AWS Partner Network (APN) Blog
Integrating Microsoft Active Directory with AWS Certificate Manager Private CA Using Secardeo certEP
By Zach Miller, Sr. Security Specialist SA – AWS
 |
| Secardeo |
 |
Many organizations utilize Microsoft Active Directory (AD) for authentication and authorization, including over 90% of Global Fortune 1000 companies.
Many of these same organizations also require the use of cryptographic certificates to identify devices on their network, authenticate users and devices, or cryptographically sign and encrypt sensitive information.
You can enable automatic distribution of certificates to domain-joined devices using a public key infrastructure and Active Directory Certificate Services; this process is referred to as certificate auto-enrollment.
Deploying and maintaining an on-premises public key infrastructure (PKI) for Active Directory is often time-consuming and expensive due to the criticality of the system and skillsets required to manage it.
Also, organizations have been left with little choice: if you want to automatically enroll certificates in Active Directory, you must use a Microsoft Certificate Authority (CA).
In this post, I will highlight a solution that provides additional options and flexibility for organizations that want to use cryptographic certificates with AD, without being required to manage the underlying certificate authority infrastructure or the hardware security modules (HSMs) to store certificates and private keys.
This solution harnesses the power of native Amazon Web Services (AWS) technologies to create a secure, scalable, highly-available certificate enrollment solution.
There are several ways to deploy Active Directory on AWS, but this solution focuses on creating the most scalable option requiring the least amount of undifferentiated heavy lifting. We’ll be using AWS Managed Microsoft AD, Amazon Relational Database Service (Amazon RDS), and AWS Certificate Manager Private Certificate Authority (ACM Private CA).
For certificate auto-enrollment, we’ll be using certEP (Certificate Enrollment Proxy) by Secardeo, an AWS Partner with a qualified software offering. Secardeo offers pioneering solutions for a full lifecycle of automation for digital certificates.
Why is Certificate Enrollment Important?
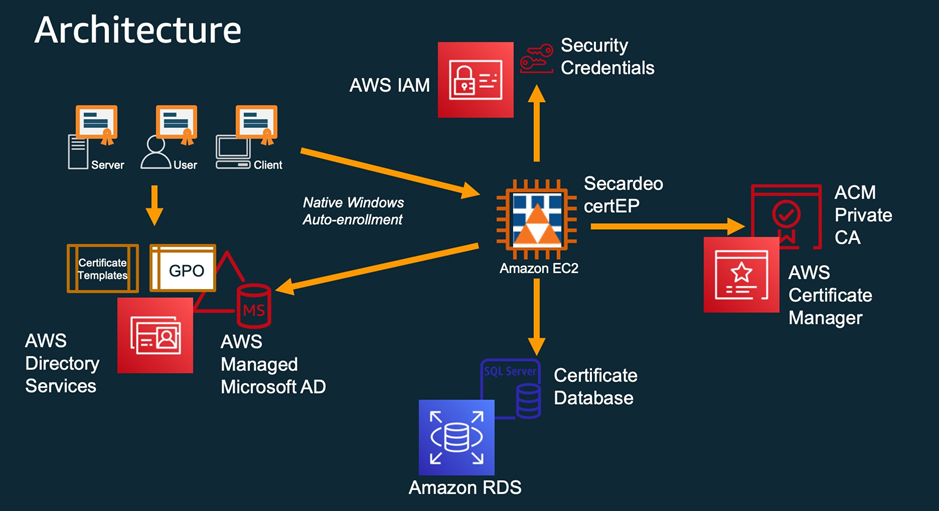
The following diagram highlights how the services mentioned above work together to facilitate certificate requests from domain-joined devices and users in Active Directory.
Figure 1 – Architecture overview.
Organizations have many different use cases for cryptographic certificates, such as enabling encryption of emails, file systems, or individual files, and authenticating devices (like corporate laptops or mobile devices) to the network. A public key infrastructure is necessary to distribute and manage these certificates, and many businesses face operational challenges that prevent them from running an on-premises PKI.
Managing a PKI can be expensive and time-consuming. It requires several layers of expertise, including managing hardware security modules to store private keys; a certificate authority able to facilitate certificate requests; and a mechanism for revoking certificates that have been exposed or are no longer in use. For most customers, these are skillsets that don’t directly relate to their primary business.
However, ACM Private CA greatly reduces the management overhead associated with running a certificate authority, as AWS manages the health, durability, and availability of your CAs and the backing HSMs.
ACM Private CA securely stores your CA private keys in a FIPS 140-2 validated HSM that is managed by AWS. ACM PCA also supports certificate revocation lists (CRLs) and Online Certificate Status Protocol (OCSP) for managing revocation.
While ACM Private CA is unable to natively accept certificate requests from domain resources with Microsoft Active Directory Certificate Services, certEP can act as a proxy for certificate requests, translating the request so ACM Private CA can generate Windows domain certificates.
Solution Overview
In the sections below, I will highlight the components that make up this solution, as well as demonstrate how to deploy these components to achieve high availability.
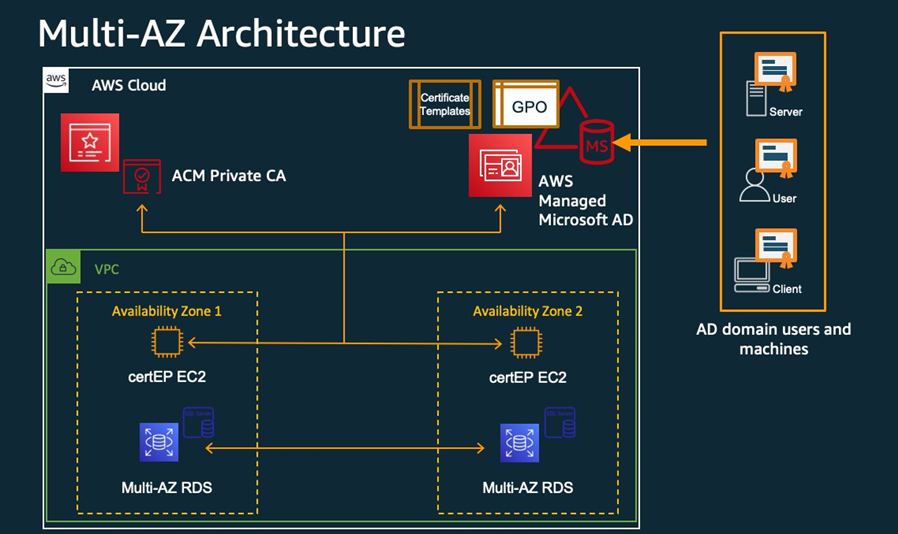
Refer to the diagram below for a visualization of the multi-Availability Zone (AZ) architecture used in this post.
Figure 2 – Multi-Availability Zone architecture.
Secardeo certEP
Secardeo’s Certificate Enrollment Proxy (certEP) supports manual and automatic certificate enrollment for users and computers on a Windows domain, as well as for network and mobile devices.
Secardeo certEP acts as a proxy for certificate enrollment requests, based on standard or custom Windows certificate templates configured and enabled by your organization. certEP runs on Amazon Elastic Compute Cloud (Amazon EC2) instances in your virtual private cloud (VPC), and can be easily launched from Secardeo’s Amazon Machine Image (AMI) from AWS Marketplace.
Using this solution, when new devices join your Windows domain they can automatically be provisioned cryptographic certificates to be used for encryption and decryption, authentication, or machine identification.
This procedure uses standard Active Directory configurations for auto-enrollment and doesn’t require the distribution of software to any client devices (such as employee laptops or corporate servers).
The enrollment process is performed in the same way you would configure auto-enrollment in any AD environment: new devices joining the domain use group policy to determine the certificate enrollment server for user or machine certificates. In this case, the enrollment server(s) is the certEP instance.
When used in conjunction with AWS Certificate Manager Private CA, certEP can facilitate certificate requests to your private CA(s) hosted on AWS, enabling use of a non-Microsoft CA with Active Directory certificates.
Since ACM Private CA cannot natively accept certificate requests using Active Directory Certificate services, certEP contextualizes these requests and works with ACM Private CA to request a certificate. It adds the appropriate metadata required by Active Directory, and distributes the certificate directly to the requesting device.
Secardeo certEP also supports additional certificate types (such as mobile) and other features to streamline certificate management. This includes certificate private key archival, additional certificate template attributes, and request blocking. Please refer to Secardeo’s product page for more information on additional features.
ACM Private CA
AWS Certificate Manager Private Certificate Authority (ACM Private CA) enables the creation and management of private certificate authorities without the significant upfront investment or maintenance costs associated with operating an on-premises CA.
Your private CAs can issue X.509 certificates in order to encrypt communications with TLS or to enable authentication of users and computers on your network. ACM Private CA supports customizable certificate templates that are used by certEP and Active Directory.
Amazon RDS
Amazon Relational Database Service (Amazon RDS) makes it easy to set up, operate, and scale a relational database in the cloud. It provides cost-efficient and resizable capacity while automating time-consuming administration tasks such as hardware provisioning, database setup, patching and backups.
While Amazon RDS provides many options for database management systems, for the purposes of this post, we’ll utilize Microsoft SQL Server on RDS. This is recommended by Secardeo for best compatibility with their certEP solution.
Using Amazon RDS, certEP can store certificate metadata independently while running across multiple EC2 instances for high availability. RDS hosts the backing database for certEP, where information about certificate enrollment requests and certificate templates will be stored. This database can also be configured to securely store (encrypted/wrapped) certificate private keys.
AWS Managed Microsoft AD
AWS Directory Service lets you run Microsoft Active Directory (AD) as a managed service, referred to as AWS Managed Microsoft AD. Host monitoring and recovery, data replication, snapshots, and software updates are automatically configured and managed for you.
AWS Directory Service makes it easy to set up and run directories on the AWS Cloud, or connect your AWS resources with an existing on-premises Microsoft Active Directory. In this post, we’ll be creating a brand-new directory on AWS, but the process will be much the same for existing active directory environments.
High Availability Configuration
ACM Private CA Config
ACM Private CA is a highly available, fully managed service provided by AWS. The hardware security modules used to back the certificate authorities are highly scalable and able to facilitate a large number of requests. However, it’s up to customers to design their own CA hierarchy that will meet their requirements.
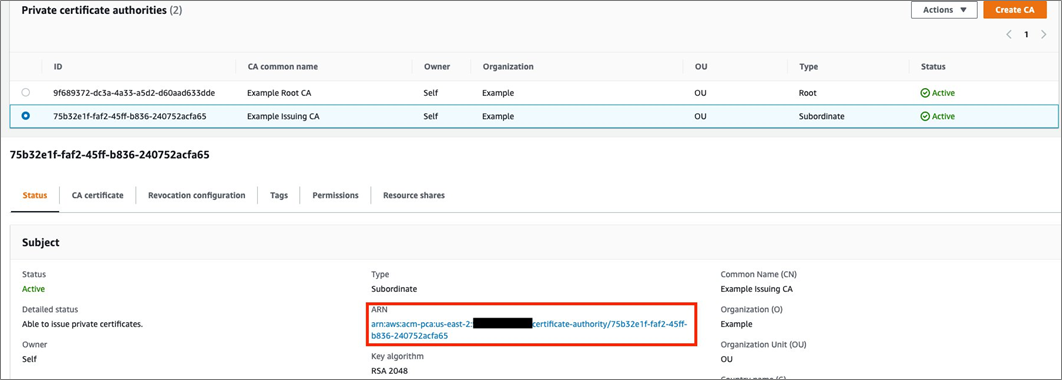
AWS recommends utilizing an issuing CA to distribute certificates to end entities, with the issuing CA being signed by your organization’s Root CA certificate. Root CAs should never issue certificates directly in production environments. Here is some more information about designing a CA hierarchy.
Create a set of certificate authorities based on your requirements, and take note of your issuing CA’s Amazon Resource Name (ARN), as this will be needed later to configure the certEP enrollment proxy to communicate with ACM Private CA.
Figure 3 – Private CA hierarchy.
You will also need to create an AWS Identity and Access Management (IAM) user that has permissions to access ACM Private CA. This post will utilize an IAM user group with the AWS managed policy AWSCertificateManagerFullAccess, as indicated in certEP’s installation manual.
Take note of the Access Key ID and Secret Access Key for the user(s) you created in this group; they will be needed later.
Amazon RDS Config (Multi-AZ)
Amazon RDS is a managed database service that enables customers to focus on application development by reducing management overhead. AWS continuously monitors your clusters to keep your workloads running with self-healing storage and automated scaling.
To achieve high availability for our certificate management solution, we chose a multi-Availability Zone RDS setup that has a replica in a second Availability Zone (AZ). Even in the event of a full AZ outage, certificate information stored in the RDS instance will be accessible to the certificate enrollment servers.
Navigate to the RDS console and select Create a Database. Ensure you select MS SQL Server in the Engine Options section, and select the appropriate version for your needs. In this post, we are using the Enterprise Edition of MS SQL Server.
Under multi-AZ Deployment, select Yes to ensure a mirrored instance is created in a second AZ. Select the appropriate options for your workload, following this guidance.
Continue through the database setup and be sure to take note of the database’s listener endpoint; this will be used to configure certEP’s access to the database. You will also need the master username and master password you configured during database creation.
AWS Managed AD Config
Navigate to the AWS Directory Service console, and select Set Up Directory. For this walkthrough, we’ll use AWS Managed Microsoft AD – Enterprise Edition, but Standard and Enterprise Edition are both compatible with the solution. Refer to the AWS documentation for the configuration details and considerations to set up AWS Managed Microsoft AD.
The certEP software will need to run on domain-joined EC2 instances in the domain you just created. More information on how to seamlessly join an EC2 instance to your domain can be found in the AWS documentation.
Secardeo certEP Config
Secardeo certEP makes it easy to achieve high availability by utilizing the native capabilities of Active Directory certificate enrollment. AD administrators can configure multiple enrollment servers, and if one enrollment server can’t be reached, the device requesting a certificate will simply go to the next enrollment server on the list.
Therefore, two (or more) certEP proxies can run on separate EC2 instances simultaneously, and end user devices will randomly select a server for enrollment, ensuring requests are load-balanced between all the enrollment servers.
To deploy the certEP enrollment server, launch an EC2 instance from Secardeo’s certEP Amazon Machine Image (AMI) on AWS Marketplace. This EC2 instance must be joined to the domain you created in the previous section.
When you first login to the new EC2 instance, the certEP software will automatically start and present a window where you can configure the product.
Refer to Secardeo’s deployment guide for detailed setup information. These guides will be located on the desktop of the EC2 instance launched from Secardeo’s certEP AMI.
You will need some information you noted in the previous steps:
- ARN of ACM Private CA Issuing CA to issue end-entity certificates.
- IAM user access key ID and secret access key for authentication to ACM Private CA.
- Database listener endpoint ARN (Amazon RDS).
- Database master username and password for authentication.
The basic steps to configure certEP are outlined below; please refer to Secardeo certEP’s deployment guide for more information.
Database Configuration
- In the database section, select the MS SQL Server DB driver from the drop-down.
- Enter the database listener endpoint ARN and port in the Server and Port boxes.
- Type the database instance name in the Database box or enter a new instance name to initialize.
- Enter the master username and password or check the box for Use Windows Authentication (if this enabled on your database).
- Leave the other options as default, or set them according to your standard database requirements and practices.
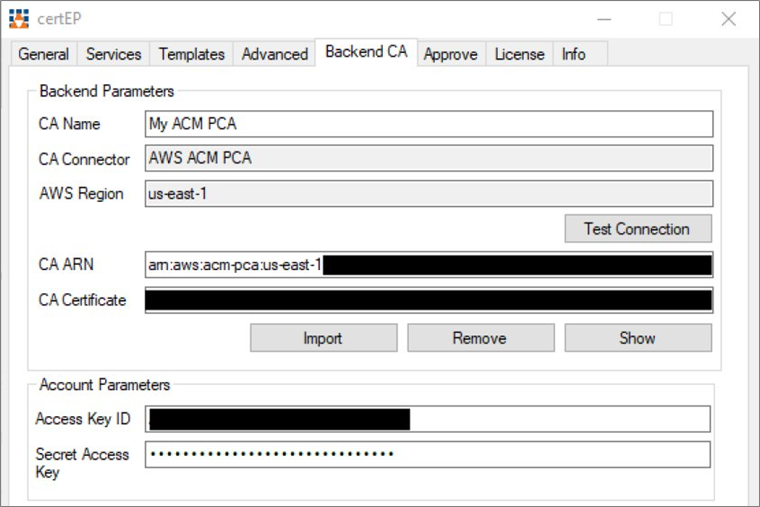
Figure 4 – Secardeo certEP configuration.
Private CA Integration
- Navigate to the backend CA section of the configuration window.
- Enter the CA ARN for your issuing CA (not the root CA you created) in the appropriate box.
- Enter the Access Key ID and Secret Access Key for the IAM user you configured with access to ACM Private CA.
- Select Test Connection:
- If this is successful, select Import and the other boxes will be automatically filled in with the appropriate information gathered from the ACM Private CA service.
- If the connection test is not successful, ensure the IAM user information you entered has appropriate permissions to interact with the ACM PCA service.
Refer to Secardeo’s documentation and Microsoft’s ADCS documentation to enable the appropriate certificate templates for auto-enrollment.
You can configure templates and auto-enrollment in exactly the same way you would any other Active Directory environment. certEP collects template information from AD and helps populate the appropriate information in certificate enrollment requests to ACM Private CA.
You should now have a fully functional, highly-available certificate auto-enrollment solution for your Microsoft AD environment. In this model, you are not locked in to using Microsoft CA, and you are not required to manage your own HSMs or sacrifice security by storing your CA private keys outside a FIPS 140-2 validated hardware security module.
Conclusion
In this post, I reviewed the need for certificate management in Active Directory (AD) environments, and how customers can harness the power and flexibility of AWS to reduce costs, offload maintenance tasks, and ensure availability of certificates to their end users.
I also walked through the components and basic setup to achieve a highly available public key infrastructure (PKI) in an AWS Managed Microsoft AD domain.
Proper certificate management helps organizations secure their data, authenticate users, and identify devices on their networks. Setting up this highly available certificate management environment ensures users, devices, and servers can always acquire the certificates they need—all without introducing unnecessary operational overhead.
Using Secardeo’s certEP (Certificate Enrollment Proxy) enables customers running AD on AWS (and on premises) to take advantage of the scalable and fully managed nature of ACM Private CA, without sacrificing security or requiring extensive experience managing keys and certificates with hardware security modules.
Secardeo – AWS Partner Spotlight
Secardeo is an AWS Partner that offers pioneering solutions for a full lifecycle of automation for digital certificates.
Contact Secardeo | Partner Overview | AWS Marketplace
*Already worked with Secardeo? Rate the Partner
*To review an AWS Partner, you must be a customer that has worked with them directly on a project.