AWS Security Blog
Manage authorization within a containerized workload using Amazon Verified Permissions
Containerization offers organizations significant benefits such as portability, scalability, and efficient resource utilization. However, managing access control and authorization for containerized workloads across diverse environments—from on-premises to multi-cloud setups—can be challenging. This blog post explores four architectural patterns that use Amazon Verified Permissions for application authorization in Kubernetes environments. Verified Permissions is a scalable permissions management and fine-grained […]
AWS completes the annual Dubai Electronic Security Centre certification audit to operate as a Tier 1 cloud service provider in the Emirate of Dubai
We’re excited to announce that Amazon Web Services (AWS) has completed the annual Dubai Electronic Security Centre (DESC) certification audit to operate as a Tier 1 Cloud Service Provider (CSP) for the AWS Middle East (UAE) Region. This alignment with DESC requirements demonstrates our continued commitment to adhere to the heightened expectations for CSPs. Government […]
2025 ISO and CSA STAR certificates now available with four additional services
Amazon Web Services (AWS) successfully completed an onboarding audit with no findings for ISO 9001:2015, 27001:2022, 27017:2015, 27018:2019, 27701:2019, 20000-1:2018, and 22301:2019, and Cloud Security Alliance (CSA) STAR Cloud Controls Matrix (CCM) v4.0. EY CertifyPoint auditors conducted the audit and reissued the certificates on February 19, 2025. The objective was to assess the level of […]
Support Canada’s CCCS PBHVA overlay compliance with the Landing Zone Accelerator on AWS
Organizations seeking to adhere to the Canadian Centre for Cyber Security (CCCS) Protected B High Value Assets (PBHVA) overlay requirements can use the Landing Zone Accelerator (LZA) on AWS solution with the CCCS Medium configuration to accelerate their compliance journey. To further support customers, AWS recently collaborated with Coalfire to assess and verify the LZA […]
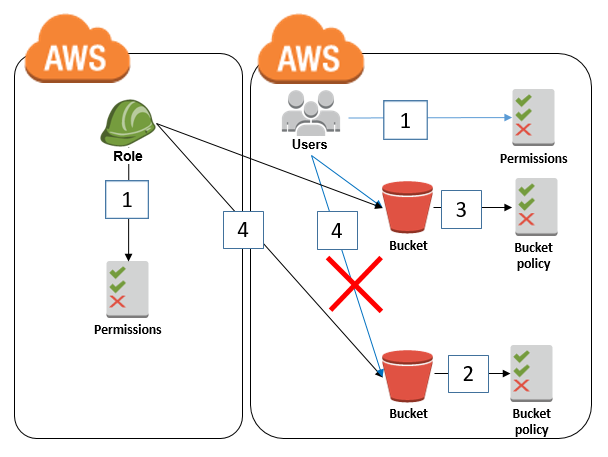
Four ways to grant cross-account access in AWS
As your Amazon Web Services (AWS) environment grows, you might develop a need to grant cross-account access to resources. This could be for various reasons, such as enabling centralized operations across multiple AWS accounts, sharing resources across teams or projects within your organization, or integrating with third-party services. However, granting cross-account access requires careful consideration […]
Connect your on-premises Kubernetes cluster to AWS APIs using IAM Roles Anywhere
February 26, 2025: We’ve updated this post to fix a typo in the code in Step 5 – Deploy your workload. Many customers want to seamlessly integrate their on-premises Kubernetes workloads with AWS services, implement hybrid workloads, or migrate to AWS. Previously, a common approach involved creating long-term access keys, which posed security risks and […]
From log analysis to rule creation: How AWS Network Firewall automates domain-based security for outbound traffic
AWS Network Firewall’s automated domain lists feature enhances network security by analyzing HTTP and HTTPS traffic patterns, providing visibility into domain usage, and simplifying the creation and management of outbound traffic controls through domain-based allowlisting.
How to restrict Amazon S3 bucket access to a specific IAM role
February 14, 2025: This post was updated with the recommendation to restrict S3 bucket access to an IAM role by using the aws:PrincipalArn condition key instead of the aws:userid condition key. April 2, 2021: In the section “Granting cross-account bucket access to a specific IAM role,” we updated the second policy to fix an error. […]
Introducing the AWS Trust Center
We’re launching the AWS Trust Center, a new online resource that shares how we approach securing your assets in the cloud. The AWS Trust Center is a window into our security practices, compliance programs, and data protection controls that demonstrates how we work to earn your trust every day.
The importance of encryption and how AWS can help
February 12, 2025: This post was republished to include new services and features that have launched since the original publication date of June 11, 2020. Encryption is a critical component of a defense-in-depth security strategy that uses multiple defensive mechanisms to protect workloads, data, and assets. As organizations look to innovate while building trust with […]