AWS Partner Network (APN) Blog
How to Benchmark and Prioritize Security Threats in Amazon GuardDuty Using Sumo Logic
By Bruno Kurtic, Founding VP, Product & Strategy at Sumo Logic
By Sridhar Karnam, Sr. Director of Product Marketing at Sumo Logic
 |
 |
 |
 |
Users looking for enhanced security operations within their Amazon Web Services (AWS) environment can utilize Sumo Logic Global Intelligent Service (GIS) for Amazon GuardDuty.
This solution allows organizations to separate the signal from the noise within your security alerts, helping to more accurately pinpoint investigations and resources.
With Sumo Logic, an AWS Partner Network (APN) Advanced Technology Partner with AWS Competencies in Security, Data & Analytics, and DevOps, customers can compare their environment security data to the aggregate AWS global landscape to understand if a potential attack is targeting them specifically.
This invaluable comparison data allows companies to bolster their security efforts by proactively identifying and remediating threats.
In this post, we will go over how to baseline capability from Sumo Logic for the Amazon GuardDuty security threats, and how the security threat benchmark gives you an insight into what’s normal and what’s an expected behavior.
We’ll explore how to prioritize rare threats and events that analysts often miss, and we’ll look at optimizing the security configurations to follow the industry’s best practices.
Lastly, we’ll see how Sumo Logic customer ThoughtWorks has used the benchmarking to detect rare security threats.
Overview
Sumo Logic Global Intelligent Service (GIS) for Amazon GuardDuty provides customers with a baseline of what’s normal, what’s expected, and ways to dig deeper into the long tail of rare security events that analysts would typically miss.
Sumo Logic GIS for GuardDuty provides real-time insight and actionable intelligence about technology adoption trends, deployment, and architecture. It generates continuous machine learning and statistical baselines for key performance indicators (KPIs) and key risk indicators (KRIs) from Amazon GuardDuty’s threat detection service.
Those baselines are used by Sumo Logic customers to benchmark, prioritize, and optimize security configuration and detection for their AWS accounts.
The Sumo Logic GSI for GuardDuty benchmark application is available on Sumo Logic App Catalog. All Sumo Logic Enterprise License Customers can install this app from their App Catalog within the product.
Architecture
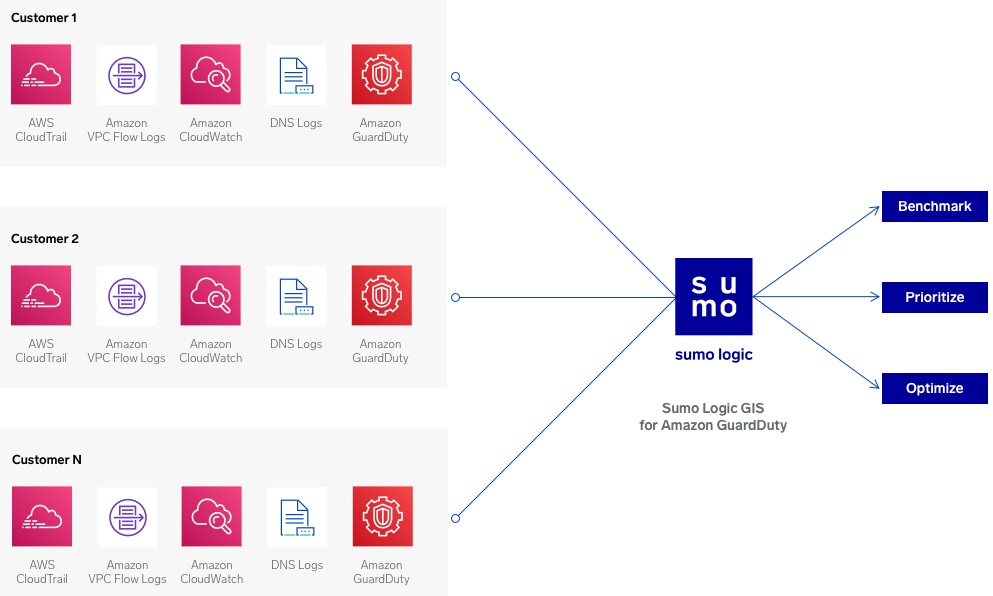
The Benchmark app analyzes baselines to benchmark, prioritize, and optimize security configurations and threat detection analysis for customers’ AWS environments. The rare one-off security events are then prioritized by comparing each of them to the baseline using statistical analysis and machine learning.
Prioritize and take action only on the threats that matter. This help you to improve and optimize your security monitoring, configuration, compliance, and implement best practices across AWS accounts.
Figure 1 – Benchmark app architecture using the Sumo Logic Global Intelligent Service.
AWS has done an amazing job with the monitoring framework in Amazon GuardDuty. The logs and events from Amazon CloudTrail, VPC Flow Logs, and DNS Logs are fed into GuardDuty, which analyzes these events and creates findings. These findings can be sent to CloudWatch and then be processed through AWS Lambda functions, or sent into Sumo Logic for further analysis.
The insight of merging global security intelligence and your local data allows you to benchmark local security threats against global threats, prioritize rare security events you may otherwise miss, and optimize your security configurations for industry best practices.
Benchmarking Security Threats on AWS
As more and more enterprises migrate their workloads to AWS, they are faced with learning new methodologies and tools to help them secure their cloud environments.
Amazon GuardDuty works hard on your behalf to detect threats, but how do you prioritize where to focus your resolution efforts? How do you figure out what’s normal or expected behavior?
Sumo Logic GIS for GuardDuty finds the signal in the noise by offering a view into what’s happening from a threat perspective in the broader AWS environment. The Global Threat Activity dashboard gives you a view into active threats, their targets, severity from a GuardDuty perspective, and spotlights unusual activity to take a proactive security approach.

Figure 2 – Global threat benchmark dashboard for Amazon GuardDuty.
From there, you can leverage the dashboard view that overlays global activity with your own activity to help you see how these differ.
For instance, if you’re seeing more backdoor activity than the global benchmark indicates, it could mean you’re currently targeted and may want to take proactive defensive posture against those specific types of threats. This helps you prioritize future resource allocation and understand what’s normal.
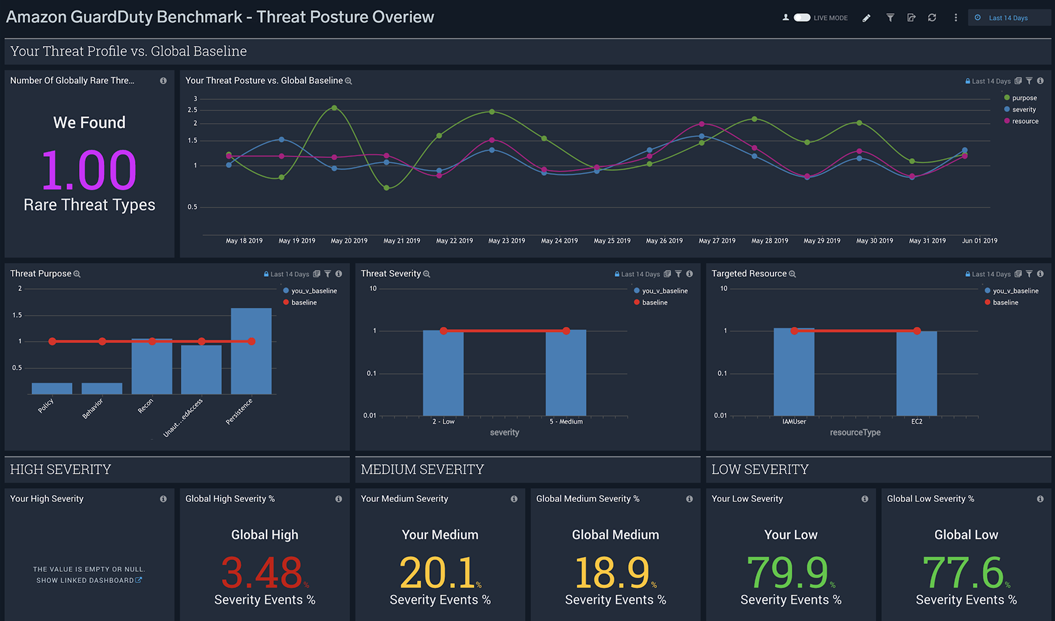
Figure 3 – Threat posture view of baseline against local security data.
Another interesting benchmark is the rare active threat type benchmark. It’s relatively straightforward to figure out the top 10 attacks on your account. However, that classic single-tenant view entirely misses whether what’s happening to you is unique or the normal part of the global landscape.
There are many security issues you can only analyze if you have visibility into global threat activity, which helps you look for those rare threats in your own environment. Sumo Logic GIS for GuardDuty continuously monitors for threats that become active in your account and notifies you via dashboard or alerts.
Prioritizing Rare Events to Investigate
If you determine that threat activity in your account differs in a significant way from the baseline, you can use the threat detail view to isolate those threats to investigate and determine what your exposure is.
The benchmark app compares all active threats in your account to determine significant contributors to the gap. Some of these threats would have gone unnoticed using a classic security information and event management (SIEM) rules engine, or even single-tenant analytics because they’re missing the global context necessary to compare your threats with the global user-base.
Without this lens, many important threats may remain buried under mountains of common findings.
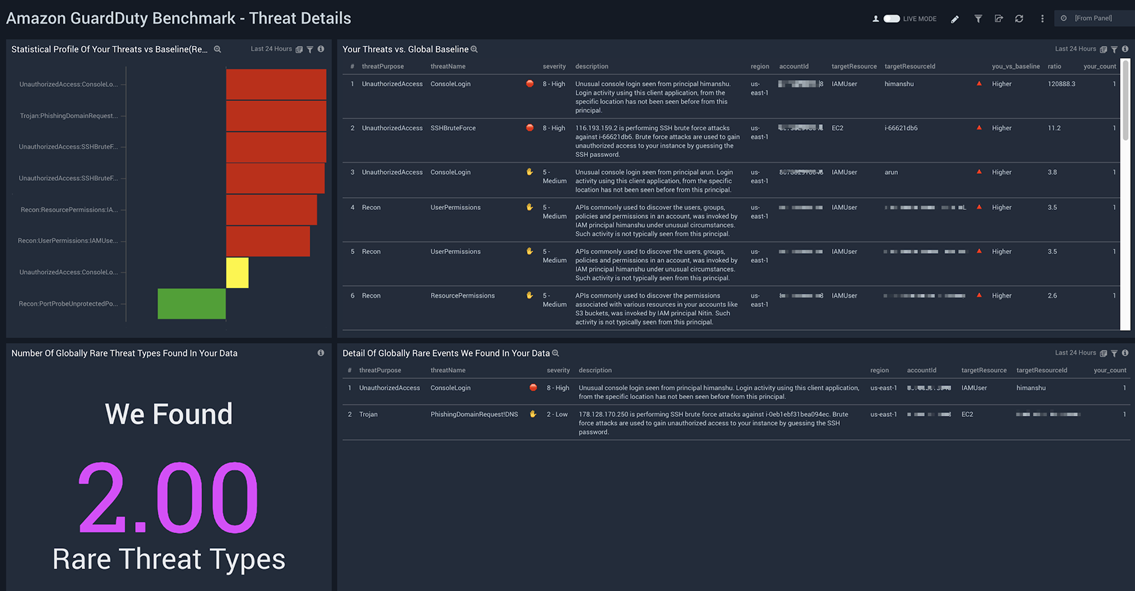
Figure 4 – Threat details of rare security event details.
Another important lens on your security is understanding rare threats that occur in your environment but do not rarely occur anywhere else.
A narrow view often misses the question about whether or not something unique is occurring in your environment. For instance, event such as a “TOR IP caller domain generation algorithm request” occurring in your environment that rarely occurs anywhere else probably warrants an investigation.
Addressing Security Gaps and Misconfigurations
Exposure to specific types of threats may indicate that some aspects of your configuration or security process require improvements.
Using Sumo Logic GIS for GuardDuty helps identify those gaps and enables you to perform root cause analysis to close potential gaps or set up compensating controls. The solution gives you access to all underlying data and benchmark from GuardDuty, but also enables you to correlate that data to other sources such as AWS CloudTrail, Amazon VPC Flow Logs, and other data such as OS logs, containers, or databases.
Sumo Logic also enables you to integrate findings with third-party tools such as ticketing systems, collaboration tools, remediation tools, and more.
You can create alerts that trigger your standard security incident response processes, create incidents inside workflow tools for further investigation, or simply start collaboration with your team to address potential incidents.
Customer Success: ThoughtWorks
ThoughtWorks is a modern application company that has contributed a lot to the open source community around the continuous integration and continuous development (CI/CD) process of the software development life cycle.
Sumo Logic works with ThoughtWorks on the security of their stack, and they have been a preview customer of Sumo Logic’s benchmarking app. The baseline on GuardDuty is used by ThoughtWorks to drill down to the rare events and optimize security configurations to meet or exceed industry best practices.
“As a global consultancy, there are hundreds if not thousands of potential security threats and events that pass through our organization on any given day, making it a challenge to not only track, but prioritize how to handle these events,” says Philip Duldig, senior security analyst at ThoughtWorks.
“As an early adopter of Sumo Logic’s Global Intelligence Service for Amazon GuardDuty, the biggest value we’ve experienced is the ability to get actionable insights to prioritize and benchmark rare or non-frequent security events from our AWS workloads, so we can optimize our security posture. I also love that I can compare global benchmarking data with my local data, to see where we are stacking up.”
Summary
Sumo Logic Global Intelligent Service (GIS) for Amazon GuardDuty increases your security posture and helps you benchmark threat detection with the global AWS landscape.
With Sumo Logic GIS for Guard Duty, organizations can utilize machine learning and automatic baselines to create a proactive security operations hub at your organization.
If you’re already an Amazon GuardDuty and Sumo Logic customer, simply go to the Sumo Logic App Catalog and install the app Amazon GuardDuty Benchmark.
New customers can sign up for a free trial, send your GuardDuty findings, and deploy the Benchmark app on your management console.
For more security and DevSecOps-focused reads, check out the Sumo Logic Blog.
The content and opinions in this blog are those of the third party author and AWS is not responsible for the content or accuracy of this post.
.
 |
 |
Sumo Logic – APN Partner Spotlight
Sumo Logic is an AWS Competency Partner. Its cloud-based machine data analytics service helps customers gain instant insights into their growing and complex pool of machine data.
Contact Sumo Logic | Solution Overview | Buy on Marketplace
*Already worked with Sumo Logic? Rate this Partner
*To review an APN Partner, you must be an AWS customer that has worked with them directly on a project.