AWS Storage Blog
Monitor, review, and protect Amazon S3 buckets using Access Analyzer for S3
At AWS, Security is more than just features – it’s a mindset. Today, we announced Access Analyzer for S3, a new feature that monitors your resource policies so you don’t have to. By default, all buckets and objects created in S3 are private. AWS enables you with mechanisms like Access Control Lists (ACLs) and Bucket Policies that you can use to configure granular levels of access. Access Analyzer for S3 is a new feature that monitors your access policies, ensuring that the policies provide only the intended access to your S3 resources. Access Analyzer for S3 evaluates your bucket access policies and enables you to discover and swiftly remediate buckets with potentially unintended access.
As your organization and workloads grow, Access Analyzer for S3 will evaluate all of your policies to alert you to buckets that are shared outside of your AWS account and are at risk of unintended access. In this post we will walk-through how to enable Access Analyzer for Amazon S3, and discuss use cases where using this new feature could benefit your organization to ensure access to your S3 buckets is what you intended, and no more.
When reviewing results that show potentially shared access to a bucket, you can Block All Public Access to the bucket with a single click in the S3 Management console, configure more granular permissions if required, or for specific and verified use cases that require public access, such as static website hosting, you can acknowledge and archive the findings on a bucket to record that you intend for the bucket to remain public or shared. You can revisit and modify these bucket configurations at any time. For auditing purposes, Access Analyzer for S3 findings can be downloaded as a CSV report.
Before you get started in the S3 Management Console, visit the IAM console to enable the AWS Identity and Access Management (IAM) Access Analyzer. When you do this, Access Analyzer for S3 will automatically be visible in the S3 Management Console. Access Analyzer for S3 is based on the IAM Access Analyzer that was launched today at re:Invent 2019.
In the S3 AWS Management Console, under Access Analyzer for S3, you will see two sets of buckets – those shared publicly and those shared with other AWS accounts, including AWS accounts external to your organization. Buckets shared publicly can be accessed by anyone on the Internet. You will also receive insights into the source of the shared access – ACL, bucket policy, or even both and the type of the shared access – Read, Write, List, permissions etc. Buckets that require your attention have an Active status. You can swiftly remediate unintended access to buckets in one of three simple ways.
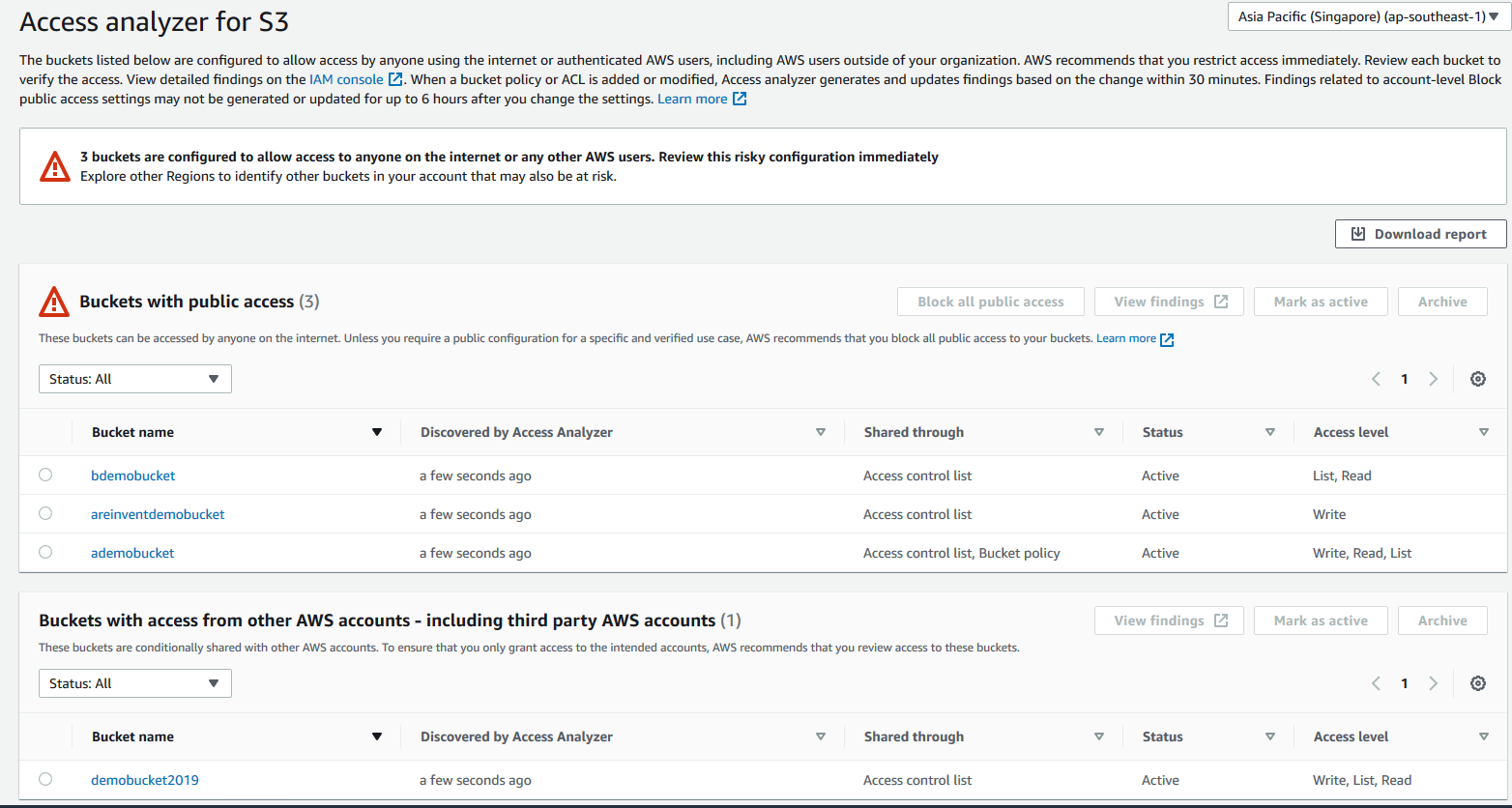
First, you can select a public bucket and select the default Block all public access button in the Access Analyzer for S3 console page. This action will immediately shut public access to the bucket down. We recommend that you block all public access to your buckets.
Next, you can click on the bucket name from within the list, which will deep link you into the permissions page for that bucket within the S3 console. From here, you can inspect the ACL or the policy that is granting public access and make necessary changes to your configurations.
If you have a specific use case that requires public access, for example, static website hosting or cross account sharing of resources, you can archive a bucket finding acknowledging that you intend to keep access the way it is. Buckets with archived findings will still appear in the Access Analyzer for S3 console page, so you always know which buckets are being shared. If your access requirements change, or even if you accidentally archived a finding, you can always revisit these buckets and reconfigure them using the steps described above. You can also download a CSV report from the S3 console to track and audit changes to your storage access over time.
Access Analyzer for S3 is available at no additional cost in the S3 Management Console in all commercial AWS Regions, excluding the AWS China (Beijing) Region and the AWS China (Ningxia) Region. Access Analyzer for S3 is also available through APIs in the AWS GovCloud (US) Regions.
Once enabled, you will begin to see findings and insights about your buckets in the S3 AWS Management Console. Let us know if you have any feedback on Access Analyzer for S3 in the comment, or if you find any different use cases.