AWS Security Blog
Category: Compute
Best Practices to help secure your container image build pipeline by using AWS Signer
AWS Signer is a fully managed code-signing service to help ensure the trust and integrity of your code. It helps you verify that the code comes from a trusted source and that an unauthorized party has not accessed it. AWS Signer manages code signing certificates and public and private keys, which can reduce the overhead […]
How to create an AMI hardening pipeline and automate updates to your ECS instance fleet
Amazon Elastic Container Service (Amazon ECS) is a comprehensive managed container orchestrator that simplifies the deployment, maintenance, and scalability of container-based applications. With Amazon ECS, you can deploy your containerized application as a standalone task, or run a task as part of a service in your cluster. The Amazon ECS infrastructure for tasks includes Amazon […]
Security considerations for running containers on Amazon ECS
January 11, 2024: We’ve updated this post to include information about Amazon GuardDuty Runtime Monitoring for Amazon ECS clusters. If you’re looking to enhance the security of your containers on Amazon Elastic Container Service (Amazon ECS), you can begin with the six tips that we’ll cover in this blog post. These curated best practices are […]
Automate the deployment of an NGINX web service using Amazon ECS with TLS offload in CloudHSM
Customers who require private keys for their TLS certificates to be stored in FIPS 140-2 Level 3 certified hardware security modules (HSMs) can use AWS CloudHSM to store their keys for websites hosted in the cloud. In this blog post, we will show you how to automate the deployment of a web application using NGINX […]
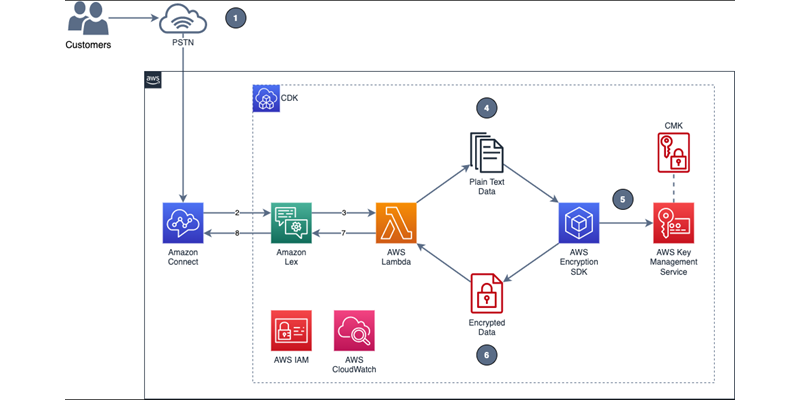
How to encrypt sensitive caller voice input in Amazon Lex
In the telecommunications industry, sensitive authentication and user data are typically received through mobile voice and keypads, and companies are responsible for protecting the data obtained through these channels. The increasing use of voice-driven interactive voice response (IVR) has resulted in a need to provide solutions that can protect user data that is gathered from […]
Introducing the Security Design of the AWS Nitro System whitepaper
AWS recently released a whitepaper on the Security Design of the AWS Nitro System. The Nitro System is a combination of purpose-built server designs, data processors, system management components, and specialized firmware that serves as the underlying virtualization technology that powers all Amazon Elastic Compute Cloud (Amazon EC2) instances launched since early 2018. With the […]
Use Amazon Inspector to manage your build and deploy pipelines for containerized applications
Amazon Inspector is an automated vulnerability management service that continually scans Amazon Web Services (AWS) workloads for software vulnerabilities and unintended network exposure. Amazon Inspector currently supports vulnerability reporting for Amazon Elastic Compute Cloud (Amazon EC2) instances and container images stored in Amazon Elastic Container Registry (Amazon ECR). With the emergence of Docker in 2013, […]
How to use new Amazon GuardDuty EKS Protection findings
If you run container workloads that use Amazon Elastic Kubernetes Service (Amazon EKS), Amazon GuardDuty now has added support that will help you better protect these workloads from potential threats. Amazon GuardDuty EKS Protection can help detect threats related to user and application activity that is captured in Kubernetes audit logs. Newly-added Kubernetes threat detections […]
Hardening the security of your AWS Elastic Beanstalk Application the Well-Architected way
April 7, 2022: This post has been updated with sample Elastic Beanstalk application with hardened security configurations on GitHub. Launching an application in AWS Elastic Beanstalk is straightforward. You define a name for your application, select the platform you want to run it on (for example, Ruby), and upload the source code. The default Elastic Beanstalk configuration […]
How to enable secure seamless single sign-on to Amazon EC2 Windows instances with AWS IAM Identity Center
September 23, 2022: This blog post has been updated with correction on sample custom permissions policy download URL. September 12, 2022: This blog post has been updated to reflect the new name of AWS Single Sign-On (SSO) – AWS IAM Identity Center. Read more about the name change here. Today, we’re launching new functionality that […]