AWS Developer Tools Blog
Why and how you should use AWS SDK for JavaScript (v3) on Node.js 18
The Node.js 18.x runtime was promoted to Active Long Term Support (LTS) on October 25th, 2022, and is now available in AWS Lambda. The AWS SDK for JavaScript (v3) is included by default in AWS Lambda Node.js 18 runtime as a convenience for developers building simpler functions. You can read about features in Node.js 18 […]
Improvements to the connection experience in the AWS Toolkit for VS Code
AWS Toolkit for VS Code has shipped improvements that help customers setting up a new machine without AWS credentials files (typically in “~/.aws/”—the “.aws” directory of the machine home folder). Setting up credentials is the first step to working with AWS cloud resources, but it’s not a frequent task, so one often needs to read […]
New: AWS CLI v2 installers available over IPv6 connections
We are excited to announce that the AWS Command Line Interface (AWS CLI) v2 is now available for download over IPv6 connections. Customers can now download the AWS CLI v2 installers for IPv6-only environments, such as Amazon EC2 running inside an IPv6-only Amazon Virtual Private Cloud. Previously, the AWS CLI v2 installation packages were only […]
Introducing Smithy IDL 2.0
The AWS Smithy team is happy to announce the 2.0 release of the Smithy Interface Definition Language (IDL). This release focuses on improving the developer experience of authoring Smithy models and using code generated from Smithy models. It contains numerous new features, such as reduced nulls and optional types in generated code, custom default values, […]
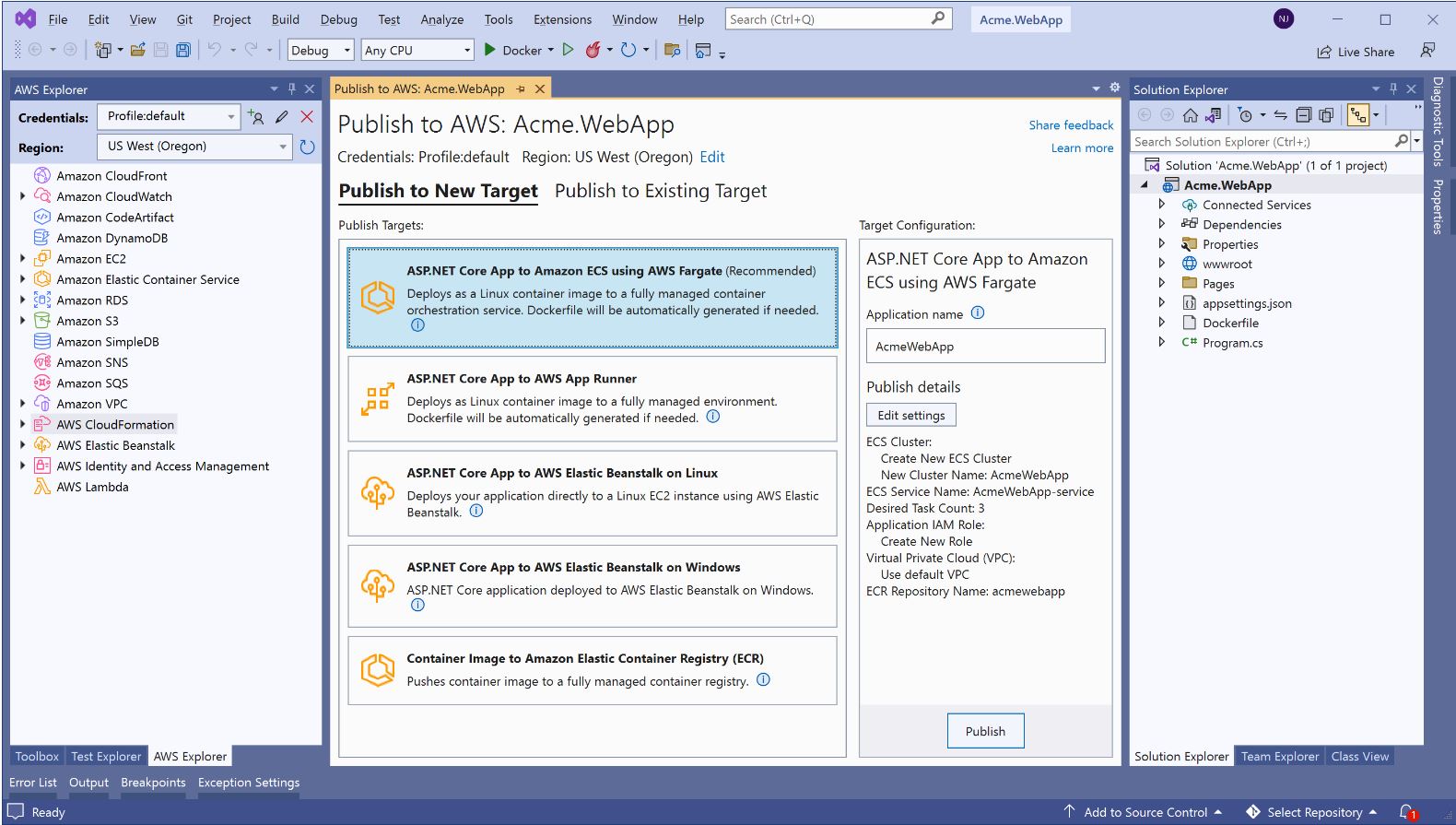
AWS announces a streamlined deployment experience for .NET applications
We are happy to announce the general availability of a new deployment experience in both the Visual Studio and the .NET CLI. This follows the preview announcement from last year. The new deployment experience focuses on the type of application you want to deploy instead of individual AWS services by providing intelligent compute recommendations. You […]
Using Amazon Corretto (OpenJDK) for lean, fast, and efficient AWS Lambda Applications
Using Amazon Corretto (OpenJDK) for lean, fast, and efficient AWS Lambda By Guest Blogger Adam Bien In this post, I will discuss how you can launch large, monolithic applications on top of AWS Lambda, and I’ll show that they perform well and are cost effective. You’ll learn that the same application you develop for Lambda […]
Version 1 of the AWS Cloud Development Kit (AWS CDK) is now in maintenance mode
The AWS Cloud Development Kit (AWS CDK) version 1 (v1) for JavaScript, TypeScript, Java, Python, .NET and Go is now in maintenance mode. AWS CDK v1 is no longer receiving higher-level “L2” construct updates for new or existing services. It will continue receiving updates for new and updated resource level “L1” constructs, critical bug fixes, and security updates only. We […]
Announcing the end of support for Node.js 12.x in the AWS SDK for JavaScript (v3)
This blog post is about AWS SDK for JavaScript (v3), and not AWS Lambda. As of Oct 2022, Lambda is planning Node.js 12.x deprecation on Mar 31, 2023. If your code uses Lambda Provided SDK, it’s v2 which continues to support Node.js 12.x Starting November 1, 2022, AWS SDK For JavaScript (v3) will no longer […]
Tuning Apache Kafka and Confluent Platform for Graviton2 using Amazon Corretto
Tuning Apache Kafka and Confluent Platform for Graviton2 using Amazon Corretto By Guest Blogger Liz Fong-Jones, Principal Developer Advocate, Honeycomb.io Background Honeycomb is a leading observability platform used by high-performance engineering teams to quickly visualize, analyze, and improve cloud application quality and performance. We utilize the OpenTelemetry standard to ingest data from our clients, including […]
Using atomic counters in the Enhanced DynamoDB AWS SDK for Java 2.x client
We are pleased to announce that users of the enhanced client for Amazon DynamoDB in AWS SDK for Java 2.x can now enable atomic counters, as well as add custom DynamoDB update expressions through the enhanced client extension framework. Customers have told us that they want improved performance and consistency when updating table records. The […]