who try to misuse their access.
The figure below highlights creation of a quorum group, and the “FortKnox Recovery Group” requires all members of the group to approve any recovery operations from the cloud vault. If all members do not approve the operation, the data recovery operation will be denied.
Quorum groups can also be used to control other operations on the cluster such as policy updates and access management.
Figure 4 – Quorum group for FortKnox recovery operations.
Recovering Data from FortKnox
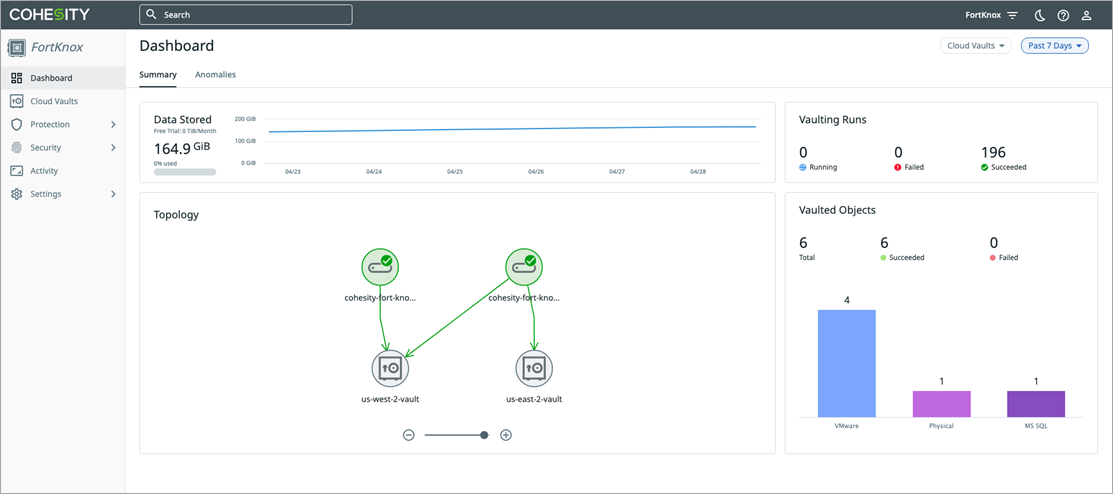
The FortKnox dashboard shown below displays information about your FortKnox environment, which includes the amount of data stored in the service, number of cloud vaults, and number of vaulted objects stored in the vault.
FortKnox currently supports vaulting of a variety of data sources including VMware, Hyper-V virtual machines, physical servers (Windows/Linux), Network Attached Storage (NAS) workloads, Microsoft 365, Oracle, and SQL across data centers.
Additional workloads are constantly being added, and the most updated list of supported workloads can be found on the Cohesity website.
Figure 5 – FortKnox dashboard.
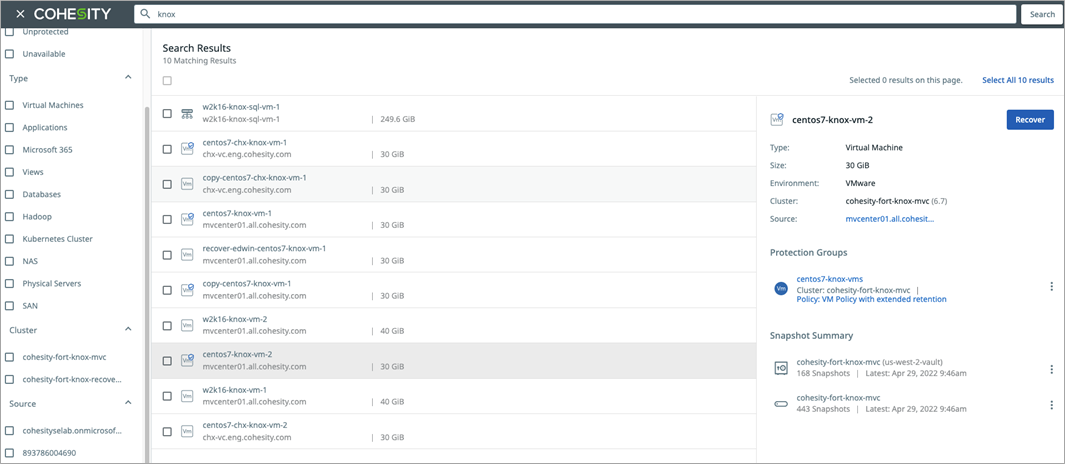
To recover data from FortKnox, you can use the search bar at the top of the dashboard to find and select the data to be recovered. You can filter the searched data to narrow down the results.
Filters include:
- Type: Type of objects to include, such as virtual machine, NAS, or Microsoft 365
- Cluster: Cohesity cluster
- Status: Object is protected, unprotected, or unavailable
- Source: Source of the backup data, such as vCenter
Figure 6 – Search for data to recover in FortKnox.
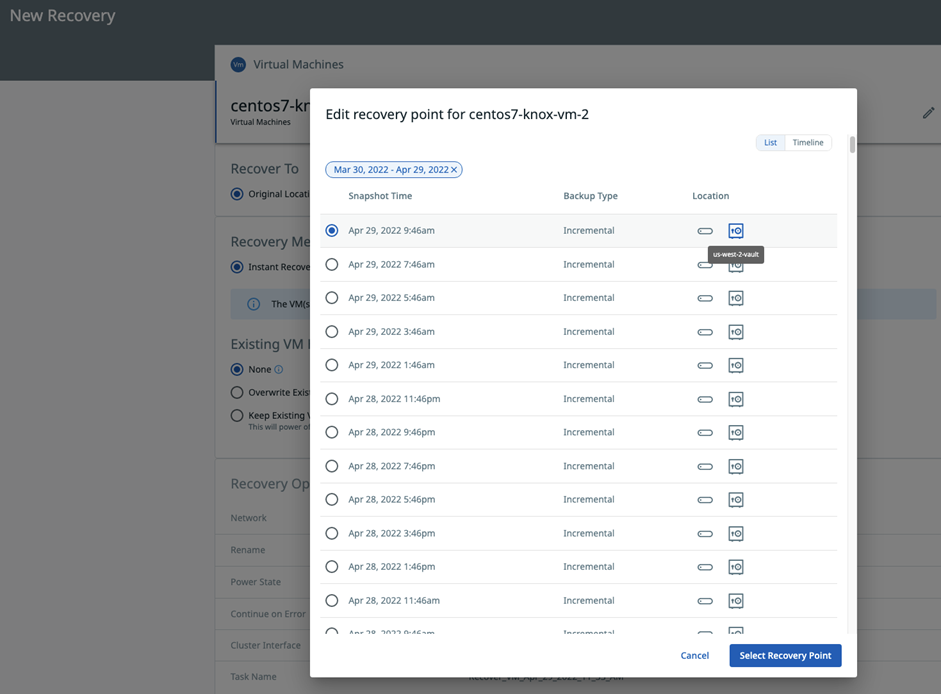
In the New Recovery wizard, select the recovery point and cloud vault location and then click Select Recovery Point.
Figure 7 – Select recovery point and cloud vault location.
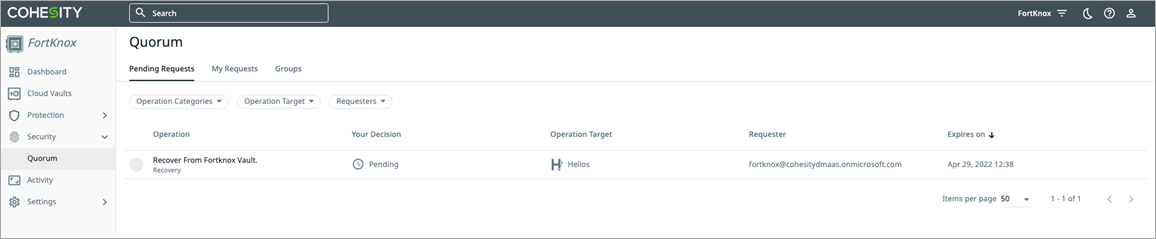
After you have selected the recovery point, you choose the recovery option (original or new location, recovery method) and submit the recovery request.
The recovery request will be submitted for approval to the members of the FortKnox Recovery Group.
Figure 8 – Quorum group pending request.
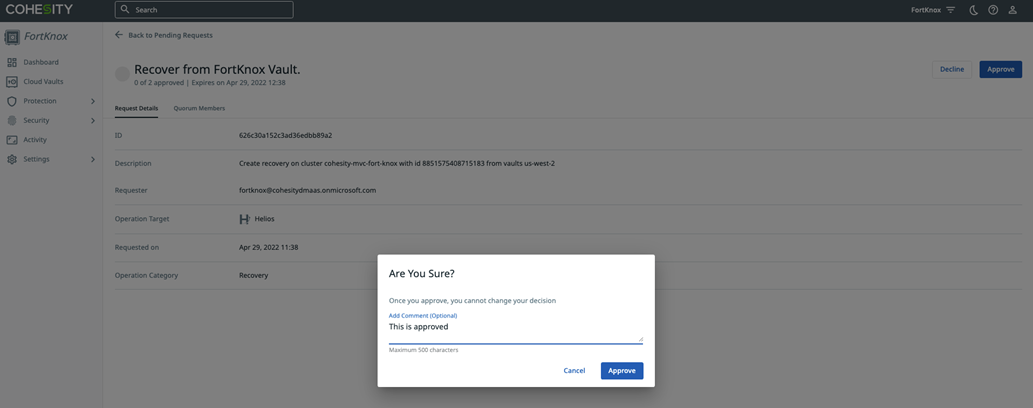
Members of the quorum group must approve the request in order for the restore operation to run.
Figure 9 – Quorum group request approval.
Only after all the quorum group members approve the operation, the recovery process will start running.
Recovering Data from FortKnox to Another Cohesity Cluster
Data can be recovered from FortKnox to a different Cohesity cluster in the customer’s environment in case the original cluster is no longer available. A new/alternate cluster may be required for recovery if there is a ransomware event or disaster and the original cluster is no longer available or needs to be sanitized, or forensics need to be run on it.
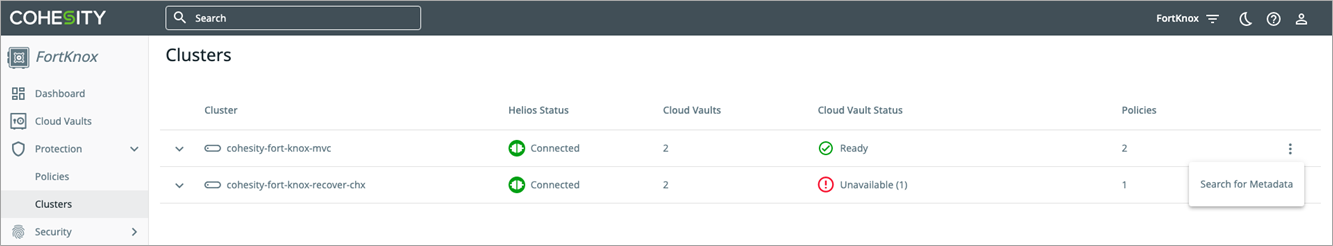
From the FortKnox navigation menu go to Protection > Clusters and then select the cluster you want to recover data to. Click on the ellipse button > Search for Metadata. The metadata contains information about the backup data which is used to retrieve the backup to the cluster.
Figure 10 – Recover to different cluster.
In the Search for Metadata wizard, select the date range, source cluster, and cloud vaults, and then press Search. Quorum group approval is required to retrieve the data from the cloud vault to the new cluster. After the data has been retrieved by the new cluster, the data can be restored using the FortKnox recovery workflow shown in the previous section.
Anomaly Detection in Backup Data
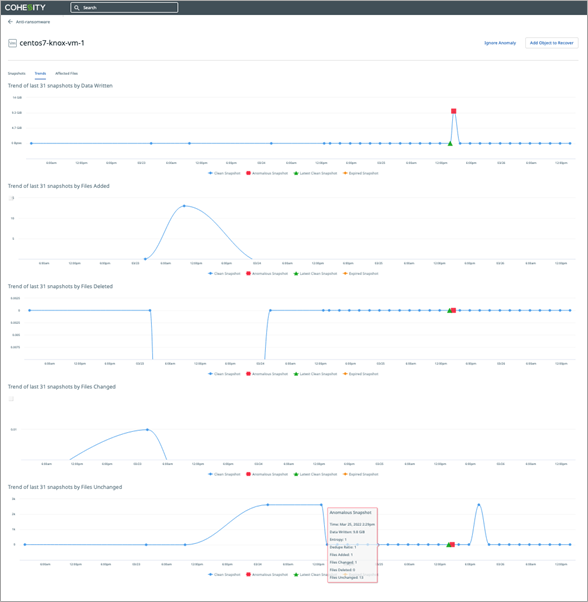
Cohesity uses machine learning anomaly detection to monitor for any anomalies in the backup data stored in FortKnox. This checks for sudden changes in the data over time, changes in data entropy, and changes in the nature of the file system.
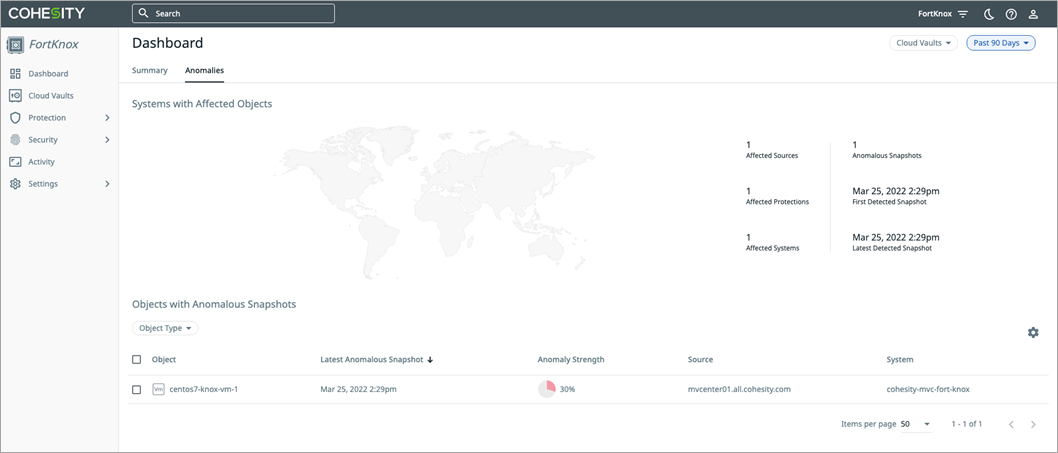
FortKnox enables users to view such anomalous snapshots from the FortKnox user interface (UI) that also manages and monitors global vaults, providing a single plane of glass to monitor the health of clusters and vaults.
The figure below highlights an anomaly that has been detected in one of the backup snapshots and displayed on the dashboard.
Figure 11 – Anomaly dashboard.
Customers can review information about all of the anomalies in the FortKnox dashboard and recover data from the last known good snapshot.
Figure 12 – Detailed anomaly information about the data.
Conclusion
In this post, we introduced Cohesity FortKnox, a secure and easy-to-use data isolation and recovery-as-a-service solution that enables customers to safeguard their data from malware such as ransomware and other cybersecurity threats and disasters.
As the solution is built on AWS, businesses can take advantage of capabilities such as global availability, security, reliability, durability, and scalability. FortKnox ensures integrity of vaulted data through a host of security features such as Amazon S3 object lock that keeps backup data immutable and prevents tampering.
For controlling access to backup data, FortKnox provides quorum groups where approval from at least two people is required before data can be recovered. It also provides anomaly detection to help customers easily spot anomalies in their backup data and roll back to previously known good points in time.
With Cohesity FortKnox’s SaaS-based deployment model, customers can connect, vault, and recover their data while avoiding the complexity and costs of traditional data isolation solutions such as tape or DIY data vaults.
FortKnox improves business continuity by helping organizations prepare for and recover confidently from security incidents with quick, granular recovery back to the original location or an alternate “clean room” target, whether that resides in a private or public cloud.
For more information on Cohesity, visit the FortKnox product page or see it in action in this demo.
Cohesity – AWS Partner Spotlight
Cohesity is an AWS Storage Competency Partner that’s redefining data management to lower total cost of ownership (TCO) while simplifying the way businesses manage and protect their data.