AWS Storage Blog
From fragmented to fortified: Motability Operations’ journey to a unified backup strategy with AWS
Motability Operations runs the UK’s Motability Scheme and provides vehicle leasing services to approximately 900,000 disabled customers. The organization leases cars, Wheelchair Accessible Vehicles, scooters, and powered wheelchairs, delivering an all-inclusive package with insurance, maintenance, and breakdown coverage that supports independence and mobility for customers across the country. Motability Operations manages diverse AWS workloads across multiple accounts, from customer-facing applications to internal analytics platforms, all handling sensitive customer data that requires robust protection to maintain trust and meet regulatory requirements.
As Motability Operations grew their cloud footprint, they identified gaps in their backup infrastructure that needed to be addressed. The existing architecture lacked defenses against ransomware encryption, deletion, and data tampering, meaning Motability Operations could not guarantee recovery from a verified, untampered backup state during a cyberattack. The challenge intensified with organizational complexity: Motability Operations operated both AWS managed and customer managed accounts across multiple AWS Organizations, making it difficult to enforce consistent backup policies, schedules, and retention rules across their estate. The Financial Conduct Authority’s requirements for secure, auditable data retention added regulatory pressure, making it clear that a fragmented, case-by-case approach to backups would not scale.
To transform their backup strategy, Motability Operations built a unified platform using AWS Backup as the foundation: a centralized service designed to deliver ransomware resilience through immutability, isolation, and automated validation. The solution implements a two-tiered vault architecture with logically air-gapped storage, integrated forensic validation done using the APN partner Elastio’s Active Cyber Resilience Platform, and tag-based policy enforcement that automatically extends protection to newly deployed workloads.
This post explores how Motability Operations designed and implemented their ransomware-resilient backup strategy to deliver measurable business outcomes for organizations managing complex multi-account environments.
Why Motability Operations needed a unified backup strategy
Motability Operations’ backup infrastructure assessment revealed three interconnected challenges that required a comprehensive solution rather than incremental fixes.
- Ransomware resilience gaps – The existing architecture provided no mechanism to verify backup integrity or isolate recovery points from production systems. Motability Operations lacked well-defined processes to rapidly provision isolated accounts for recovery testing or identify the last clean backup for restoration. In a ransomware scenario, this could result in delayed recovery or worse, restoring compromised data that would reinfect new infrastructure.
- Operational fragmentation across account boundaries – Motability Operations operated both AWS managed and Motability Operations managed accounts within multiple AWS Organizations. This architectural complexity made it difficult to maintain consistent backup policies, schedules, and retention rules across the estate. Each account required manual configuration, creating operational overhead and increasing the risk of coverage gaps as new workloads were deployed.
- Regulatory compliance requirements – The Financial Conduct Authority and other governing bodies required secure, auditable data retention practices that could demonstrate proper protection of sensitive customer information. Meeting these requirements with fragmented backup infrastructure would require significant manual effort to generate compliance reports and prove data integrity across multiple systems.
These interconnected challenges made it clear that Motability Operations needed a unified, organization-wide backup strategy built on automation, immutability, and centralized governance.
Solution overview
The following diagram illustrates the solution architecture.
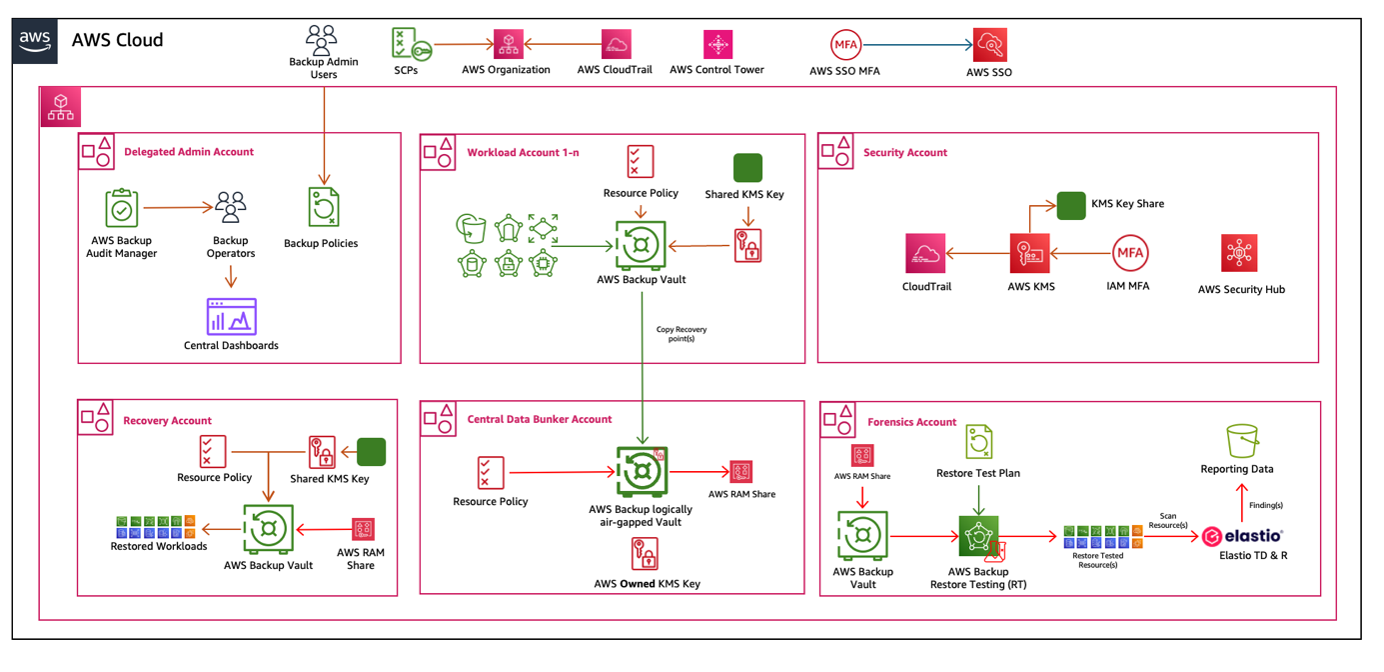
Figure 1: Architecture diagram showing the AWS Backup architecture that Motability Operations employs for each workload.
Following AWS multi-account best practices, workloads run in their own dedicated accounts. This multi-account architecture enables Motability Operations to scale backup protection across workload accounts while using dedicated accounts for key backup functions like centralized storage, forensic scanning, and isolated recovery.
The solution is built on five distinct account types:
- Delegated management account – The platform team defines backup policies centrally in this account, which also hosts a central dashboard to monitor the health of backup and restore jobs. Policies are enforced through mandatory tags assigned to resources, providing consistent protection across workloads.
- Workload accounts – Each workload account stores backups of the workloads running in that account. These are day-to-day operational backups intended for quick restores. Backups are stored in vaults with AWS Backup Vault Lock enabled in governance mode, which means users with sufficient AWS Identity and Access Management (IAM) privileges, such as the management team, can manage these backups as needed.
- Central backup account – Backups from workload accounts are copied into a logically air-gapped vault deployed in this dedicated account. All logically air-gapped vaults have Vault Lock with compliance mode enabled by default, which means backups in the central backup account can’t be deleted or changed by any user, including administrators. This provides tamper-proof storage that remains accessible even if production accounts are compromised. The centralized immutable backup vault maintains separate vaults per platform for organizational clarity.
- Forensic account – This separate account serves to verify backup integrity using Elastio, an APN Partner that provides expert backup verification for ransomware and corruption detection. The logically air-gapped vault in the central backup account is shared to the forensic account using an AWS Resource Access Manager (AWS RAM) resource share. When backup copies complete in the central backup account, Amazon EventBridge triggers AWS Backup restore testing to perform automated restore tests of the data in the forensic account. Elastio then analyzes the restored data, providing proactive threat detection and integrity verification to confirm backups are clean and trustworthy. Elastio scan data is stored in an Amazon S3 bucket, and the forensic account connects to AWS Security Hub in the centralized security account, enabling centralized threat visibility for any threats identified during scanning.
- Recovery account – In the event of an incident, an isolated recovery account is provisioned on demand. The last clean backup is copied from the central backup account to this isolated environment to restore workloads within defined Recovery Time Objectives (RTOs).
Key design principles
Motability Operations’ backup architecture is built on four design principles that guided them to a fortified, ransomware-resilient infrastructure. Operating under these principles (operational flexibility balanced with maximum security, deletion protection through vault locks, automated integrity verification, and strict access isolation) helped Motability Operations build a backup strategy that makes sure backups remain trustworthy and recoverable even under attack.
Two-tiered vault architecture
The solution uses distinct backup vault tiers: one optimized for operational restoration and another dedicated to sustained compliance preservation and isolation. Workloads initially back up into vaults within their workload accounts (Tier 1), providing immediate backup capabilities and quick access for routine restore operations. Multiple workload accounts per platform can all back up into a single Tier 2 logically air-gapped vault in the central backup account, which functions as a more secure backup destination for enhanced isolation and protection. Tier 1 vaults use AWS managed keys for encryption and are locked with Vault Lock in governance mode, so users with sufficient IAM privileges can manage backups as needed. Tier 2 logically air-gapped vaults employ customer managed keys (CMKs) with one CMK per platform and are locked with Vault Lock in compliance mode, providing stronger deletion protection through two modes that each fit their respective tier.
Deletion protection through AWS Backup Vault Lock
AWS Backup Vault Lock serves as an enforcement mechanism, implementing retention policies that prevent deletion of recovery points. This write-once, read-many (WORM) behavior operates in two distinct modes, each designed for its respective tier:
- Governance mode, used in Tier 1 vaults, allows removal or modification with proper permissions for operational flexibility
- Compliance mode, used in Tier 2 vaults, renders vaults indelible after an initial customer-defined grace period
When it’s fully effective, even root users or AWS itself can’t delete protected backups within retention periods, creating air-gapped protection against ransomware attacks that attempt to destroy backup data.
Automated validation and forensic scanning
An event-driven workflow orchestrates the entire backup ecosystem to verify integrity so backups can be trusted in the event of recovery. EventBridge triggers AWS Lambda functions for successful backup replication, and Amazon CloudWatch provides comprehensive monitoring and retry logging capabilities. Motability Operations uses AWS Backup restore testing to perform automated restore tests of their data in the forensic account. Elastio then validates those recovery points, providing proactive threat detection and integrity assurance. This combined approach (automated restoration plus forensic scanning of recovery points) makes sure backups undergo rigorous integrity validation.
Enhanced security through account segregation
Motability Operations’ architecture isolates centralized backup infrastructure, forensic analysis capabilities, and workload recovery operations into separate AWS accounts. This account structure enables a simple workflow where users only have the access required to complete their tasks. Each account operates with dedicated service roles that enforce least-privilege permissions tailored specifically for backup and restore functions. Access controls follow a zero-trust model where permissions are assigned based on user profiles with no overlap. Workload teams can only access their respective workload and recovery accounts. Backup administrators maintain exclusive access to the central backup account. This makes sure that a breach in one domain can’t cascade across the protection boundary.
“Since we implemented it, we’ve had fast, unambiguous, known-good-state recovery across our complex AWS estate, and the embedded forensics have closed our detection gaps before they turn into incidents,” says Nicholas Rowe, Platform Manager, Motability Operations.
Business impact and outcomes
Motability Operations’ unified backup platform delivered measurable improvements across operational efficiency, security posture, and regulatory compliance. The tag-based policy enforcement reduced manual backup configuration work, making it straightforward to enroll new workloads in the backup platform as they scaled. This automation reduced the operational overhead of managing backups across multiple accounts while providing consistent coverage across their entire AWS implementation.
The two-tiered vault architecture with logically air-gapped storage provided Motability Operations with verified recovery capabilities. The combination of AWS Backup restore testing and Elastio backup integrity verification gave the team confidence that they could identify the last clean backup and restore operations quickly in the event of a ransomware attack.
From a compliance perspective, the centralized dashboard and reporting capabilities simplified audit preparation. The dashboard in the delegated management account gave Motability Operations visibility into backup and restore job health across all of their workload accounts, making it straightforward to generate compliance reports and demonstrate adherence to Financial Conduct Authority requirements for secure data retention.
Conclusion
Motability Operations transformed their backup infrastructure from fragmented, workload-by-workload protection into a unified, ransomware-resilient platform that protects data for 900,000 customers across the UK. By partnering with AWS to design and implement this solution, Motability Operations built an architecture that balances operational flexibility with maximum security, using AWS Backup as the foundation for centralized policy management, logically air-gapped storage, and automated integrity validation.
The platform delivers automated protection for newly deployed workloads, verified recovery capabilities through integrated backup validation with Elastio, and simplified compliance reporting that meets stringent regulatory requirements. Motability Operations’ approach demonstrates how organizations managing complex multi-account environments can achieve comprehensive data protection without sacrificing operational efficiency.
For organizations looking to strengthen their backup strategy, Motability Operations’ implementation provides a practical blueprint. The combination of two-tiered vault architecture, deletion protection, automated validation, and strict account segregation shows that comprehensive data protection requires deliberate architectural choices that make sure backups remain accessible, verified, and recoverable even when production systems are compromised.