The Internet of Things on AWS – Official Blog
Category: Security, Identity, & Compliance
Designing a Single Pane of Glass for Securing your Globally Deployed IoT-Workload
Introduction Companies are investing in large-scale Internet of Things (IoT) projects and deploying global scale IoT platform such as Deutsche Bahn or Carrier. Enterprises are looking for a solution that offers a multi-tenant Single Pane of Glass Device Lifecycle Management (DLM) which caters to both IT and OT operations. In this blog we will focus […]
Integrating AWS IoT SiteWise and Fleet Hub with IAM Identity Center and Okta
Introduction Many organizations are using an external identity provider to manage user identities. With an identity provider (IdP), you can manage your user identities outside of AWS and give these external user identities permissions to use AWS resources in your AWS accounts. External identity providers (IdP), such as Okta Universal Directory, can integrate with AWS […]
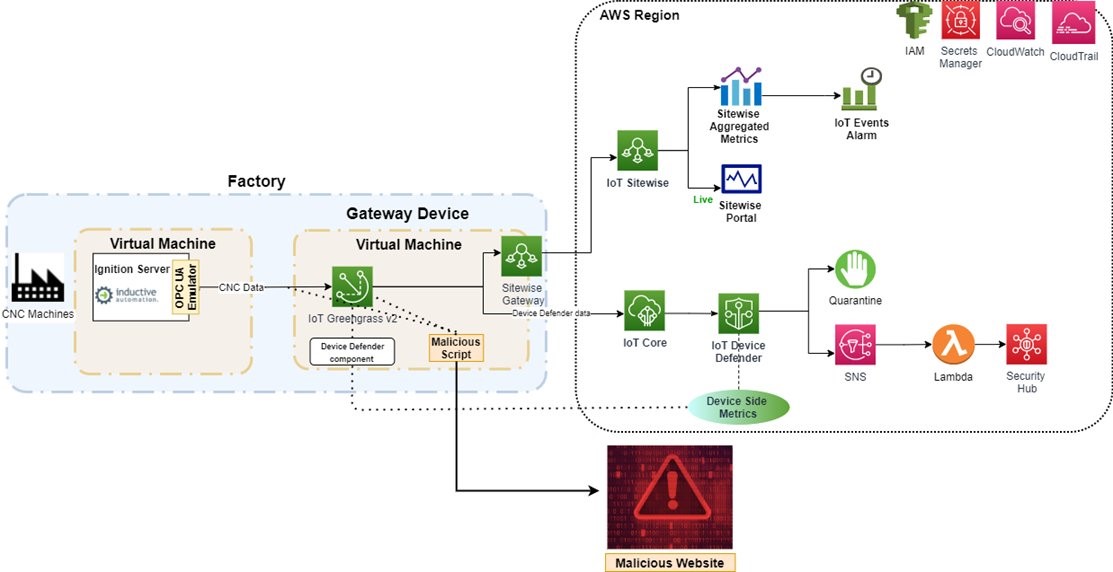
Detect Cryptocurrency Mining Threats on Edge Devices using AWS IoT
Introduction Machine learning (ML) at the edge requires powerful edge requires powerful edge devices with a unique set of requirements. The availability, safety, and security requirements for the edge differ from cloud since they are located at the customer site, outside the data center, and interface directly with operational technology (OT) and the internet. Since […]
Managing Organizational Transformation for Successful OT/IT Convergence
Introduction Industrial organizations are facing a new challenge as they try to merge the traditional physical world (Operational Technology or OT) and the digital world (Information Technology or IT). In our experience, companies who prioritize organizational change management when implementing digital solutions get better results from their investments. This is even more true when building […]
Learn how to secure your IIoT solutions with AWS IIoT security workshop
Introduction Industrial digital transformation is driving changes to the Operational Technology (OT) landscape, making it more connected to the internet and IT systems and solutions. With OT/IT convergence, OT environments are leveraging more IT solutions to improve productivity and efficiency of production operations. Industrial customers can use AWS edge and cloud services to securely access […]
Connected vehicles telemetry – Processing Protobuf messages with AWS IoT Core
Introduction In connect vehicles applications, telemetry data is usually very extensive, containing structure and unstructured data. To send data over to the Cloud you can use Protocol Buffers (Protobuf – binary format). Protobuf provides the application with an efficient yet well structured compressing mechanism. The built-in protocol documentation makes data serialization and deserialization more manageable […]
Automate global device provisioning with AWS IoT Core and Amazon Route 53
Introduction Use AWS IoT Core together with Amazon Route 53 to choose an AWS Region based on geo location or latency and register your devices automatically when they connect for the first time to AWS IoT Core. Time to read 10 minutes Learning level 300 Services used AWS IoT Core,Amazon Route53, Amazon Certificate Manager Private […]
Simplify multi-account device provisioning and certificate authority registration when using AWS IoT Core
Customers often manage multiple AWS accounts to separate their development, staging, and production environments. When deploying IoT workloads on AWS IoT Core, customers usually use unique X.509 certificates for identifying devices and certificate authorities (CAs) for validating the signature of device certificates during provisioning. In this blog, we will demonstrate how to use the newly […]
Increase military readiness with AWS IoT for Defense and National Security
In this post we discuss how AWS IoT for Defense and National Security (IoT4D) increases readiness by driving operational excellence for manufacturing and supply chains, improving sustainability for buildings and bases, improving equipment maintenance and uptime, and providing situational awareness at the tactical edge. IoT workloads securely collect, aggregate, and store data from fleets of […]
Scaling for Complexity – Architecting for Performant Embedded Devices at the Edge – Part 2
The following is a survey paper, published and presented to the Academic Congress of Embedded World 2022 at Nuremberg, Germany on June 21st 2022. Part 1 – Scaling for Complexity – Architecting for Performant Embedded Devices at the Edge – Part 1 Provisioning Layer The provisioning layer of your IoT workloads consists of the Public Key […]