AWS Compute Blog
Category: Database
Managing sessions of anonymous users in WebSocket API-based applications
In this post, you learn how to keep track of user sessions when using WebSockets API and not lose the session context when the user reconnects again. Apply learnings from this example to improve your user experience when using WebSocket APIs for web-frontend and mobile applications, where internet connections may be unstable.
Introducing AWS Lambda Powertools for .NET
CloudWatch and AWS X-Ray offer functionality that provides comprehensive observability for your applications. Lambda Powertools .NET is now generally available. The library helps implement observability when running Lambda functions based on .NET 6 while reducing the amount of custom code.
Implementing reactive progress tracking for AWS Step Functions
This blog post is written by Alexey Paramonov, Solutions Architect, ISV and Maximilian Schellhorn, Solutions Architect ISV This blog post demonstrates a solution based on AWS Step Functions and Amazon API Gateway WebSockets to track execution progress of a long running workflow. The solution updates the frontend regularly and users are able to track the […]
Enabling load-balancing of non-HTTP(s) traffic on AWS Wavelength
This blog post is written by Jack Chen, Telco Solutions Architect, and Robert Belson, Developer Advocate. AWS Wavelength embeds AWS compute and storage services within 5G networks, providing mobile edge computing infrastructure for developing, deploying, and scaling ultra-low-latency applications. AWS recently introduced support for Application Load Balancer (ALB) in AWS Wavelength zones. Although ALB addresses […]
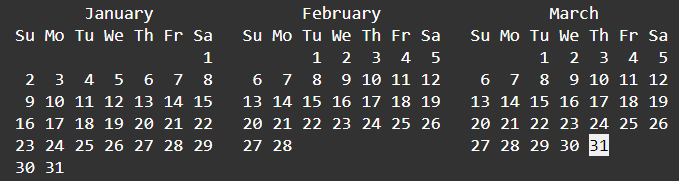
ICYMI: Serverless Q3 2022
Welcome to the 19th edition of the AWS Serverless ICYMI (in case you missed it) quarterly recap. Every quarter, we share all the most recent product launches, feature enhancements, blog posts, webinars, Twitch live streams, and other interesting things that you might have missed! In case you missed our last ICYMI, check out what happened […]
Introducing Amazon CodeWhisperer in the AWS Lambda console (In preview)
This blog post is written by Mark Richman, Senior Solutions Architect. Today, AWS is launching a new capability to integrate the Amazon CodeWhisperer experience with the AWS Lambda console code editor. Amazon CodeWhisperer is a machine learning (ML)–powered service that helps improve developer productivity. It generates code recommendations based on their code comments written in […]
ICYMI: Serverless Q1 2022
Welcome to the 17th edition of the AWS Serverless ICYMI (in case you missed it) quarterly recap. Every quarter, we share all the most recent product launches, feature enhancements, blog posts, webinars, Twitch live streams, and other interesting things that you might have missed! In case you missed our last ICYMI, check out what happened […]
Using AWS Step Functions and Amazon DynamoDB for business rules orchestration
In this post, you learned how to leverage an orchestration framework using Step Functions, Lambda, DynamoDB, and API Gateway to build an API backed by an open-source Drools rules engine, running on a container. Try this solution for your cloud native business rules orchestration use-case.
Choosing the right solution for AWS Lambda external parameters
This post is written by Thomas Moore, Solutions Architect, Serverless. When using AWS Lambda to build serverless applications, customers often need to retrieve parameters from an external source at runtime. This allows you to share parameter values across multiple functions or microservices, providing a single source of truth for updates. A common example is retrieving […]
Using the circuit breaker pattern with AWS Step Functions and Amazon DynamoDB
This post is written by Anitha Deenadayalan, Developer Specialist SA, DevAx Modern applications use microservices as an architectural and organizational approach to software development, where the application comprises small independent services that communicate over well-defined APIs. When multiple microservices collaborate to handle requests, one or more services may become unavailable or exhibit a high latency. […]