AWS Compute Blog
Adding approval notifications to EC2 Image Builder before sharing AMIs
This blog post is written by, Glenn Chia Jin Wee, Associate Cloud Architect, and Randall Han, Professional Services.
You may be required to manually validate the Amazon Machine Image (AMI) built from an Amazon Elastic Compute Cloud (Amazon EC2) Image Builder pipeline before sharing this AMI to other AWS accounts or to an AWS organization. Currently, Image Builder provides an end-to-end pipeline that automatically shares AMIs after they’ve been built.
In this post, we will walk through the steps to enable approval notifications before AMIs are shared with other AWS accounts. Image Builder supports automated image testing using test components. The recommended best practice is to automate test steps, however situations can arise where test steps become either challenging to automate or internal compliance policies mandate manual checks be conducted prior to distributing images. In such situations, having a manual approval step is useful if you would like to verify the AMI configuration before it is shared to other AWS accounts or an AWS Organization. A manual approval step reduces the potential for sharing an incorrectly configured AMI with other teams which can lead to downstream issues. This solution sends an email with a link to approve or reject the AMI. Users approve the AMI after they’ve verified that it is built according to specifications. Upon approving the AMI, the solution automatically shares it with the specified AWS accounts.
Overview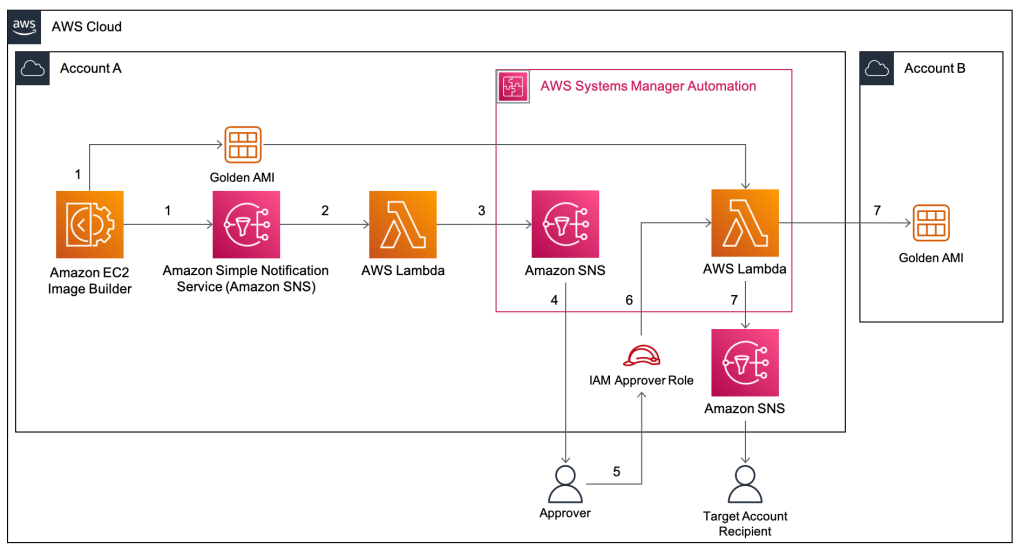
- In this solution, an Image Builder Pipeline is run that builds a Golden AMI in Account A. After the AMI is built, Image Builder publishes data about the AMI to an Amazon Simple Notification Service (Amazon SNS)
- The SNS Topic passes the data to an AWS Lambda function that subscribes to it.
- The Lambda function that subscribes to this topic retrieves the data, formats it, and then starts an SSM Automation, passing it the AMI Name and ID.
- The first step of the SSM Automation is a manual approval step. The SSM Automation first publishes to an SNS Topic that has an email subscription with the Approver’s email. The approver will receive the email with a URL that they can click to approve the step.
- The approval step defines a specific AWS Identity and Access Management (IAM) Role as an approver. This role has the minimum required permissions to approve the manual approval step. After performing manual tests on the Golden AMI, the Approver principal will assume this role.
- After assuming this role, the approver will click on the approval link that was sent via email. After approving the step, an AWS Lambda Function is triggered.
- This Lambda Function shares the Golden AMI with Account B and sends an email notifying the Target Account Recipients that the AMI has been shared.
Prerequisites
For this walkthrough, you will need the following:
- Two AWS accounts – one to host the solution resources, and the second which receives the shared Golden AMI.
- In the account that hosts the solution, prepare an AWS Identity and Access Management (IAM) principal with the sts:AssumeRole permission. This principal must assume the IAM Role that is listed as an approver in the Systems Manager approval step. The ARN of this IAM principal is used in the AWS CloudFormation Approver parameter, This ARN is added to the trust policy of approval IAM Role.
- In addition, in the account hosting the solution, ensure that the IAM principal deploying the CloudFormation template has the required permissions to create the resources in the stack.
- A new Amazon Virtual Private Cloud (Amazon VPC) will be created from the stack. Make sure that you have fewer than five VPCs in the selected Region.
Walkthrough
In this section, we will guide you through the steps required to deploy the Image Builder solution. The solution is deployed with CloudFormation.
In this scenario, we deploy the solution within the approver’s account. The approval email will be sent to a predefined email address for manual approval, before the newly created AMI is shared to target accounts.
The approver first assumes the approval IAM Role and then selects the approval link. This leads to the Systems Manager approval page. Upon approval, an email notification will be sent to the predefined target account email address, notifying the relevant stakeholders that the AMI has been successfully shared.
The high-level steps we will follow are:
- In Account A, deploy the provided AWS CloudFormation template. This includes an example Image Builder Pipeline, Amazon SNS topics, Lambda functions, and an SSM Automation Document.
- Approve the SNS subscription from your supplied email address.
- Run the pipeline from the Amazon EC2 Image Builder Console.
- [Optional] To conduct manual tests, launch an Amazon EC2 instance from the built AMI after the pipeline runs.
- An email will be sent to you with options to approve or reject the step. Ensure that you have assumed the IAM Role that is the approver before clicking the approval link that leads to the SSM console approval page.
- Upon approving the step, an AWS Lambda function shares the AMI to the Account B and also sends an email to the target account email recipients notifying them that the AMI has been shared.
- Log in to Account B and verify that the AMI has been shared.
Step 1: Deploy the AWS CloudFormation template
1. The CloudFormation template, template.yaml that deploys the solution can also found at this GitHub repository. Follow the instructions at the repository to deploy the stack.
Step 2: Verify your email address
- After running the deployment, you will receive an email prompting you to confirm the Subscription at the approver email address. Choose Confirm subscription.
- This leads to the following screen, which shows that your subscription is confirmed.
- Repeat the previous 2 steps for the target email address.
Step 3: Run the pipeline from the Image Builder console
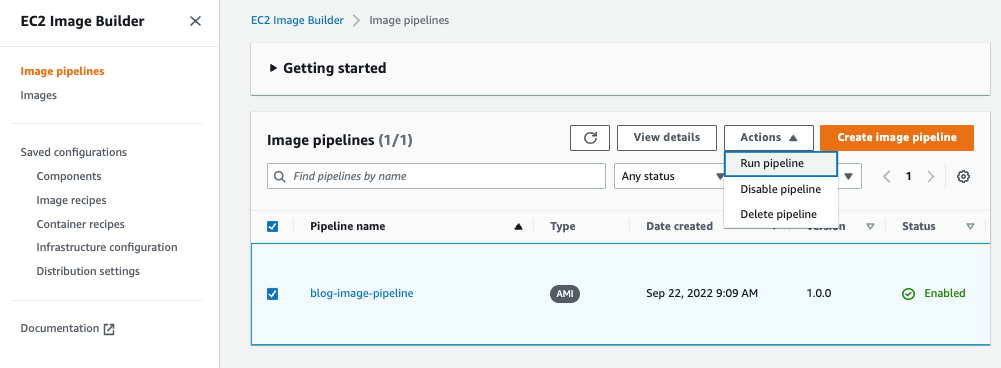
- In the Image Builder console, under Image pipelines, select the checkbox next to the Pipeline created, choose Actions, and select Run pipeline.
Note: The pipeline takes approximately 20 – 30 minutes to complete.
Step 4: [Optional] Launch an Amazon EC2 instance from the built AMI
If you have a requirement to manually validate the AMI before sharing it with other accounts or to the AWS organization an approver will launch an Amazon EC2 instance from the built AMI and conduct manual tests on the EC2 instance to make sure it is functional.
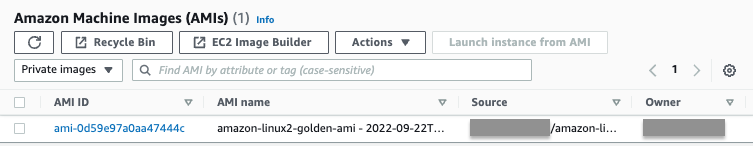
- In the Amazon EC2 console, under Images, choose AMIs. Validate that the AMI is created.
- Follow AWS docs: Launching an EC2 instances from a custom AMI for steps on how to launch an Amazon EC2 instance from the AMI.
Step 5: Select the approval URL in the email sent
- When the pipeline is run successfully, you will receive another email with a URL to approve the AMI.
- Before clicking on the Approve link, you must assume the IAM Role that is set as an approver for the Systems Manager step.
- In the CloudFormation console, choose the stack that was deployed.
4. Choose Outputs and copy the IAM Role name.
5. While logged in as the IAM Principal that has permissions to assume the approval IAM Role, follow the instructions at AWS IAM documentation for switching a role using the console to assume the approval role.
In the Switch Role page, in Role paste the name of the IAM Role that you copied in the previous step.
Note: This IAM Role was deployed with minimum permissions. Hence, seeing warning messages in the console is expected after assuming this role.
6. Now in the approval email, select the Approve URL. This leads to the Systems Manager console. Choose Submit.
7. After approving the manual step, the second step is executed, which shares the AMI to the target account.
Step 6: Verify that the AMI is shared to Account B
- Log in to Account B.
- In the Amazon EC2 console, under Images, choose AMIs. Then, in the dropdown, choose Private images. Validate that the AMI is shared.
- Verify that a success email notification was sent to the target account email address provided.
Clean up
This section provides the necessary information for deleting various resources created as part of this post.
- Deregister the AMIs that were created and shared.
- Log in to Account A and follow the steps at AWS documentation: Deregister your Linux AMI.
- Delete the CloudFormation stack. For instructions, refer to Deleting a stack on the AWS CloudFormation console.
Conclusion
In this post, we explained how to enable approval notifications for an Image Builder pipeline before AMIs are shared to other accounts. This solution can be extended to share to more than one AWS account or even to an AWS organization. With this solution, you will be notified when new golden images are created, allowing you to verify the accuracy of their configuration before sharing them to for wider use. This reduces the possibility of sharing AMIs with misconfigurations that the written tests may not have identified.
We invite you to experiment with different AMIs created using Image Builder, and with different Image Builder components. Check out this GitHub repository for various examples that use Image Builder. Also check out this blog on Image builder integrations with EC2 Auto Scaling Instance Refresh. Let us know your questions and findings in the comments, and have fun!