AWS Security Blog
Enable Your Federated Users to Work in the AWS Management Console for up to 12 Hours
AWS Identity and Access Management (IAM) supports identity federation, which enables external identities, such as users in your corporate directory, to sign in to the AWS Management Console via single sign-on (SSO). Now with a small configuration change, your AWS administrators can allow your federated users to work in the AWS Management Console for up to 12 hours, instead of having to reauthenticate every 60 minutes. In addition, administrators can now revoke active federated user sessions.
In this blog post, I will show how to configure the console session duration for two common federation use cases: using Security Assertion Markup Language (SAML) 2.0 and using a custom federation broker that leverages the sts:AssumeRole* APIs (see this downloadable sample of a federation proxy). I will wrap up this post with a walkthrough of the new session revocation process.
Note: If you receive an “Invalid credentials parameter” error when attempting to access the AWS Management Console with a sign-in URL that specifies session duration, see this Knowledge Center article.
How to specify console session duration using SAML 2.0
These instructions assume you have enabled federated access to AWS using Windows Active Directory, Active Directory Federation Services (AD FS), and SAML 2.0. See this AWS Security Blog post for step-by-step instructions about how to set this up.
To specify the duration of a console session when using SAML 2.0, follow these steps:
- From the AD FS Console, right-click the relying party (in this case Amazon Web Services), and then click Edit Claim Rules, as shown in the following screenshot.

- In the Edit Claim Rules for <Relying Party> dialog box, click Add Rule.

- From the Claim rule template list, select Send Claims Using a Custom Rule.

- Specify the following settings:
Claim rule name: SessionDuration
Custom rule:
Note: This example uses 28,800 seconds (or 8 hours), but you can specify your own preferred duration, ranging from from 15 minutes to 12 hours.
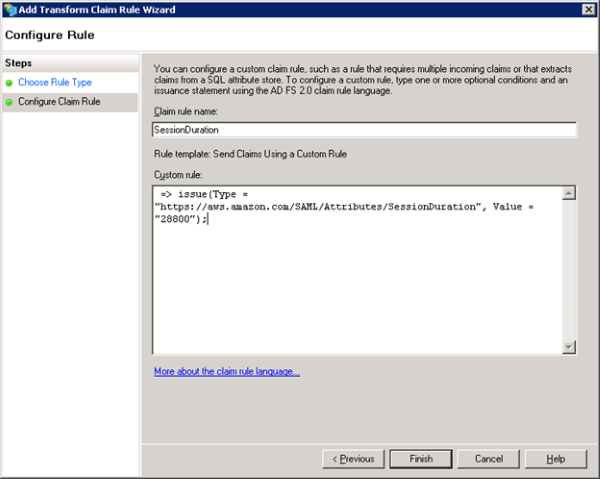
- Click Finish, and then click OK.
Any new console session your federated users initiate will now be valid for the duration specified in the SessionDuration claim. To see a SAML response that includes the new parameter in your browser, see How to View a SAML Response in Your Browser for Troubleshooting.
Important note: In case you already have configured the optional SAML claim SessionNotOnOrAfter to specify the duration of an SSO session when using SAML 2.0, you can continue to use the same SAML claim and specify the duration up to 12 hours. If you configure both SAML claims SessionNotOnOrAfter and SessionDuration, SSO session duration equals the smaller SAML claim value.
How to specify console session duration for a custom federation broker
These instructions assume you have enabled a custom identity broker to access the AWS Management Console. See Creating a URL that Enables Federated Users to Access the AWS Management Console (Custom Federation Broker) to learn how to enable a custom identity broker for this purpose.
To specify the duration of a console session when you federate using a custom identity broker, simply add the new HTTP URL parameter, SessionDuration (expressed in seconds), to your request when calling the AWS federation endpoint.
The following example shows what your request might look like if you specified 12 hours (43,200 seconds). The new SessionDuration parameter is highlighted.
https://signin.aws.amazon.com/federation?Action=getSigninToken&Session=%7B%22sessionId%22%3A%22ASIAEXAMPLEMD
LUUAEYQ%22%2C%22sessionKey%22%3A%22tpSl9thxr2PkEXAMPLETAnVLVGdwC5zXtGDr
%2FqWi%22%2C%22sessionToken%22%3A%22AQoDYXdz%EXAMPLE&SessionDuration=43200
Revocation of open federated sessions
We have also made it easier to revoke open federated sessions for an IAM role with a single click in the IAM console. Revocation invalidates all currently open sessions created by either IAM users or AWS services using the role.
To revoke open federated sessions:
- From the IAM console, click Roles in the left pane, select a role, and then go to the Revoke Sessions tab.

- Click Revoke active sessions. A notification informs you of the actions you are about to take and asks you to confirm your revocation decision.
- When you confirm your decision by clicking Revoke active sessions, IAM attaches to the role the AwsRevokeSessionsPolicy inline policy with a time-based condition. This policy denies all access for role sessions that were active when you clicked Revoke active sessions. In effect, this invalidates all sessions created by either IAM users or AWS services using the role. Note that the policy will not affect any new sessions created after you click the Revoke active sessions button.
To learn more about configuring federated console session duration, see Identity Providers and Federation. If you have comments about setting the session duration or session revocation, submit them in the “Comments” section below. If you have questions about the content of this blog post, please start a new thread in the IAM forum.
– Kai
Want more AWS Security how-to content, news, and feature announcements? Follow us on Twitter.