AWS Compute Blog
Choosing the right solution for AWS Lambda external parameters
This post is written by Thomas Moore, Solutions Architect, Serverless.
When using AWS Lambda to build serverless applications, customers often need to retrieve parameters from an external source at runtime. This allows you to share parameter values across multiple functions or microservices, providing a single source of truth for updates. A common example is retrieving database connection details from an external source and then using the retrieved hostname, user name, and password to connect to the database:
AWS provides a number of options to store parameter data, including AWS Systems Manager Parameter Store, AWS AppConfig, Amazon S3, and Lambda environment variables. This blog explores the different parameter data that you may need to store. I cover considerations for choosing the right parameter solution and how to retrieve and cache parameter data efficiently within the Lambda function execution environment.
Common use cases
Common parameter examples include:
- Securely storing secret data, such as credentials or API keys.
- Database connection details such as hostname, port, and credentials.
- Schema data (for example, a structured JSON response).
- TLS certificate for mTLS or JWT validation.
- Email template.
- Tenant configuration in a multitenant system.
- Details of external AWS resources to communicate with such as an Amazon SQS queue URL, Amazon EventBridge event bus name, or AWS Step Functions ARN.
Key considerations
There are a number of key considerations when choosing the right solution for external parameter data.
- Cost – how much does it cost to store the data and retrieve it via an API call?
- Security – what encryption and fine-grained access control is required?
- Performance – what are the retrieval latency requirements?
- Data size – how much data is there to store and retrieve?
- Update frequency – how often does the parameter change and how does the function handle stale parameters?
- Access scope – do multiple functions or services access the parameter?
These considerations help to determine where to store the parameter data and how often to retrieve it.
For example, a 4KB parameter that updates hourly and is used by hundreds of functions needs to be optimized for low retrieval costs and high performance. Choosing a solution that supports low-cost API GET requests at a high transaction per second (TPS) would be better than one that supports large data.
AWS service options
There are a number of AWS services available to store external parameter data.
Amazon S3
S3 is an object storage service offering 99.999999999% (11 9s) of data durability and virtually unlimited scalability at low cost. Objects can be up to 5 TB in size in any format, making S3 a good solution to store larger parameter data.
Amazon DynamoDB
Amazon DynamoDB is a fully managed, serverless, key-value NoSQL database designed for single-digit millisecond performance at any scale. Due to the high performance of this service, it’s a great place to store parameters when low retrieval latency is important.
AWS Secrets Manager
AWS Secrets Manager makes it easier to rotate, manage, and retrieve secret data. This makes it the ideal place to store sensitive parameters such as passwords and API keys.
AWS Systems Manager Parameter Store
Parameter Store provides a centralized store to manage configuration data. This data can be plaintext or encrypted using AWS Key Management Service (KMS). Parameters can be tagged and organized into hierarchies for simpler management. Parameter Store is a good default choice for general-purpose parameters in AWS. The standard version (no additional charge) can store parameters up to 4 KB in size and the advanced version (additional charges apply) up to 8 KB.
For a code example using Parameter Store for Lambda parameters, see the Serverless Land pattern.
AWS AppConfig
AppConfig is a capability of AWS Systems Manager to create, manage, and quickly deploy application configurations. AppConfig allows you to validate changes during roll-outs and automatically roll back, if there is an error. AppConfig deployment strategies help to manage configuration changes safely.
AppConfig also provides a Lambda extension to retrieve and locally cache configuration data. This results in fewer API calls and reduced function duration, reducing costs.
AWS Lambda environment variables
You can store parameter data as Lambda environment variables as part of the function’s version-specific configuration. Lambda environment variables are stored during function creation or updates. You can access these variables directly from your code without needing to contact an external source. Environment variables are ideal for parameter values that don’t need updating regularly and help make function code reusable across different environments. However, unlike the other options, values cannot be accessed centrally by multiple functions or services.
Lambda execution lifecycle
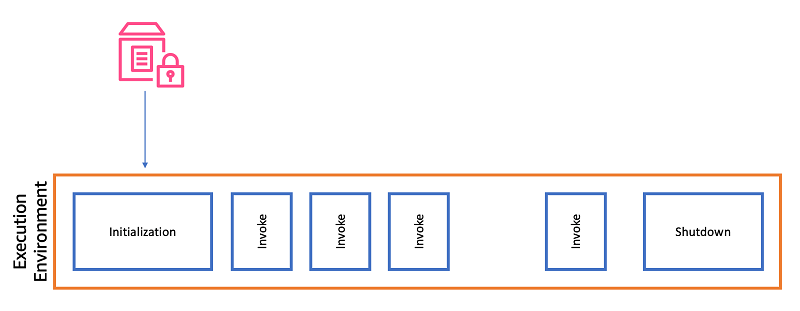
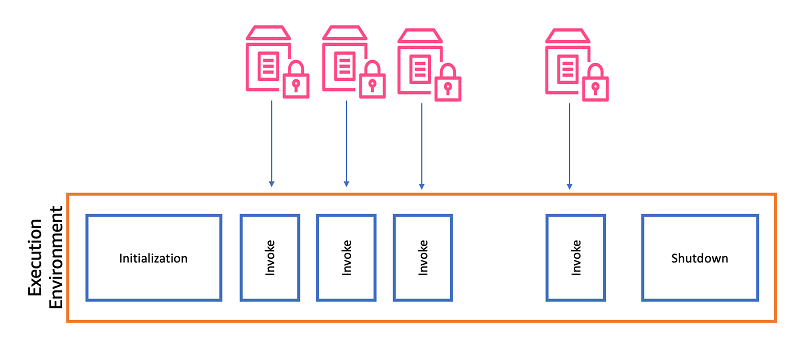
It is worth understanding the Lambda execution lifecycle, which has a number of stages. This helps to decide when to handle parameter retrieval within your Lambda code, including cache management.
When a Lambda function is invoked for the first time, or when Lambda is scaling to handle additional requests, an execution environment is created. The first phase in the execution environment’s lifecycle is initialization (Init), during which the code outside the main handler function runs. This is known as a cold start.
The execution environment can then be re-used for subsequent invocations. This means that the Init phase does not need to run again and only the main handler function code runs. This is known as a warm start.
An execution environment can only run a single invocation at a time. Concurrent invocations require additional execution environments. When a new execution environment is required, this starts a new Init phase, which runs the cold start process.
Caching and updates
Retrieving the parameter during Init
As Lambda execution environments are re-used, you can improve the performance and reduce the cost of retrieving an external parameter by caching the value. Writing the value to memory or the Lambda /tmp file system allows it to be available during subsequent invokes in the same execution environment.
This approach reduces API calls, as they are not made during every invocation. However, this can cause an out-of-date parameter and potentially different values across concurrent execution environments.
The following Python example shows how to retrieve a Parameter Store value outside the Lambda handler function during the Init phase.
import boto3
ssm = boto3.client('ssm', region_name='eu-west-1')
parameter = ssm.get_parameter(Name='/my/parameter')
def lambda_handler(event, context):
# My function code...Retrieving the parameter on every invocation
Another option is to retrieve the parameter during every invocation by making the API call inside the handler code. This keeps the value up to date, but can lead to higher retrieval costs and longer function durations due to the added API call during every invocation.
The following Python example shows this approach:
import boto3
ssm = boto3.client('ssm', region_name='eu-west-1')
def lambda_handler(event, context):
parameter = ssm.get_parameter(Name='/my/parameter')
# My function code...Using AWS AppConfig Lambda extension
AppConfig allows you to retrieve and cache values from the service using a Lambda extension. The extension retrieves the values and makes them available via a local HTTP server. The Lambda function then queries the local HTTP server for the value. The AppConfig extension refreshes the values at a configurable poll interval, which defaults to 45 seconds. This improves performance and reduces costs, as the function only needs to make a local HTTP call.
The following Python code example shows how to access the cached parameters.
import urllib.request
def lambda_handler(event, context):
url = f'http://localhost:2772/applications/application_name/environments/environment_name/configurations/configuration_name'
config = urllib.request.urlopen(url).read()
# My function code...For caching secret values using a Lambda extension local HTTP cache and AWS Secrets Manager, see the AWS Prescriptive Guidance documentation.
Using Lambda Powertools for Python or Java
Lambda Powertools for Python or Lambda Powertools for Java contains utilities to manage parameter caching. You can configure the cache interval, which defaults to 5 seconds. Supported parameter stores include Secrets Manager, AWS Systems Manager Parameter Store, AppConfig, and DynamoDB. You also have the option to bring your own provider. The following example shows the Powertools for Python parameters utility retrieving a single value from Systems Manager Parameter Store.
from aws_lambda_powertools.utilities import parameters
def handler(event, context):
value = parameters.get_parameter("/my/parameter")
# My function code…Security
Parameter security is a key consideration. You should evaluate encryption at rest, in-transit, private network access, and fine-grained permissions for each external parameter solution based on the use case.
All services highlighted in this post support server-side encryption at rest, and you can choose to use AWS KMS to manage your own keys. When accessing parameters using the AWS SDK and CLI tools, connections are encrypted in transit using TLS by default. You can force most to use TLS 1.2.
To access parameters from inside an Amazon Virtual Private Cloud (Amazon VPC) without internet access, you can use AWS PrivateLink and create a VPC endpoint for each service. All the services mentioned in this post support AWS PrivateLink connections.
Use AWS Identity and Access Management (IAM) policies to manage which users or roles can access specific parameters.
General guidance
This blog explores a number of considerations to make when using an external source for Lambda parameters. The correct solution is use-case dependent. There are some general guidelines when selecting an AWS service.
- For general-purpose low-cost parameters, use AWS Systems Manager Parameter Store.
- For single function, small parameters, use Lambda environment variables.
- For secret values that require automatic rotation, use AWS Secrets Manager.
- When you need a managed cache, use the AWS AppConfig Lambda extension or Lambda Powertools for Python/Java.
- For items larger than 400 KB, use Amazon S3.
- When access frequency is high, and low latency is required, use Amazon DynamoDB.
Conclusion
External parameters provide a central source of truth across distributed systems, allowing for efficient updates and code reuse. This blog post highlights a number of considerations when using external parameters with Lambda to help you choose the most appropriate solution for your use case.
Consider how you cache and reuse parameters inside the Lambda execution environment. Doing this correctly can help you reduce costs and improve the performance of your Lambda functions.
There are a number of services to choose from to store parameter data. These include DynamoDB, S3, Parameter Store, Secrets Manager, AppConfig, and Lambda environment variables. Each comes with a number of advantages, depending on the use case. This blog guidance, along with the AWS documentation and Service Quotas, can help you select the most appropriate service for your workload.
For more serverless learning resources, visit Serverless Land.