AWS Developer Tools Blog
End-of-support for Windows PowerShell 2
Following the end of support of Windows Server 2008 R2, in March 2020 we announced that we require Windows PowerShell 3.0+ and .NET Framework 4.5+ as prerequisite for all new releases of AWSPowerShell. As of June 1st, 2020 we no longer release new AWSPowerShell versions compatible with Windows PowerShell 2. The existing versions of AWSPowerShell […]
AWS SDK for C++ Version 1.8 is Now Generally Available
We’re happy to share that version 1.8 of AWS SDK for C++ is now generally available. AWS SDK for C++ provides a modern C++ (version C++ 11 or later) interface for Amazon Web Services (AWS). It is performant and fully functioning with low- and high-level SDKs, and minimizes dependencies. The AWS SDK for C++ also […]
Centralize Amazon CloudWatch Logs using AWS CDK
September 8, 2021: Amazon Elasticsearch Service has been renamed to Amazon OpenSearch Service. See details. One of the most common use cases that customers try to implement is to centralize various types of logs in their AWS infrastructure so that these logs can be utilized for security, monitoring or analytics purposes. Centralizing AWS services logs […]
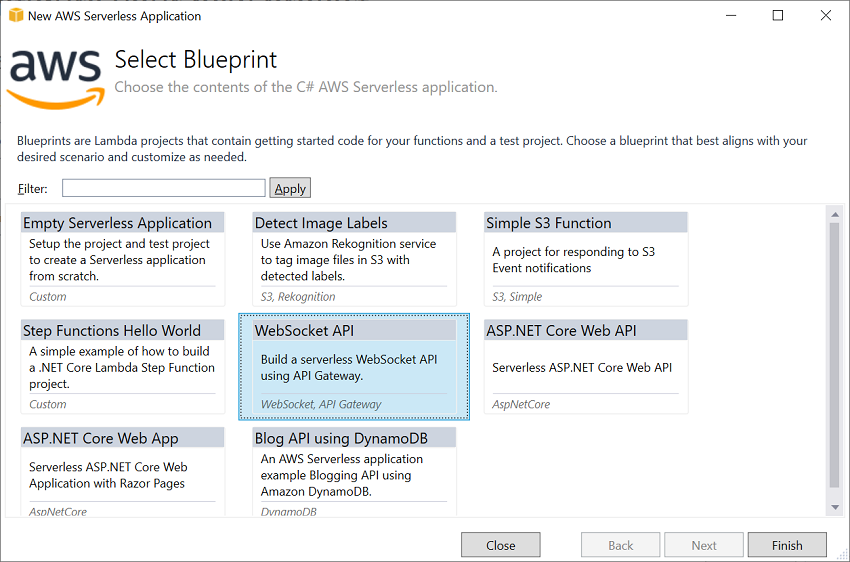
10 years of building .NET on AWS
This week is my 10 year anniversary at AWS and what a ride it has been. Somewhere along the road they gave me the keys to publish blog posts so I thought I would take over for a bit and look back on my journey at AWS. My journey also maps very closely with .NET's […]
AWS CLI v2 now available for Linux ARM
With the release of 2.0.15 of the AWS CLI v2, we are excited to announce the availability of aarch64 builds of the AWS CLI v2. This launch includes a new Linux ARM installer to add to the current AWS CLI v2 installation mechanisms: Linux x86 installer MacOS PKG installer Windows MSI installer Docker image The […]
Announcing end of support for .NET Standard 1.3 in AWS SDK for .NET
Microsoft announced the end of support for .NET Core 1.0 and 1.1 platforms on June 27th, 2019. Given that the .NET Standard 1.3 target of the AWS SDK for .NET is only used for .NET Core 1.0 and 1.1 platforms, we will be removing the .NET Standard 1.3 target in AWS SDK for .NET, and […]
Provision AWS infrastructure using Terraform (By HashiCorp): an example of web application logging customer data
Many web and mobile applications can make use of AWS services and infrastructure to log or ingest data from customer actions and behaviors on the websites or mobile apps, to provide recommendations for better user experience. There are several ‘infrastructure as code’ frameworks available today, to help customers define their infrastructure, such as the AWS […]
Orchestrating an application process with AWS Batch using AWS CDK
In many real work applications, you can use custom Docker images with AWS Batch and AWS Cloud Development Kit(CDK) to execute complex jobs efficiently. AWS CDK is an open source software development framework to model and provision your cloud application resources using familiar programming languages, including TypeScript, JavaScript, Python, C# and Java. For the solution […]
Introducing .NET Core Support for AWS Amplify Backend Functions
Earlier this month, the AWS Amplify team announced support for backend functions that use runtimes beyond the existing support for Node.js. With this new feature, customers can now write backend functions using Python, Java, Go, and .NET Core to handle requests from their REST or GraphQL APIs, triggers from services like Amazon DynamoDB and Amazon […]
One Month Update to .NET Core 3.1 Lambda
One Month Update to .NET Core 3.1 Lambda About one month ago we released the .NET Core 3.1 Lambda runtime. Since then we have seen a lot excitement for creating new .NET Core 3.1 Lambda functions or porting existing Lambda functions to .NET Core 3.1. We have also received some great feedback and as a […]