AWS Partner Network (APN) Blog
Simplifying Network Connectivity with VMware Cloud on AWS and AWS Direct Connect
 By Aarthi Raju, Partner Solutions Architect at AWS
By Aarthi Raju, Partner Solutions Architect at AWS
By Haider Witwit, Sr. Solutions Architect – VMware at AWS
Connectivity to VMware Cloud on AWS has gone through multiple iterations. We started with connecting to the software-defined data center (SDDC) cluster using virtual private network (VPN) connections, then enabled support for AWS Direct Connect using Private VIF for vMotion and management traffic. We also supported AWS Direct Connect Public VIF with VPN.
While this works, we learned from Amazon Web Services (AWS) customers that they wanted a simplified network connectivity model.
That’s why we recently launched support for full connectivity using AWS Direct Connect. Prior to this, customers who wished to connect to their SDDC and migrate workloads required the below connectivity model:
- L3 connectivity between source and destination vMotion and host management networks. This requires Private VIF between on-premises and the SDDC VPC. The Private VIF will enable L3 connectivity between the SDDC underlay and related on-premises networks.
. - L3 connectivity between source and destination vCenter Servers. Since the SDDC vCenter Server operates on the overlay network, it needs L3 VPN between the management gateway (MGW) and edge router of the on-premises vCenter Server network. This tunnel can be established over an AWS backbone using Public VIF or Internet connection.
.
With Public VIF, the MGW public address will be included in the AWS prefixes customers receive on their on-premises edge router. We recommend you use a firewall filter to limit accepted prefixes to only targeted endpoints and ports when possible. In this case, the two public addresses of the MGW and customer gateway (CGW) only.
We wanted to simplify this for our customers because you wanted to get a dedicated network connection with consistent throughput and not manage VPN connections. We worked with VMware, an AWS Partner Network (APN) Advanced Technology Partner, to build features that allow customers to use their existing AWS Direct Connect or new connections to provide a dedicated network performance.
Customers can use their existing AWS Direct Connect connection and just pay for the data egress charges. In this post, we’ll detail how customers can use AWS Direct Connect Private VIF to connect to their SDDC clusters eliminating the need for Public VIF or VPN connections.
What is AWS Direct Connect?
AWS Direct Connect is a cloud service solution that makes it easy to establish a dedicated network connection from your premises to AWS. Using AWS Direct Connect, you can establish private connectivity between AWS and your data center, office, or co-location environment, which in many cases can reduce your network costs, increase bandwidth throughput, and provide a more consistent network experience than Internet-based connections.
AWS Direct Connect lets you establish a dedicated network connection between your network and one of the AWS Direct Connect locations. Using industry-standard 802.1q VLANs, this dedicated connection can be partitioned into multiple virtual interfaces.
This allows you to use the same connection to access public resources, such as objects stored in Amazon Simple Storage Service (Amazon S3) using public IP address space, and private resources such as Amazon Elastic Compute Cloud (Amazon EC2) instances running within an Amazon Virtual Private Cloud (VPC) using private IP space, while maintaining network separation between the public and private environments.
Virtual interfaces can be reconfigured at any time to meet your changing needs.
New Connectivity Model
NSX-T uses the “Tier-0” logical router concept as a single point of connectivity between SDDC compute and management networks on one side, with external networks like customer connected VPCs (utilizing the 25G ENA card), other customer VPCs over VPN tunnels, and on-premises networks over Direct Connect or the Internet, on the other side.
Tier-0 router also simplifies connectivity between CGW and MGW since they now run as separate processes in the tier-0 router instead of the two separate VMs in the old NSX-V model.

Figure 1 – Connectivity to VMware SDDC using AWS Direct Connect.
The joint engineering work between AWS and VMware shows results in adding full Direct Connect support for NSX-T. This feature enables default advertisement for SDDC logical networks and management traffic over hosted Direct Connect Private VIF to a customer’s on-premises facility when associated to SDDC, with no need for IPSec tunnels over DX public VIF or the Internet. This model significantly simplifies connectivity requirements for use cases like vMotion with the NSX-T versus NSX-V base clusters.
With this new feature, customers can use a single hosted Private VIF to connect to their SDDC. This Private hosted VIF allows customers to communicate to their workload virtual machines on the overlay networks, and also to the host management and appliance networks.
Hosted Private VIF allows you to create a VIF in another account by only specifying the account number. The destination account will have to accept this VIF in their account.
In our case, customers can create a Hosted Private VIF from their account and enter the VMware Cloud on AWS account number for the VIF. This account number can be obtained from the VMware Cloud on AWS console, under the Direct Connect > VMC AWS Account, as shown in Figure 2.
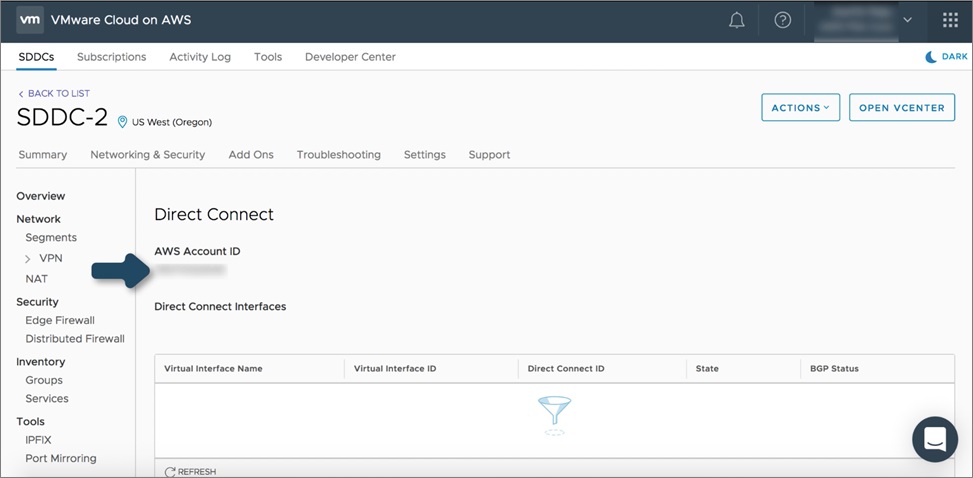
Figure 2 – VMware Cloud on AWS Direct Connect console.
Once a Hosted VIF is created, customers can accept this from their VMware Cloud on AWS console. The VMware SDDC will advertise all their logical networks using this VIF, and customers can advertise their on-premises networks to the SDDC as well. This allows a simplified full connectivity option for customers while taking advantage of the 1G or 10G bandwidth connections form Direct Connect.
You can see the routes advertised from the VMware Cloud SDDC to your on-premises from the Advertised BGP Routes section on the console, and the routes received from their on-premises on the Learned BGP Routes section, as shown in Figure 3. The maximum number of logical network routes that can be advertised from the VMware Cloud SDDC to on-premises is 16 and can be increased by VMware upon evaluation.
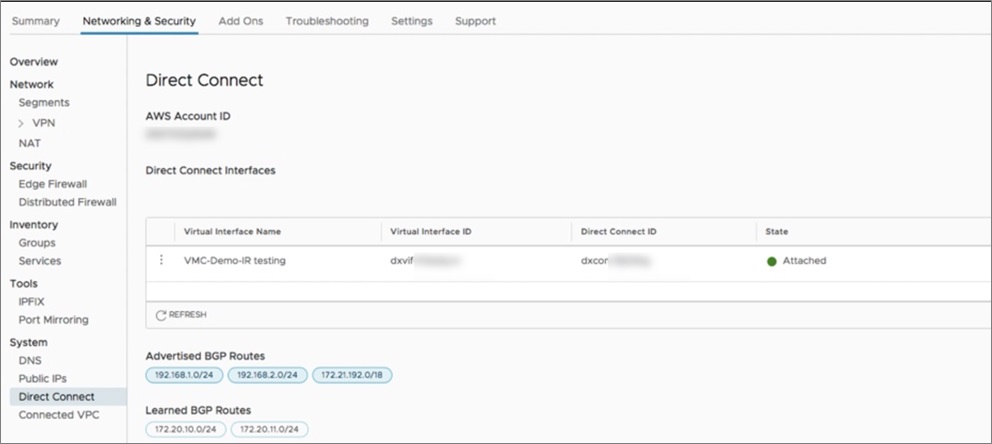
Figure 3 – AWS Direct Connect advertised and learned BGP routes.
This feature is currently available in all VMware Cloud on AWS Regions. Pricing remains similar to the AWS pricing model, where the account owner of the Direct Connect connection pays for the connection charges/hour, and the account that hosts the VIF pays for data egress charges.
In this case, customers pay for the port charges and VMware pays for the egress data charges, which is then billed back to the customer. Note that Direct Connect Gateway is not supported yet with VMware Cloud on AWS.
Conclusion
The new VMware Cloud on AWS SDDCs backed by NSX-T networking provides full routing support for infrastructure (underlay) and overlay networks over a single Virtual Private Interface. This model simplifies the routing requirements between SDDC and on-premises environments using BGP routing without the need for VPN tunnels, unless if encryption is required.
AWS Direct Connect provides connection speeds of 1Gbps and 10Gbps. Speeds of 50Mbps, 100Mbps, 200Mbps, 300Mbps, 400Mbps, and 500Mbps can be ordered from APN Partners supporting AWS Direct Connect.
Customers who are architecting for data center extension, disaster recovery, or building hybrid environments can use AWS Direct Connect to achieve the private connectivity to their VMware Cloud on AWS SDDC.