AWS Security Blog
How to import AWS Config rules evaluations as findings in Security Hub
August 10, 2022: The content in this blog post is no longer up-to-date. AWS Security Hub now automatically receives AWS Config managed and custom rule evaluation results as security findings. Please see the feature announcement and the documentation for more details. You no longer need the custom solution described in this blog post to import AWS Config rules evaluations as findings in Security Hub.
In June at re:Inforce 2019, AWS announced the general availability of AWS Security Hub, a security service that enables customers to centrally view and manage compliance checks and security findings across their AWS accounts. AWS Security Hub imports security findings from AWS Guard Duty, Amazon Inspector, Amazon Macie, and over 30 AWS partner security solutions.
By default, when Security Hub is enabled, it deploys the CIS AWS Foundations standard in your account. CIS AWS Foundations are a set of security configuration best practices for hardening AWS accounts. In order for Security Hub to successfully run compliance checks against the rules included in the CIS AWS Foundations standard, AWS Config must be enabled in the same account where you enabled AWS Security Hub.
If you had previously created your own AWS Config rules before enabling AWS Security Hub, you will need to import them into AWS Security Hub. This will enable your security teams to have all compliance findings across accounts show up in Security Hub, along with the security findings from services like AWS Guard Duty, Amazon Inspector and Amazon Macie. In this post, we’ll show you how to set this up.
Solution Overview
You’ll use an AWS CloudFormation template to deploy the following components, so that you can import the findings of AWS Config rules into AWS Security Hub. Below are the main resources created by this template:
- An AWS Lambda function with the necessary IAM role and IAM policies:
Config-SecHub-Lambda
This Lambda function will execute immediately after the CloudFormation stack creation. It will parse and import AWS Config Rule findings into Security Hub.
- A CloudWatch Event rule with the necessary permission to invoke the AWS Lambda function:
Config-Sechub-CW-Rule
This CloudWatch Event rule will match the compliance change event from AWS Config and will route it to the Lambda function for processing.
Here’s the high level setup of the AWS services that will be created from the CloudFormation stack deployment:
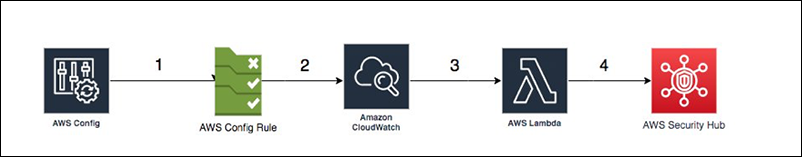
Figure 1: Architecture diagram
- A new AWS Config rule is deployed in the account after you enable AWS Security Hub.
- The AWS Config rule reacts to resource configuration and compliance changes and send these change items to AWS CloudWatch.
- When AWS CloudWatch receives the compliance change, a CloudWatch event rule triggers the AWS Lambda function.
- The Lambda function parses the event received from CloudWatch and imports it into Security Hub as a finding.
Deploy the solution
- Log in to the AWS Management Console and select the us-east-1 Region (N.Virginia) for this sample deployment.
- Make sure that AWS Config and AWS Security Hub are enabled in the region where you want to deploy the template.
- Set up the sample deployment by selecting the Launch Stack button below.
The solution must be launched in the region where AWS Config and AWS Security Hub are enabled, and can be deployed in any region that support the resources that will be created.
Follow these steps to execute the stack:
- Leave the default location for the template and select Next.
- On the Specify stack details page, add your preferred stack name.
- On the Configure Stack options page, select the Next button.
- On the Review page, select the check box, the select the Create Stack button.
- Stack creation will take between 5 – 10 minutes. After the stack is created successfully, select the Resources tab to see the deployed resources.
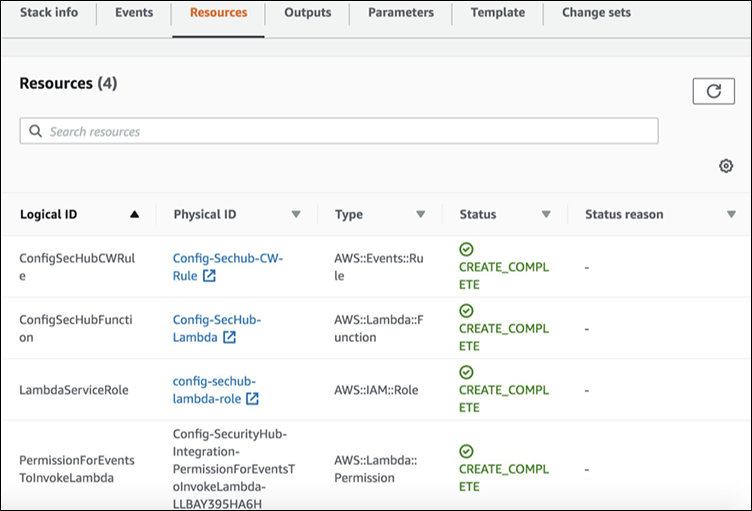
Figure 2: Select the Resources tab to see deployed resources
At this point, you’ve successfully created the following resources:
- A Lambda function that will integrate AWS Config and Security Hub.
- A Lambda execution role used by the Lambda function to call other services.
- A CloudWatch Events rule that will trigger the Lambda function based on AWS Config compliance change events.
- A service permission to allow Amazon CloudWatch to invoke the Lambda function.
Verify the solution
To be certain that everything is set up properly, look at the Lambda code that integrates AWS Config with AWS Security Hub by following the steps below from the console:
- Navigate to the AWS Lambda console.
- From the list of Lambda functions, open the function with the name Config-SecHub-Lambda to check that the function has been deployed successfully.

Figure 3: Config-SecHub-Lambda
You can also verify that the CloudWatch Event rule has deployed successfully:
- Go to the Amazon CloudWatch service console.
- Under Events, select Rules. You should see a rule with the name Config-Sechub-CW-Rule.

Figure 4: Config-Sechub-CW-Rule
Test the solution
- Go to the AWS Config console.
- On the left, select Rules, then Add rule.
- In the search filter, enter ec2 as an input, then select the desired-instance-type rule to test.

Figure 5: AWS Config “add rule” page
- In the rule parameters, enter t2.micro as the value. Any other instance type launched in this account will violate this rule and be noncompliant. Then, select Save.
- Navigate to Amazon EC2 console, and under Create Instance, select Launch.
- Select any Amazon Linux AMI.

Figure 6: Select an Amazon Linux AMI
- To test the rule, select any instance type except t2.micro. In our example, we’ve selected t2.nano.

Figure 7: Choose your instance type
- Because you’re just testing the rule, select Review and Launch. Then choose Proceed without a key pair, check the “I acknowledge…” box, and select Launch Instances.

Figure 8: Select “Launch Instances”
You’ll need to wait few minutes until the instance is launched. You can check the EC2 console to view the instance status.
- Once the instance has launched, go back to the AWS Config console, and from the left-hand menu, select Rules again.
- On the Rules page, select the Noncompliant filter from the drop-down menu to view the rule you’ve created to check instance types.

Figure 9: Select the “Noncompliant” filter on the AWS Config Rules page
- Under Rule name, look for your desired-instance-type rule. It will be followed by your number of noncompliant resources. In this case, there should only be 1 noncompliant resource that matches the EC2 instance you launched above. You can select the rule name to view more details about the noncompliant resource.

Figure 10: Look for the desired-instance-type rule
- Go to the AWS Security Hub console. On the left, select Findings.
- Select the search filter, and from the drop-down menu select Title as the filter, then desired-instance-type as the value. Then select Apply.

Figure 11: Filter by title
- You should now see your AWS Config rule under Findings in AWS Security Hub.

Figure 12: Look for your Config rule under “Findings”
- After you’ve verified that the Lambda function is working, terminate the EC2 instance and delete the Config rule.
What’s happening in the background?
When you deploy the CloudFormation stack, a Lambda function is created along with other resources. This function integrates AWS Config with AWS Security Hub. Every time a new config rule is added, and as soon its compliance status is changed, the AWS CloudWatch Event rule will trigger the Lambda function based on the compliance event. Through this function, the CloudWatch Event is parsed to get the required data for ingestion, then the data is mapped and converted into AWS Security Finding format. After this, the BatchImportFindings API operation is used to import the findings into AWS Security Hub. You can also find the CloudFormation template and the code files in the linked GitHub repository.
Conclusion
In this blog post, we’ve shown you how to import an AWS Config rule to AWS Security Hub, so that your AWS Config rules show up alongside your other security findings. This allows you to more easily use AWS Config rules in your journey toward continuous compliance across your estate of AWS accounts. If you need help in planning, building or optimizing your infrastructure, please reach out to AWS Professional Services. If you have questions about this post, let us know in the Comments section below, or start a new thread on the AWS Security Hub forum.