AWS Compliance
Learn more about our compliance offerings and why we serve our customers best
Inherit the most comprehensive compliance controls with AWS. AWS supports 143 security standards and compliance certifications, including PCI-DSS, HIPAA/HITECH, FedRAMP, GDPR, FIPS 140-2, and NIST 800-171, helping customers satisfy compliance requirements around the globe.
Benefits of Compliance on AWS
Learn more about the certifications, regulations, and frameworks AWS aligns with to support customer compliance on our Compliance Programs webpage.
Third-party validation for 1,000s of global requirements
AWS regularly achieves third-party validation for thousands of global compliance requirements that we continually monitor to help you meet security and compliance standards for finance, retail, healthcare, government, and beyond.
Inherit the latest security controls AWS uses on its own infrastructure
These controls strengthen your own compliance and certification programs, while also receiving access to tools you can use to reduce your cost and time to run your own specific security assurance requirements.
Streamline and automate compliance
Traditional assurance methods become challenging with scale. Reduce risk and enable scale by using our activity monitoring services that detect configuration changes and security events across your system, even integrating our services with your existing solutions to simplify your operations and compliance reporting.
Automated Compliance Reporting
Get on-demand access to more than 2,500 security controls by using AWS Artifact, our automated compliance reporting tool available in the AWS Management Console.
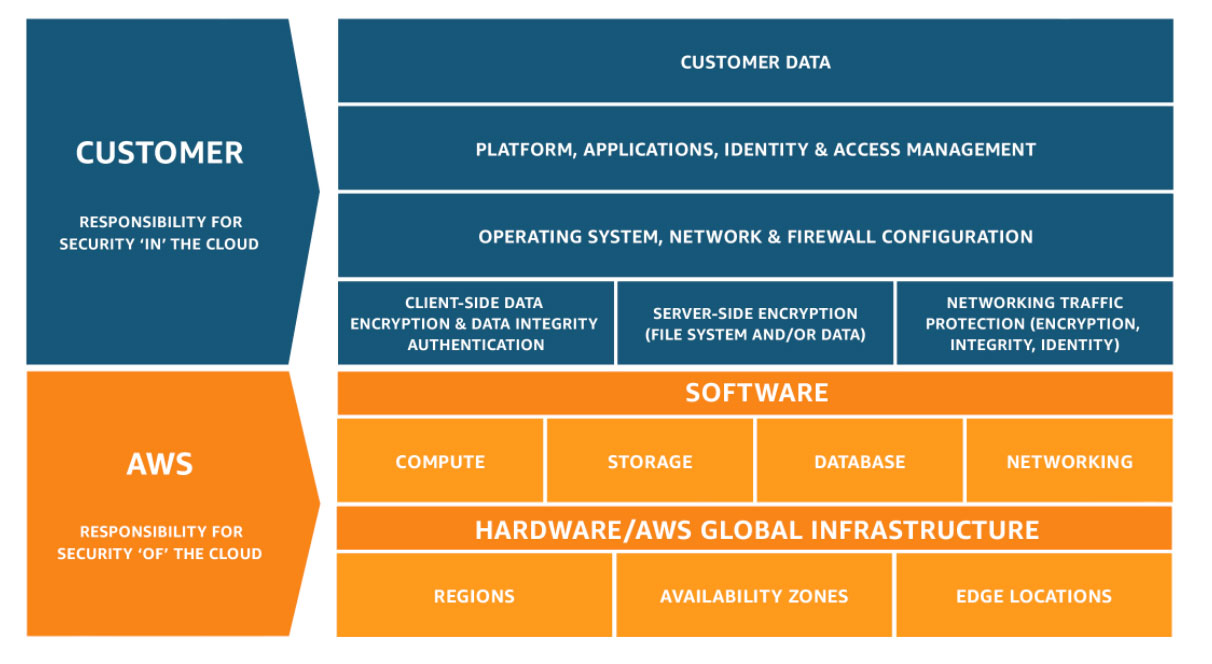
Compliance is a Shared Responsibility
Security and Compliance is a shared responsibility between AWS and the customer. This shared model can help relieve the customer’s operational burden as AWS operates, manages and controls the components from the host operating system and virtualization layer down to the physical security of the facilities in which the service operates. The customer assumes responsibility and management of the guest operating system (including updates and security patches), other associated application software as well as the configuration of the AWS provided security group firewall.
Visit Shared Responsibility Model to learn more.
Meeting Your Compliance Goals on AWS
AWS Audit Manager
Continuously audit your AWS usage to simplify how you assess risk and compliance with regulations and industry standards
Amazon GuardDuty
Protect your AWS accounts and workloads with intelligent threat detection and continuous monitoring
AWS Artifact
No cost, self-service portal for on-demand access to AWS’ compliance reports

Amazon Data Centers
Learn about our security approach to protect the data of millions of active monthly customers
Customers in Regulated Industries
For security and compliance, customers choose AWS. To see more examples of customer success stories, visit our Testimonials webpage.
Data Privacy
AWS gives customers ownership and control over their customer content by design through simple, but powerful tools that allow customers to determine where their customer content will be stored, secure their customer content in transit or at rest, and manage access to AWS services and resources.
Visit our Data Privacy FAQ for more details.
Information Requests
We know customers care deeply about privacy and data security, and we optimize our work to get these issues right for customers.
Learn more on our Information Requests webpage.
Compliance Resources
AWS provides information about its compliance programs to help customers incorporate AWS controls into their governance framework. This information can assist customers in documenting a complete control and governance framework with AWS included as an important part of that framework.
Visit our Compliance Resources or Compliance FAQ to learn more.






