AWS News Blog
New – Use AWS PrivateLink to Access AWS Lambda Over Private AWS Network
|
|
AWS Lambda is a serverless computing service that lets you run code without provisioning or managing servers. You simply upload your code and Lambda does all the work to execute and scale your code for high availability. Many AWS customers today use this serverless computing platform to significantly improve their productivity while developing and operating applications.
Today, I am happy to announce that AWS Lambda now supports AWS PrivateLink which lets you create, manage, and invoke Lambda functions securely from inside your virtual private cloud (VPC) or on-premises data centers without exposing traffic to the public Internet.
Until now, in order to call Lambda functions, a VPC required an Internet Gateway, network address translation (NAT) gateway, and/or public IP address. With this update, PrivateLink routes the call through the AWS private network, eliminating the need for Internet access. Additionally, you can now call the Lambda API directly from your on-premises data centers by connecting to a VPC using AWS Direct Connect or AWS VPN Connections.
Some customers have wanted to manage and call Lambda functions from a VPC that doesn’t have internet access due to internal IT governance requirements. With this update, you will now be able to use Lambda without going through the public internet. Also, customers who have maintained a NAT gateway to access Lambda from a VPC can use a VPC endpoint instead of incurring the cost of the NAT gateway. Security is further improved because you no longer need to allow Internet access to your VPC to call Lambda functions, and network architecture becomes more simple and easily manageable.
How to Get Started With AWS PrivateLink
AWS PrivateLink uses an elastic network interface called the “Interface VPC endpoint” to act as an entry point for traffic targeting AWS services. Interface endpoints limit all network traffic to AWS internal network and provide secure access to your services. The Interface VPC endpoint is a redundant, highly available VPC component that has a private IP address and is scaled horizontally.
Getting Started Using the AWS Management Console
To get started, you can use the AWS Management Console, AWS CLI, or AWS CloudFormation. In this first example, I’ll show the Management Console.
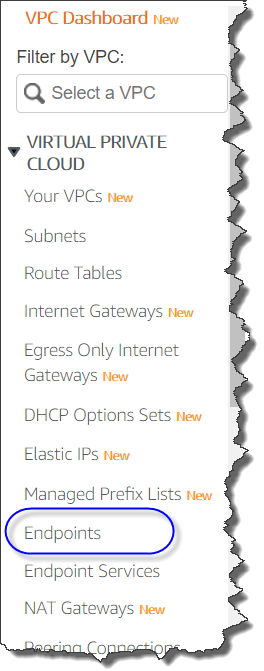
First, you access the VPC management console, and click “Endpoints.”
Click “Create Endpoint” button.
Type “lambda” in the search bar, and you’ll see Service Name. Select it, and choose the VPC where you want to create the interface endpoint.
After that, you are prompted to specify subnets where you may want to create endpoints.
If you want, you can set your own DNS name to the endpoint with Amazon Route53 private hosted zones when you enable “Enable DNS name” option. With this option enabled, any request to Lambda from your public subnet does not go through the Internet Gateway. All requests to Lambda go through the VPC endpoints.
Next, specify “Security Group” for protocols, port, and source/target IP address control.
Then, set the policy to control who has access to the VPC endpoint. By default, “Full Access” is selected, but we always recommend you first grant access only to the minimum necessary principal; you can modify this later.
Following is a sample policy you can customize. With this sample, only the IAM user “MyUser” can update and invoke the Lambda function “my-function”.
{
"Statement": [
{
"Principal": "arn:aws:iam::123412341234:user/MyUser",
"Action": [
"lambda:InvokeFunction"
"lambda:UpdateFunctionCode",
"lambda:UpdateFunctionConfiguration"
],
"Effect": "Allow",
"Resource": [
"arn:aws:lambda:us-east-2:123456789012:function:my-function:1”
]
}
]
}
Now, it’s time for the final step. Click the “Create endpoint” button. You’ll see the success dialog shown below.
Now you can create, manage, and invoke Lambda functions through the VPC endpoint. You can also access the VPC endpoint from another VPC connected to the original VPC via VPC peering or AWS Transit Gateway. You can also access the VPC endpoint from another AWS account.
Getting Started Using the AWS Command Line Interface (CLI)
Using AWS CLI is more precise and easy if you already have the AWS CLI environment.
Available Today
AWS PrivateLink support for AWS Lambda is now available in all AWS Regions except for Africa (Cape Town) and Europe (Milan). Support for those regions is on our roadmap and coming soon. Standard AWS PrivateLink pricing applies to Lambda interface endpoints. You will be billed each hour the interface endpoint is provisioned in each Availability Zone, and for the data processed through the interface endpoint. There is no change to AWS Lambda pricing for using through VPC endpoints.
See AWS PrivateLink for more information, including pricing and documentation.
– Kame;